We often hear of the many challenges of the industrial revolution, but one of the scourges of this time period that often goes unmentioned was mass fires. To the people of the time, great fires threatened the very viability of industrialization. The number of fires bearing the moniker ‘great’ helps prove this point: The 1835 Great Fire of New York, The Great Fire of Pittsburgh, and The Great Chicago Fire are just a few examples.
There are some parallels between these fires and the great breaches we are experiencing in the information age. We see many of the same dramatic reactions, but the ultimate solution proves to be much more practical. Let’s look at a specific example to understand this relationship:
The Great Chicago Fire of 1871, in particular, left a deep scar on the American spirit. The fire started at night in a small barn. Aided by high winds, the fire spread from building to building until one third of the city was destroyed. Chicago was America’s fastest growing city at the time, and the inferno received widespread attention. Large-scale fires would continue to plague urban centers throughout the 19th century.
In response, many people criticized the rush to industrialize or blamed the conflagration on divine retribution. Despite the panic, the ultimate solution to the problem was constructing buildings a little farther from each other, utilizing flame-resistant materials and implementing quick response to fires. This was the birth of fire codes, which helped create an environment resistant to the spread of fire and ultimately lead to a reduction in major urban fires.
This concept is equally as effective when applied to the network to help reduce the spread and damage of a breach.
In many networks, there is little stopping an attacker from accessing everything once they are inside. Like a fire, they spread from area to area until nothing is left and all of the data is compromised. Network segmentation brings your network up to code. Separating users and network resources into separate zones can slow the spread of a compromise. And just as automatic sprinkler systems and quick response systems helped contain fires, effective incident response processes and tools can keep a compromise from becoming a massive data breach.
Segmentation: the digital fire code
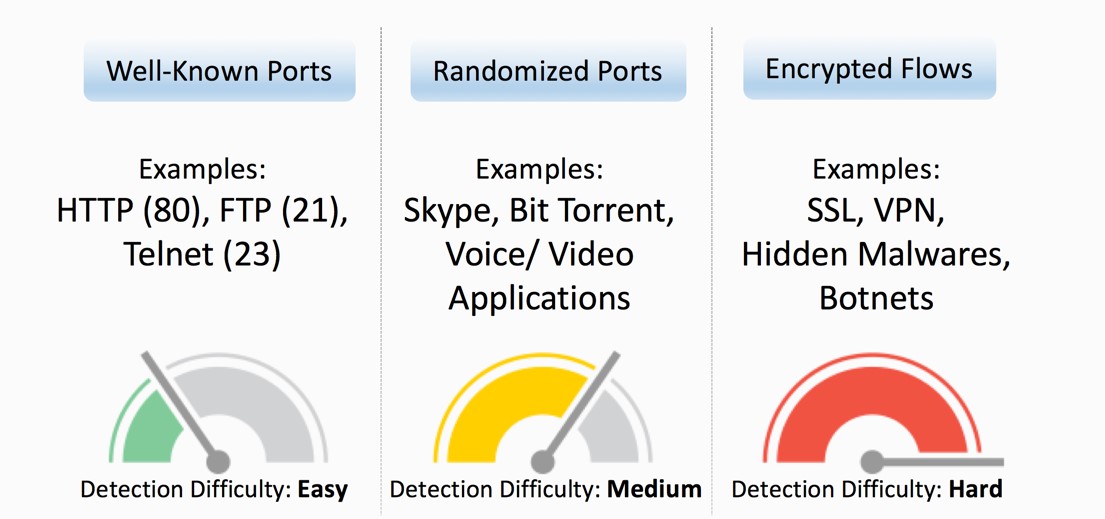
In an unsegmented network, everyone can access everything with few exceptions. Marketing can access proprietary intellectual property, engineers can obtain sensitive financial documents, and contractors and third-party vendors have enough access privilege to cripple the company’s digital infrastructure. While this may be convenient from an employee standpoint, it is a nightmare for security teams. An attacker can compromise a single user, through phishing or other means, and they have access to all of the company’s sensitive resources.
Network segmentation helps address this problem by giving employees access to only the resources they need to perform their job. It operates under the principle of least privilege and has been around for years. But there are some challenges that often prevented organizations from effectively implementing segmentation policies.
Historically, network segmentation was dependent on access control lists (ACLs), which had to be maintained individually across every point of enforcement. As networks became bigger, ACLs ballooned to thousands of individual rules, and making changes was a painful, time-consuming process. In addition, mistakes in segmentation policies could prevent employees from legitimately accessing a necessary resource, which could impact productivity and the company’s bottom line.
But there is an answer that relegates many of these challenges to past: software-defined segmentation.
A new era of segmentation
Software-defined segmentation helps address the challenges of traditional segmentation largely by centralizing and simplifying management. Cisco enables software-define segmentation via Cisco Identity Services Engine (ISE) and Cisco TrustSec technology.
Using this solution, network administrators can design policies that assign users and devices into logical groupings, called security group tags (SGT). Policies define what groups can communicate with each other, and what groups are restricted. These policies are then enforced across every TrustSec-enabled device on the network.
These policies are created and managed from a centralized console, which pushes out updates to the entire network at the same time. This makes adjusting segmentation policy a simple and quick process. In fact, customers who implemented TrustSec technology saw as much as an 80 percent decrease in their IT operational costs, according to The Total Economic Impact of Cisco TrustSec by Forrester.
New segmentation needs new methodology
Even with the advantages of software-defined segmentation, there still exists the challenges of crafting policies that are effective and do not impede legitimate access. Many network administrators do not know what every role within a company does and what network assets they need to perform their job. To solve this problem, you need a way to see what network traffic exists today and the ability to model policies without enforcing them to assess their accuracy.
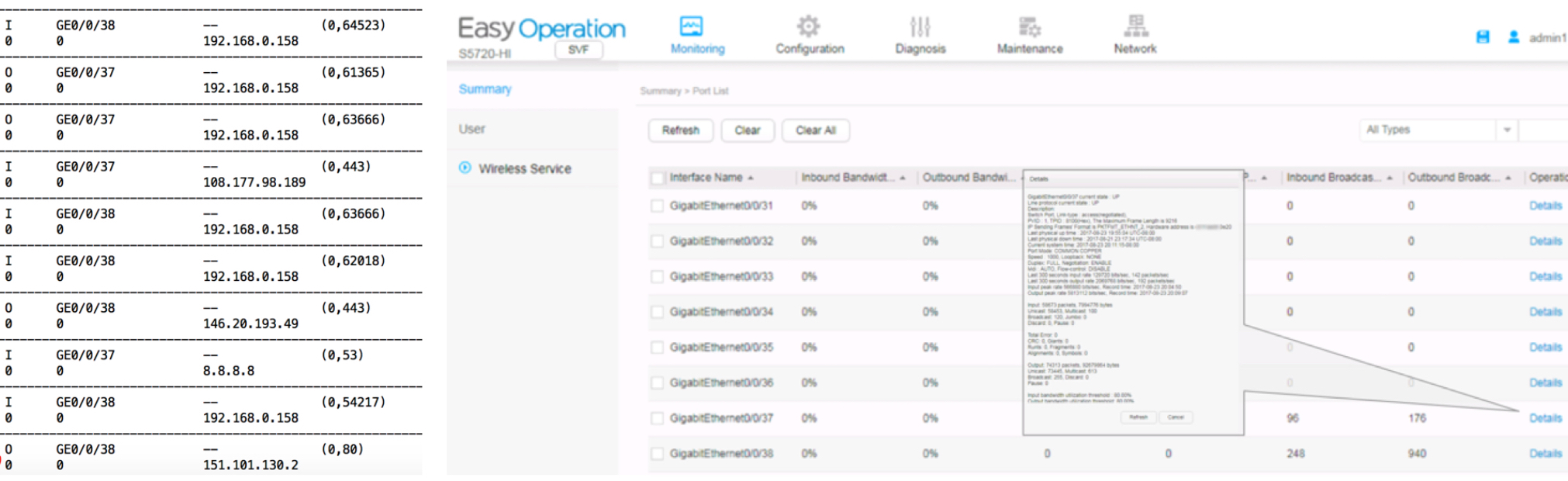
Cisco Stealthwatch Enterprise delivers complete visibility into all network traffic. This allows you to:
- Inventory network assets and classify them based on role or function
- Gain insight into user behavior and interactions on the network
Using this information, you can intelligently design segmentation based on activity that is taking place on your network. And to ensure you aren’t disrupting critical business activities, using host group policies with Stealthwatch Enterprise, you can model proposed segmentation policies – without enforcing them yet. This allows you to identify what activity would be prevented if your policies were fully implemented. Then you can decide if that traffic is legitimate, and adjust your policies accordingly, or determine it is inappropriate activity.
Stealthwatch Enterprise can also help you evaluate the effectiveness of your segmentation policies. You can configure custom alarms to trigger if any there is any traffic taking place that should be forbidden by segmentation policies. This helps you identify segmentation policies that are not configured or implemented properly.
Don’t forget incident response
Segmentation is great for limiting the reach of an attacker and the scale of a breach, but it doesn’t prevent compromises in the first place. Just as fires still require firefighters to prevent further damage, compromise requires strong incident response to prevent a breach.
Fortunately, Stealthwatch Enterprise can help detect threat activity early. Through a combination of advanced behavioral analysis and machine learning, Stealthwatch Enterprise can detect early indicators of compromise such as command-and-control communication, connections to servers in unusual geographies, and network scanning. It also provides all of the information you need to identify the source of the incident in minutes.
Through integration with ISE, you can quarantine affected hosts with a single button-click inside the Stealthwatch Enterprise management console. This prevents the host from communicating on the network and spreading the infection while you remediate the device.
Bring your network up to code
As the threat landscape continues to evolve, security personnel need to give themselves as much leeway as possible. Similar to modern fire prevention, you cannot stop an event from ever happening, but the right amount of preparation can keep a small fire from burning down the rest of the city.
Network segmentation has always been an important defensive measure, but it wasn’t until recent technologies were developed that it could be effectively deployed in large enterprise networks. Just as fire codes help prevent catastrophes, software-defined segmentation can severely limit the reach of a breach and improve an organization’s security posture.
To learn more about how Cisco can help you segment your network, read our eBook Segment Your Network for Stronger Security.