This month marks the 50th anniversary of Burt Munro setting the land speed record on a motorcycle. Munro used a 1920, 1,000 CC Indian motorcycle at the Bonneville Salt Flats in Utah to set a record of 184.087 mph—a record that stands unbroken for its class to this very day. He was 68 years old when he accomplished the feat.
But how did Munro do it? He didn’t have the newest bike. Munro’s modified version was more than 40 years old at the time the record was set. Without modifications, the bike’s top speed was around 60 mph. Munro performed a lot of testing and learned from many failures to develop the configuration that would eventually set the record. He raced all over his native land of New Zealand before eventually working his way to Bonneville, where he continued to push the bike’s limits. He talked with other enthusiasts and built up his knowledge to continually improve his model and manufacture better parts. Compiling information, testing, and modifying gave Munro the determination he needed to etch his name into the record books.
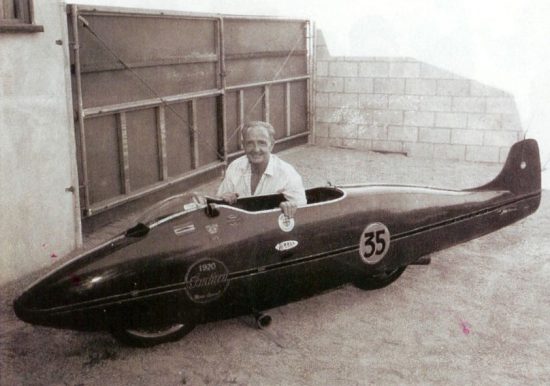
Munro and his record-setting Indian motorcycle. Photo on Munro from https://roadtrippers.com/stories/breaking-burt-munro-record
Break records using your manufacturing data
Much like Munro, manufacturers are on a quest to continually improve and boost their productivity. Munro was continually improving on a 40-year-old model. Similarly, manufacturers don’t always have the luxury of swapping out to new equipment and must use and improve on what they currently have deployed. The common thread is using data to gain a competitive advantage.
Technology advancements have moved the acquisition of data from a manual process to “always-on” and automated. Munro did not have that luxury in 1967 and had to build from trial and error. Manufacturers in this day and age have access to modern networks, IoT devices, software, and sensors for end-to-end visibility in their factories. This actionable information from IoT systems in turn creates new opportunities for record-breaking, such as:
- Increasing profitability
- Identifying efficiencies
- Improve business operations
Data pitfalls to watch out for
Despite its benefits, more data also comes with challenges, including an overload of information that can slow operations if not carefully managed. Understanding the frequency, prioritization, and orchestration of the data is a key to avoiding setbacks.
Munro also recognized that the original bike wasn’t built to support a rider at the speeds he wished to achieve. More speed equaled more risk. Munro created a large fairing around the bike that gave him a speed advantage, but it also served as better protection for him at high speeds. The same is true of more devices and information. Protection must be built in and managed properly as more data and information come onto the network. Threats will continue to advance at a rapid pace, and manufacturers must use protective gear to mitigate the risk.
A handbook for driving data in manufacturing
To help manufacturers with the speed at which data is coming at them, we developed a guide to Data Management in Digital Manufacturing. The guide provides best practices around data management, as well as tips for embracing the possibilities without introducing new risk. It also includes key case studies as well as resources that can help you shift into this new data model. Remember, data is the new fuel of industry—and the key to record achievements.
I also invite you to explore the following manufacturing topics:





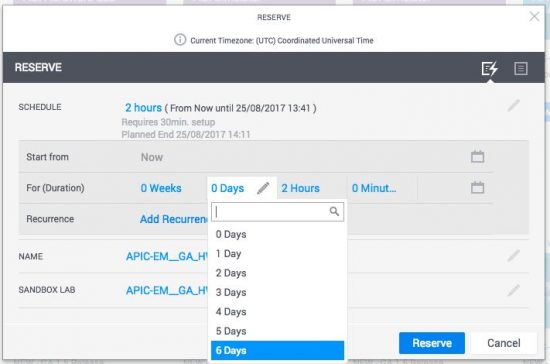

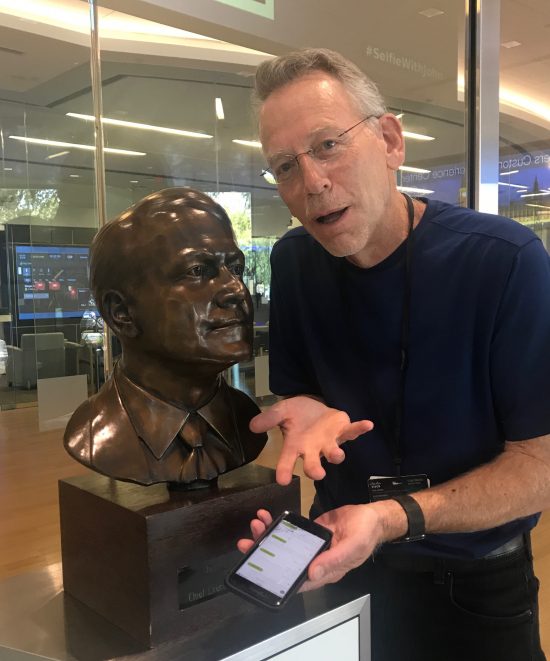

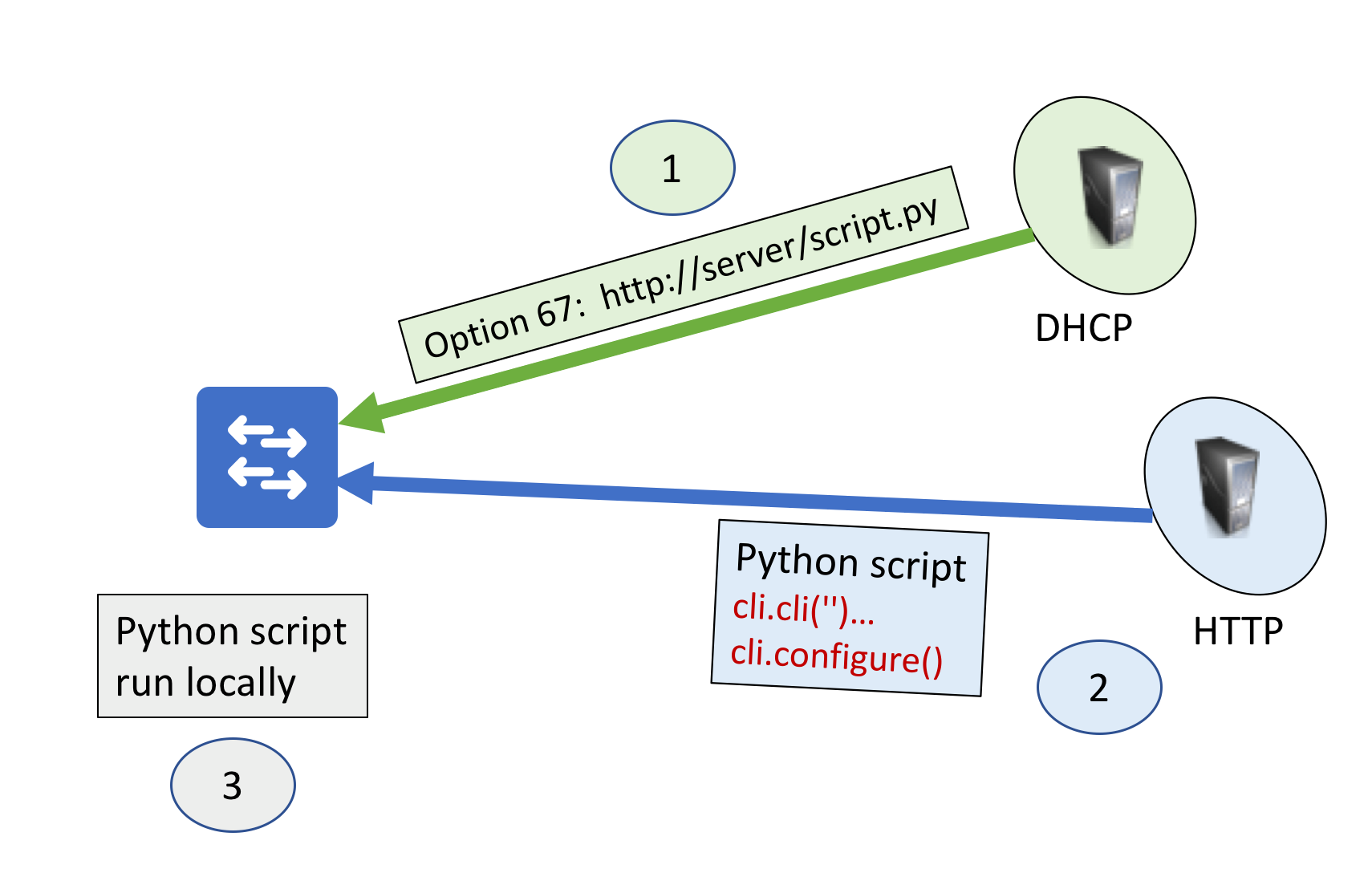 Figure 1 Basic ZTP Use Case
Figure 1 Basic ZTP Use Case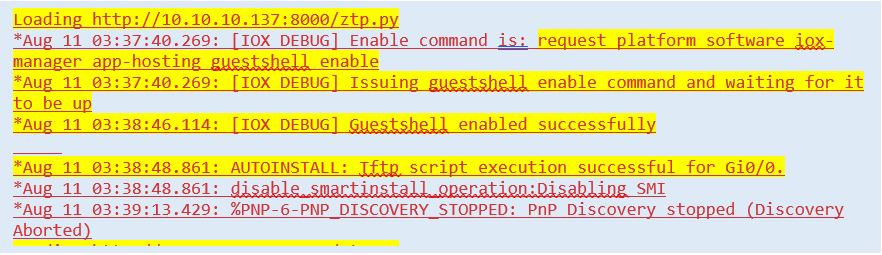 Figure 2 – Log messages during device boot process
Figure 2 – Log messages during device boot process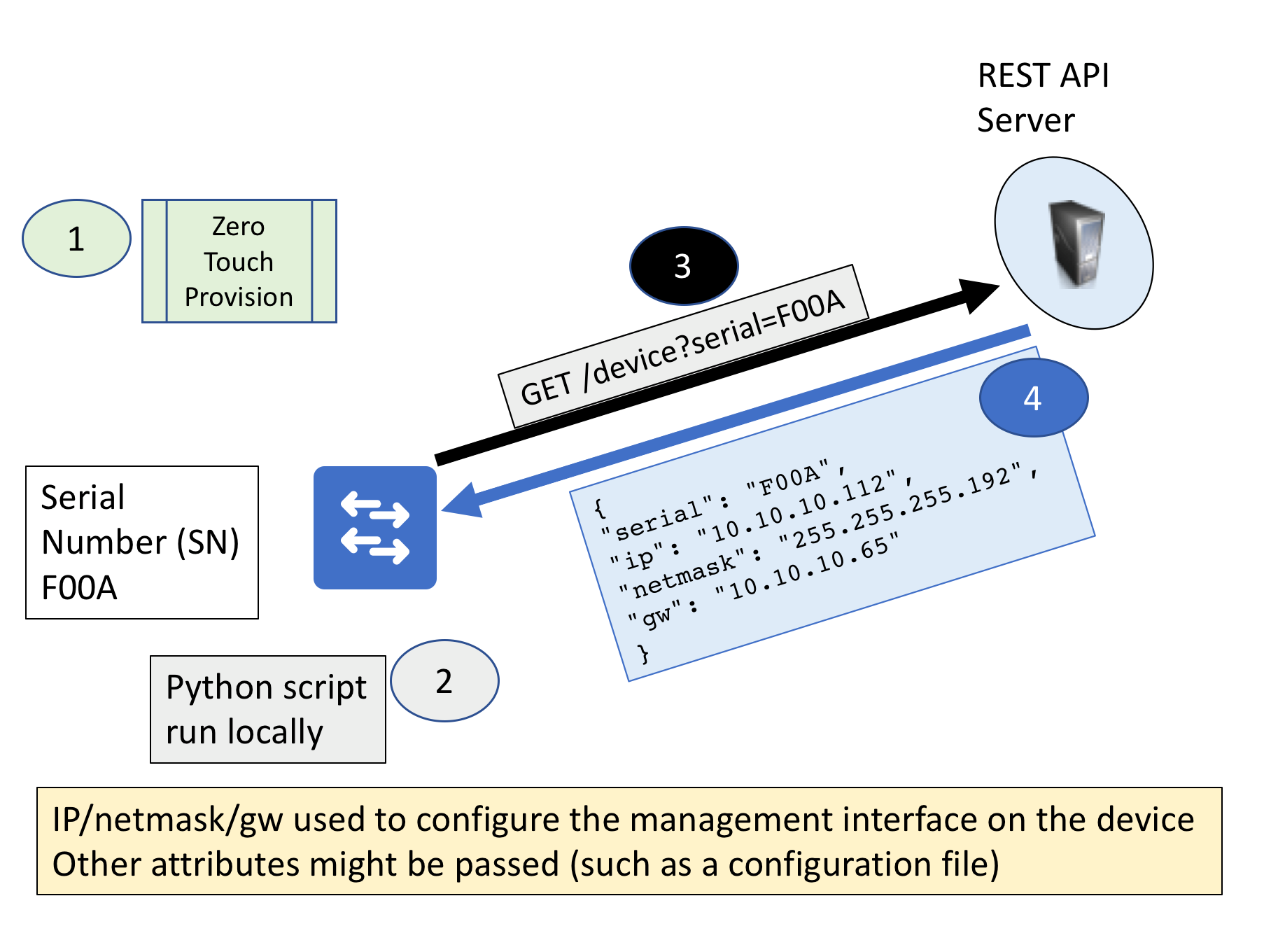 Figure 3 Dynamic Use Case
Figure 3 Dynamic Use Case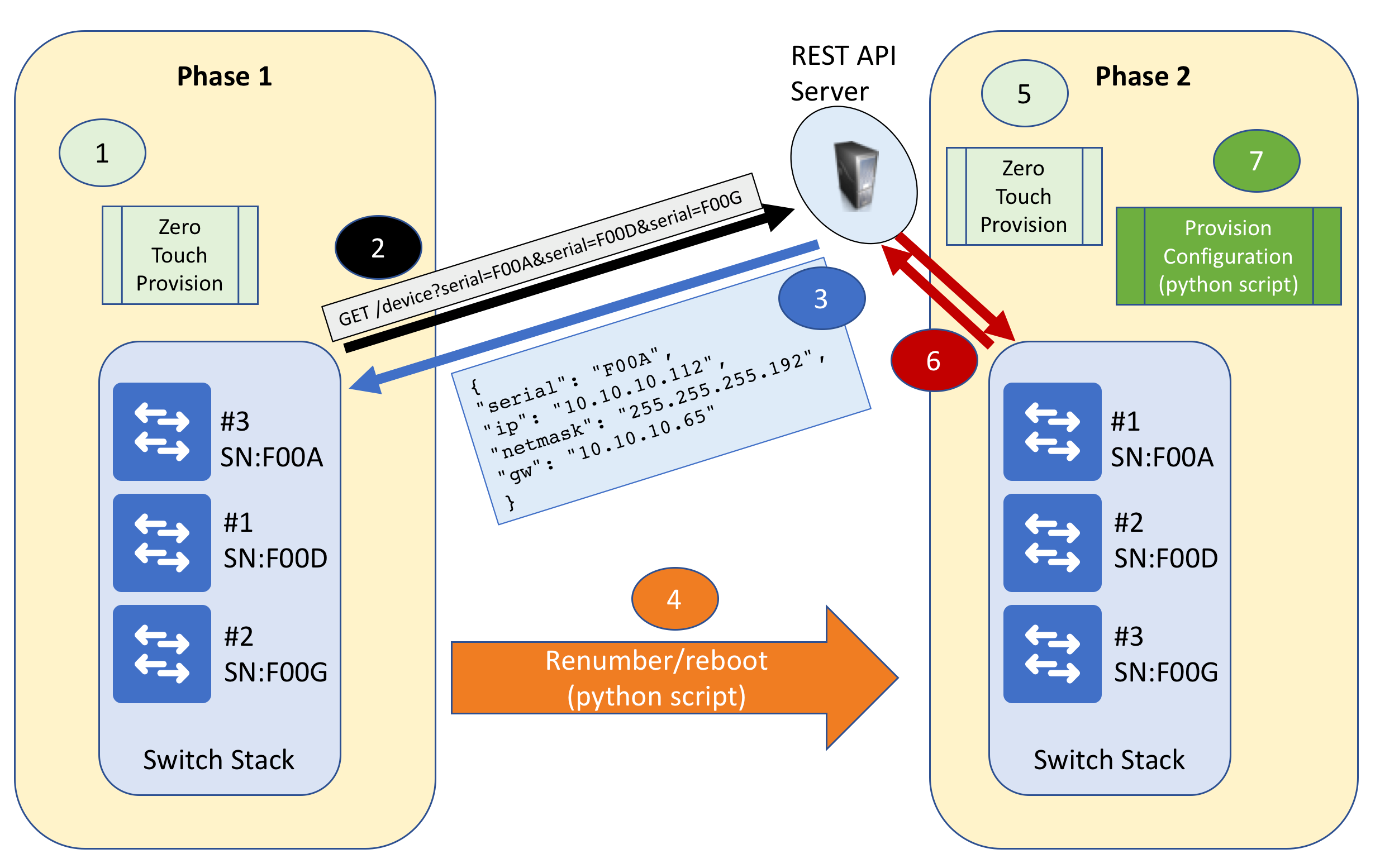 Figure 4 Stacking
Figure 4 Stacking