The University of Oklahoma (OU) is using October, National Cyber Security Awareness Month (CSAM), to emphasize the creative and common-sense actions they are taking to improve cybersecurity and educate users across campus about the importance of being smart online. Higher education organizations face many of the same cybersecurity challenges as commercial ones: assuring availability, keeping personal data safe, and protecting intellectual property, but they also want to keep their environments as open as possible to encourage creative teaching, learning, and engagement.
Aaron Baillio, Managing Director, Security Operations and Architecture, and Lynnetta Eyachabbe, Cyber Security Awareness and Outreach Coordinator, have tied CSAM to the university’s overall cybersecurity initiatives and will be working all month on raising awareness. Here’s why each of their IT Security Top 5 is important, and the steps they are taking to focus awareness and drive actions among their users this month:
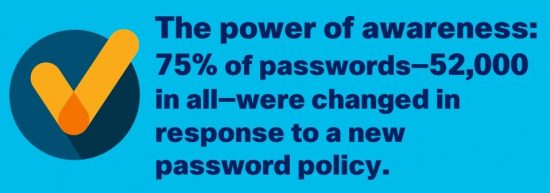
Passwords—Stealing a password may be as simple as looking over someone’s shoulder to see what they type or as sophisticated as social engineering and password cracking programs. Many people use the same password on many sites, so once the bad guys have one password, they can quickly “own” the user with access to their accounts on many sites. At OU, CSAM will serve as a reminder to users to set unique passwords for each account (school, shopping, streaming, email) to cut down on password reuse.
In fall 2016, the university implemented a new password policy that encouraged users to change all passwords and replace them with a 12-character password or passphrase. The results were significant: 75 percent of the approximately 70,000 passwords used—more than 52,000 in all—were changed before the university had to take the more drastic step of locking out accounts until new passwords were set.
Antivirus/Antimalware—Next-generation tools are gaining wide acceptance in the market as long-used signature matching intrusion prevention tools have been ineffective against newer, more advanced malware. These next-generation tools use machine learning, virtualization, cloud analysis, and other methods to guard against threats. OU has adopted these next-generation products and is finding them significantly more effective. They consume fewer system resources while detecting viruses or malware more quickly and accurately. The university provides enterprise endpoint protection for faculty and staff and during the month will be stepping up their recommendations for free applications for students.
Phishing—Phishing is one of the most common ways cyber criminals gain unauthorized access to users accounts. Email and web filtering, which are commonly used to stop phishing, can be tricky to apply in an open campus environment, so training users becomes even more important. Phishing is one of the most significant security issues facing the OU campus, and to combat it, the IT team regularly cautions users on phishing messages and how to identify them. The school even uses an “in-house” phishing effort with select departments—doing “on-the-spot” training when a user falls for the phishing attempt. For CSAM, they are increasing the cadence of their “Knowing the Signs” awareness program and are offering phishing assessments of school departments. Some tips they provide to faculty and students in email alerts and campus blogs are:
- Always read what is being requested before granting permission
- Verify with the sender before clicking or opening an attachment you are not expecting
- Attempt to verify web address for links without clicking
One year ago, OU experienced phishing attacks daily and the average response rate was about 15 percent per attack—with hundreds of accounts compromised each week. One year later, in September 2017, OU experienced fewer attacks, about two dozen, and had just 300 compromised accounts in all—a reduction in compromised accounts of more than 50 percent.
Encryption of Data and Secure Email—Use of encryption for data files and to secure email is growing quickly because it protects data from people who have gained unauthorized access to files, the network, or communications channels. At OU, they provide encryption for sensitive data, especially for those departments needing a higher standard of security due to regulations and compliance. In addition, they publish a sensitivity matrix showing which services are appropriate for storing certain data types. For example, to store HIPAA data, local file storage or O365 are the only allowed storage locations.
Multi-Factor Authentication (MFA)—In addition to requiring a username and password, asking users to present additional, separate evidence of who they are, such as a fingerprint, PIN, or smart ID Card, provides a higher level of security. OU offers an MFA solution to their users and continues implementation across the campus. They are stepping up user education on the importance of additional layers of authentication while also stressing that these multiple levels of security are needed to protect data.
National Cyber Security Awareness Month gives institutions of all sizes an opportunity to remind users of the importance of cybersecurity. As the team at the University of Oklahoma is showing, user education is vital to any successful cybersecurity initiative. Each of the IT Security Top 5 requires understanding and engagement from those who use the university network. In many cases, the actions are simple—like maintaining hard-to-decipher passwords or verifying a link before clicking—and gaining user acceptance and adoption can help ensure critically important protections online.