Cisco XDR served as a Tier-1 & 2 detection and response platform for Cisco engineers and analysts working in the Black Hat Europe 2025 NOC/SOC. The NOC leadership enabled Cisco and other partners to introduce additional pre-approved software and hardware solutions, enhancing our internal efficiency and expanding our visibility capabilities; however, Cisco is not the official provider for Extended Detection & Response, Security Event and Incident Management, Firewall, Network Detection & Response or Collaboration.
The main goal of the NOC/SOC was to ensure secure and reliable network operations. As the Official Security Cloud Provider to Black Hat, we integrated Cisco XDR with Splunk Enterprise Security and Splunk Attack Analyzer, Secure Malware Analytics, Cisco Secure Firepower Intrusion Detection System, Cisco Secure Access, and third-party intelligence sources, it enabled real-time correlation and analysis to quickly identify potential security risks and incidents. We also ingested logs into Splunk from our partner Palo Alto Networks and Corelight, correlating in Incidents via Cisco XDR. These integrations significantly reduced both the Mean Time to Detect (MTTD) and the Mean Time to Respond (MTTR).
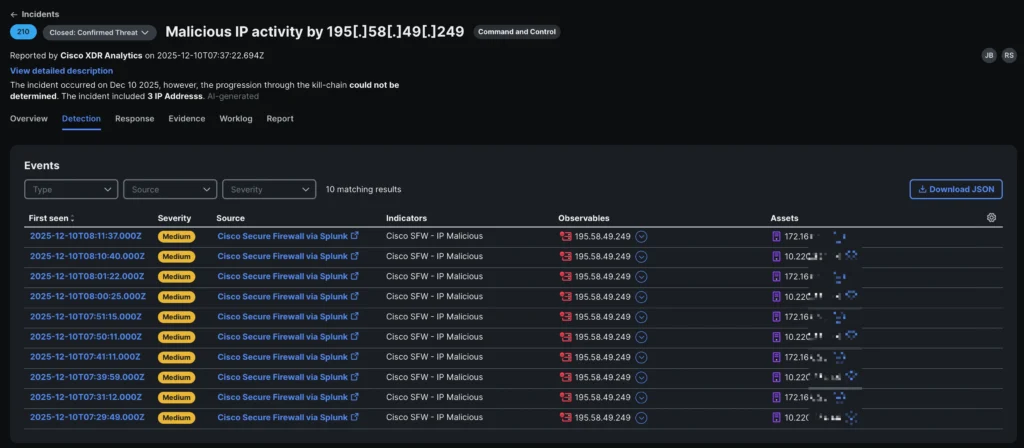
In the morning of December 10th, the first day of Briefings and Keynotes, the following detection appeared in Cisco XDR Incident Management:
2025-12-10T07:29:49.000Z: Malicious IP activity by 195[.]58[.]49[.]249
This incident correlated multiple indications about connection to a known malicious IP address on the internet.
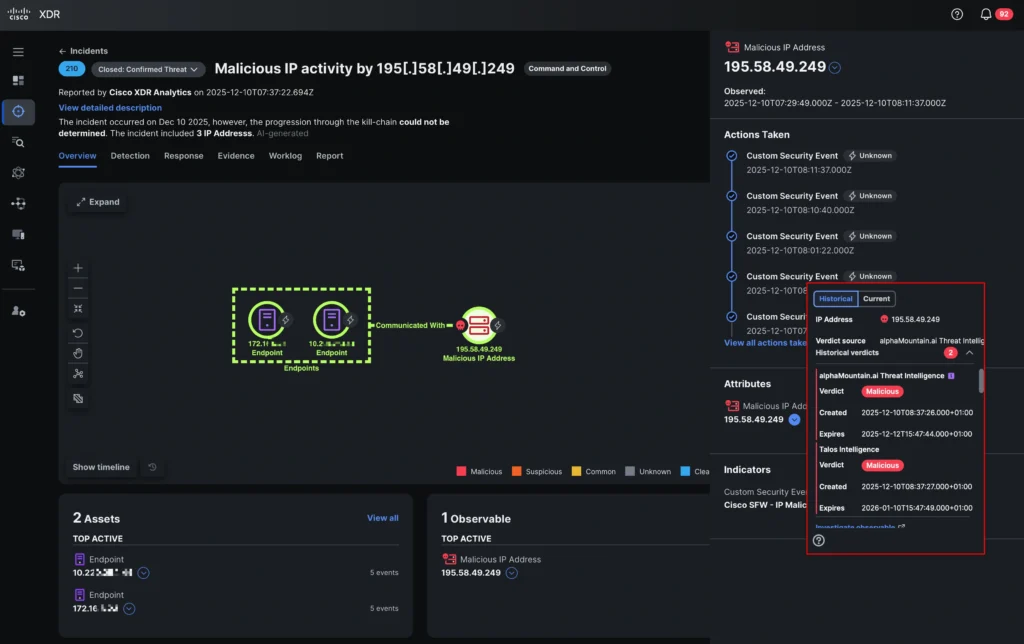
Cisco XDR provided valuable details about the observables of the incident, like which intelligence sources provided the malicious verdicts, and it allowed the team members to follow traces to hunt down this attack.
Investigation Steps
While the initial alert flagged communication with Russia based IP 195[.]58[.]49[.]249, an investigation with the Corelight Open NDR solution revealed that this device was actually communicating with dozens of distinct external malicious IPs on TCP port 22067, indicating it is likely part of a distributed botnet (possibly associated with CoinMiner (or similar malware families using this port). The Palo Alto Networks firewall team also confirmed the detection.
A quick look in Cisco Secure Access and the Corelight NDR solution also revealed that we did not see any DNS requests before the actual conversation started. As a result of this investigation, the Cisco team at Black Hat Europe 2025 developed a new XDR workflow to automatically investigate DNS logs from various sources to check if DNS resolutions to specific IP addresses were seen in the recent past or not. This will improve future investigations by eliminating manual tasks and reducing the time to investigate. Further searches in Corelight Investigator exposed that TLS1.3 was used with no Server Name Indicator (SNI).
Both, no DNS resolutions and missing SNI, increased the likelihood of potentially suspicious activities.
In parallel, one of the team members had a look at the packet captures taken by Corelight Open NDR. As he explored the world of TLS 1.3 handshakes, something interesting caught their eye: JA3 fingerprints.
JA3 hashes are found in the TLS header of the client’s “ClientHello” packets. They collect several details about the client’s TLS preferences and roll them up into a unique MD5 hash. What makes this so useful is that different clients – such as web browsers, bots, or even malware — often present distinctive combinations of these details. This means their JA3 fingerprints can serve as reliable identifiers, helping us spot exactly who (or what) is knocking at our digital door.
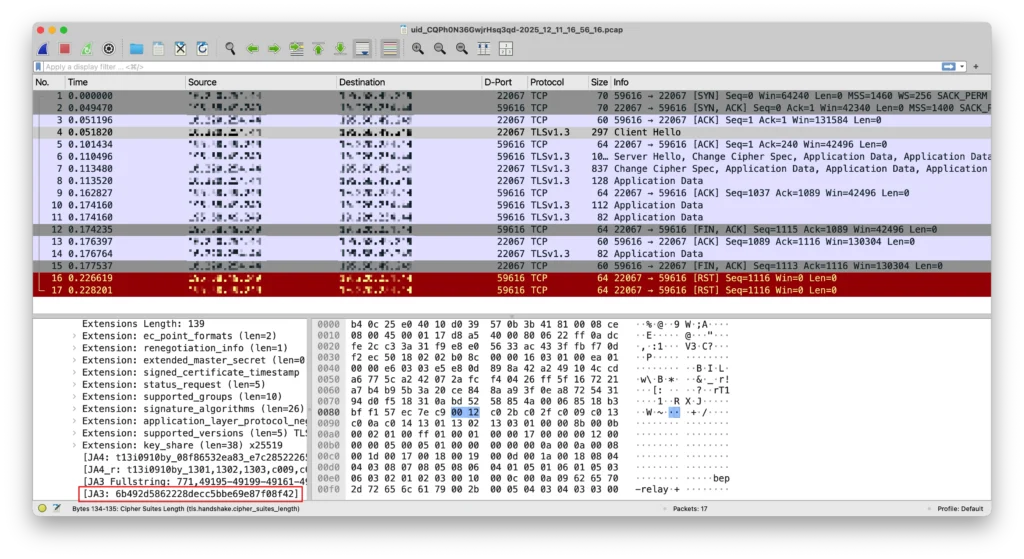
A quick search for this JA3 hash led us straight to an open-source P2P file synchronization tool called Syncthing. Syncthing is designed to keep files in sync between devices, whether they’re on the same local network or scattered across the Internet. By default, Syncthing clients try to connect directly to their configured peers – taking the most straightforward route whenever possible. But if a direct connection isn’t possible, they get creative and use a public relay server to make the connection happen. Interestingly, this relay server typically communicates over port 22067, which lines up perfectly with our earlier findings.
So far, so good! We’ve pieced together a clear picture of the type of communication we’re seeing and what clues to look for on the source devices. With this information in hand, it’s time for the next step: Let’s track down the asset and see what’s really going on under the hood.
Takeaway and Response
In a typical enterprise setting, a SOC analyst would now reach for an EDR or an Endpoint Forensics tool to gather evidence and remotely respond right on the user’s device, with no need to leave their chair. However, at Black Hat conferences, these tools are intentionally off-limits except for some critical event assets. That means the team had to go old-school and handle responses directly on-site, adding an extra layer of excitement (and maybe a few extra steps) to the process.
At an earlier Black Hat conference, one of the Cisco team members developed an XDR Automate workflow to integrate asset information into incidents. The workflow is automatically executed at the incident creation time and pulls in information about the IP scope, the location at the conference venue, and an indication of the potential use of the assets. The result is stored as a note in the worklog of the incident and easily available to the analyst.
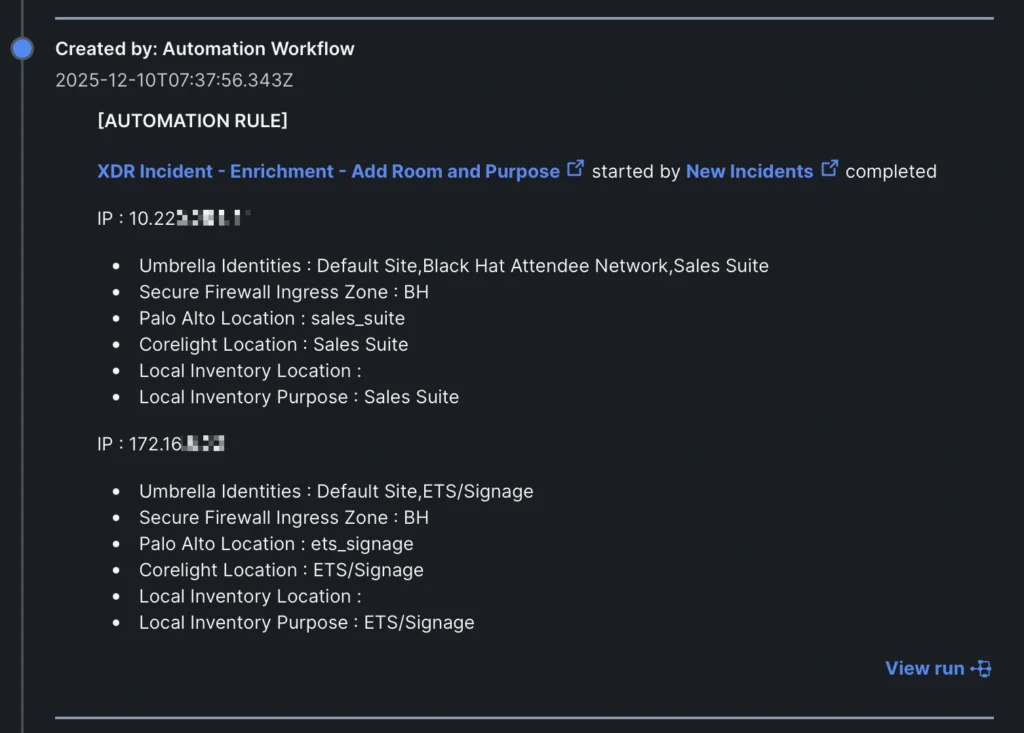
Since this device appeared to be a Sales/Operations machine (according to the SSID on which it connected to the Internet), operated and deployed by Black Hat rather than a student/guest device, immediate remediation was advised.
- Locate & Isolate: Locate the machine in the Sales Suite and disconnect it from the network to stop the P2P beaconing.
- Scan & Reimagine: The machine is likely infected with a botnet loader. Run a full antivirus scan or reimage the device entirely.
- Check Credentials: Given the “Sales” context, ensure any credentials used on this device are reset, as the malware may have scrape capabilities.
The on-site investigation in the meeting room quickly uncovered the culprit: a rented notebook that had been connected to a display for demonstration purposes. It turned out that the notebook hadn’t been cleaned up or re-imaged after its previous use, leaving behind a digital trail that led us straight to the source of the activity.
The incident was highlighted in the Black Hat Europe NOC report.

Final Thoughts
As an automated and open security detection and response platform, Cisco XDR played a critical role in the secure NOC operations at Black Hat Europe 2025. It enabled NOC and SOC analysts to detect and investigate real incidents in real time by integrating Cisco and 3rd party solutions into a single platform.
While investigating incidents within XDR, analysts could review the attack chain, add notes to the worklog, update the incident status, and discuss with Splunk, Firewall, Secure Access and NOC partner teams using Slack and Webex. Event correlation via Cisco XDR and effective team collaboration was key to successful identification and remediation of threats.
Throughout the SOC operation, Cisco XDR’s automation enhanced the efficiency of the analysts noticeably, and the team created new automations based on incident response findings and activities. Keep an eye out for new workflows on Cisco XDR Automate Experience soon!
You can read the other blogs from our colleagues at Black Hat Europe.
About Black Hat
Black Hat is the cybersecurity industry’s most established and in-depth security event series. Founded in 1997, these annual, multi-day events provide attendees with the latest in cybersecurity research, development, and trends. Driven by the needs of the community, Black Hat events showcase content directly from the community through Briefings presentations, Trainings courses, Summits, and more. As the event series where all career levels and academic disciplines convene to collaborate, network, and discuss the cybersecurity topics that matter most to them, attendees can find Black Hat events in the United States, Canada, Europe, Middle East and Africa, and Asia. For more information, please visit the Black Hat website.
We’d love to hear what you think! Ask a question and stay connected with Cisco Security on social media.
Cisco Security Social Media





