Today, Talos is releasing details of three new vulnerabilities discovered within Apache OpenOffice application. The first vulnerability, TALOS-2017-0295 within OpenOffice Writer, the second TALOS-2017-0300 in the Draw application, and the third TALOS-2017-0301 discovered in the Writer application. All three vulnerabilities allow arbitrary code execution to be performed.
It is that time of year again; leaves are turning, the air is crisp, and every week teams from the National Football League line up to participate in the ‘ultimate team sport’, American football. As a lifelong fan, I watch every Patriots game and I am certainly not alone. It is that diehard devotion that the NFL counts on to drive viewership and revenue in this $50 billion dollar business, which is what networks and carriers like ESPN and DirecTV have committed to the NFL until the early 2020s.
For fans, there are a growing number of options for watching our favorite teams, many of which are designed to appeal to “cord cutters.” This season, for example, you can choose from Amazon Prime, Verizon Wireless, or Twitter, if you’re willing to subscribe and pay. Games continue to shift from network television to cable to internet streaming services. And as more games become available through streaming platforms, we can expect the rise of sketchy, illegal, pirate streaming sites. 
If service and content providers fail to protect such premium content from pirates, it is not out of the question that the NFL could find itself in the same bind as the “other” football (translation – soccer). A recent BBC survey suggests that up to one half of English Premier League fans have accessed soccer matches through unofficial providers, resulting in a dip in reportable viewership and advertising revenue.
Pirate Talk:
Here’s some good news; Cisco can help service and content providers protect these valuable sports and entertainment assets from pirates with Credential Sharing Protection and Illegal Streaming Detection.
Recently, I had a chance to contribute to a Reuters article about the industry costs of password sharing, and Cisco’s solutions to combat the practice. The practice of password sharing certainly presents its fair share of ethical and legal questions, but it also has a very real, though often underplayed financial impact. Though it is difficult to nail down exact numbers, is estimated that password sharing costs an estimated $500 million annually in missed revenue opportunities.
But perhaps one of the biggest things keeping our service and content provider friends up at night is the emergence of streaming piracy. Perhaps you’ve heard of “fully-loaded” set-top boxes or dongles? These are boxes that have been modified with third party add-ons to allow illegal streaming of subscription content. This type of underground streaming piracy is made possible by a pervasive network of video production operations, who capture content from streaming devices and broker it through the dark web. These streaming piracy boxes and players have been made easily available to consumers, proliferating the spread of copyright infringement. The problem is becoming so widespread that one study suggests that illegal video streaming amounts to one-quarter of all global internet traffic. Live sports, in particular, is commonly streamed illegally, but the practice extends to other genres as well.
HBO has had recent success cracking down on pirated access to its wildly popular Game of Thrones series, through a combination of shutting down known piracy operations, and offering a greater number of options for viewers to legally access the content. On the retail front, Amazon, Facebook, and eBay have taken a firm stance and are working to proactively block the sale of such “fully-loaded” boxes that enable and encourage unauthorized access to digital media. With the threat of expensive legal action and possible criminal charges, illegal TV add-on developers are beginning to distance themselves, but the battle wages on.
Sky, a Cisco customer and co-innovation partner, recently announced an extended security collaboration with Cisco. Sky will expand the use of Cisco’s VideoGuard Everywhere conditional access (CA) and digital rights management (DRM) solutions to secure video distributed to millions of devices as Sky expands their multi-screen offerings. Together, we are building innovative solutions to defend against new forms of digital piracy.
Service providers must remain vigilant and continue to work to effectively protect their investments but the war cannot be won alone. At Cisco, Security is in our DNA and we have been providing security solutions for our service and content provider customers for decades. We provide unmatched network security and analytic capabilities that enable providers to flag and block pirates and password-sharers, alike. A parting message to pirates; time to surrender.
As data grows with more people, devices, and applications coming online, the data center storage infrastructure that hosts and powers the workloads also needs to evolve to keep up with the increasing demand. What should be truly alarming to any storage and storage networking admin is the vast majority of this data growth has happened in just the last few years. Just consider that it took the world more than 40 years to generate the first zettabyte, a run rate we reached last year.
As a result, customers are constantly on the lookout for high-performance, easily scalable, ultra-reliable, and highly intelligent solutions to manage their fast-growing storage and storage networking environments. The newest batch of Cisco innovations directly address the challenges our customers are dealing with every day. Here’s are the highlights of what we’re introducing (Press Release).
- More flexible deployment options at attractive cost points with a new line-rate 32G Fibre Channel Fabric Switch,
- Easier LAN/SAN convergence through support for Fibre Channel N_Port Virtualization (NPV) on the Nexus 93180YC-FX, built on Cisco Cloud Scale® technology,
- Advanced troubleshooting and enhanced SAN visibility through the new SAN Telemetry Streaming on MDS 9700 48-Port 32-Gbps Fibre Channel Switching Module.
- Deep and more efficient SAN visibility through enhanced integration with Virtual Instruments ( VI Press Release)
Attend this webinar to learn more: Nov 8th, 10am PDT.
Learn about the new 32G Fibre Channel Fabric Switch, FC-NPV support on Nexus 9300, SAN Telemetry Streaming, VI Integration
High-Performance SAN Switching at Entry-Level Prices
The new Cisco MDS 9132T 32-Port Fibre Channel Switch enables customers to cost effectively scale from eight to 32 ports as demand grows with each port capable of 32 Gigabits per second performance at line rate. This solution consolidates hundreds of high-performance virtual machines without disrupting existing architecture. The new switch includes up to 32 auto-sensing line-rate 32-Gbps Fibre Channel ports in a compact easy to deploy and manage 1-rack-unit (1RU) form factor.
Built on a versatile semi-modular design catering to both entry-level and departmental SANs, the Cisco MDS 9132T enables customers to grow from eight to 16 ports initially on the base, and expands up to 32 ports using the 16-port expansion module when capacity needs to grow, thus lowering initial cost of ownership. The MDS 9132T also offers enhanced onboard telemetry and a comprehensive set of built-in tools for flash storage environments, enabling end-to-end and proactive diagnostics to identify and correct conditions that can impact performance.
Fibre Channel NPV Support on Cloud Scale Nexus 93180YC-FX
Cisco is a leading innovator in promoting the benefits of LAN/SAN convergence. Cisco extends this lead with support for Fibre Channel NPV support on the Nexus 9300-FX fixed configuration data center switches, starting with support for 16G FC with a pathway for 32G FC.
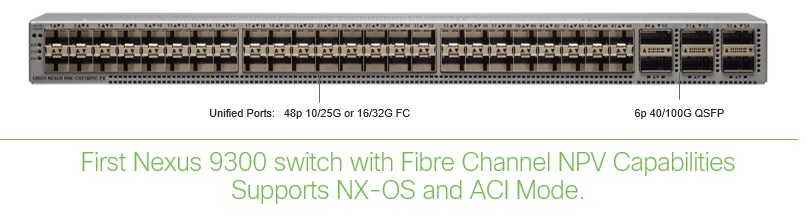 NPV is an FC technology designed to reduced switch management and overhead, especially as the SAN fabric grows. By adding NPV support on the Nexus 9300-FX, customers who have chosen to consolidate their LAN and SAN infrastructure at the data center access layer will have an easy migration path from the earlier generations of Nexus 5000/5600/6000 switches to state-of-the art capabilities of the Nexus 9300-FX, powered by Cisco Cloud Scale technology.
NPV is an FC technology designed to reduced switch management and overhead, especially as the SAN fabric grows. By adding NPV support on the Nexus 9300-FX, customers who have chosen to consolidate their LAN and SAN infrastructure at the data center access layer will have an easy migration path from the earlier generations of Nexus 5000/5600/6000 switches to state-of-the art capabilities of the Nexus 9300-FX, powered by Cisco Cloud Scale technology.
SAN Telemetry Streaming
Cisco SAN Telemetry Streaming improves troubleshooting and provides deep insight into SAN fabrics enabling users to analyze every frame, flow, at any speed. Enabled through built-in sensors, Telemetry Streaming performs at line rate for 100 percent visibility with no performance impact to data flows. This feature can be deployed anywhere in the data path, offering seamless integration and ease-of-operations. Further, no external hardware taps are required, which simplifies operations for a variety of troubleshooting, diagnostics use cases.
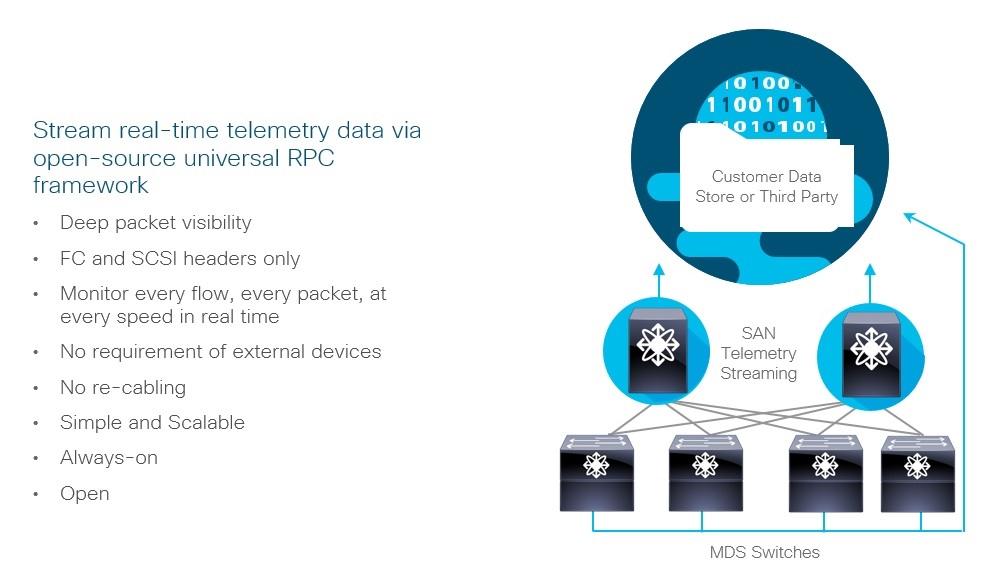
Cisco/Virtual Instruments Technology Integration
Cisco will offer direct technology integration with Virtual Instruments to solve current pain points of hardware probes and scalability on SAN fabric management. The integration combines the Cisco’s SAN Telemetry Streaming on MDS 9700 32G module with VI’s VirtualWisdom.
Cisco SAN customers can now choose to deploy VirtualWisdom non intrusively, eliminating the need for physical TAPs. Data will be streamed real-time from MDS FC SAN switches to the VirtualWisdom Platform Appliance. This brings together the best of the Virtual Instruments analytics capabilities with the best of SAN infrastructure.
Please check out these blogs by our partners !
Ramesh Chitor , Senior Director, Business Development, Tegile: Future-Proof Your SAN Investments With a Platform That Supports Cost-Effective Web and Cloud-Scale Deployments.
Rick Walsworth, VP Product & Solution Marketing, Vexata Maximizing Cisco 32Gbps Fibre Channel Infrastructure
Mike Jochimsen, Director of Alliances, Kaminaro, what-excites-us-about-ciscos-latest-announcement
Summary: Modern data center and cloud applications generate vast quantities of data and require more sophisticated processing capabilities than older-generation applications. Cisco is helping customers support today’s applications and resulting data growth with a number of performance, reliability, and fabric management/visibility innovations for the MDS and Nexus switch families.
For more info
Storage Networking
Press Release
Attend Webinar: Nov 8th: 10 AM PST
Tony Antony
Sr. Marketing Manager
Cisco and IBM created VersaStack to help IT organizations simplify and speed the deployment of infrastructure and applications. The beauty of Cisco and IBM’s joint solution is that it integrates and validates the very latest compute, network, storage, and software technologies from both companies into proven solutions. This innovation engine helps VersaStack offer the foundation for popular infrastructure-as-a-service (IaaS) offerings, hybrid cloud deployments, and enterprise applications while delivering investment protection for our joint customers.
Earlier this year, we extended VersaStack solutions to address IT modernization and emerging cloud-scale applications by adding infrastructure automation, hybrid cloud, and software defined storage capabilities. We are continuing to enhance VersaStack solutions through compute and storage performance enhancements, new software defined storage (SDS) cloud capabilities, and flexible consumption models.
A brief summary of new VersaStack technologies and capabilities are below:
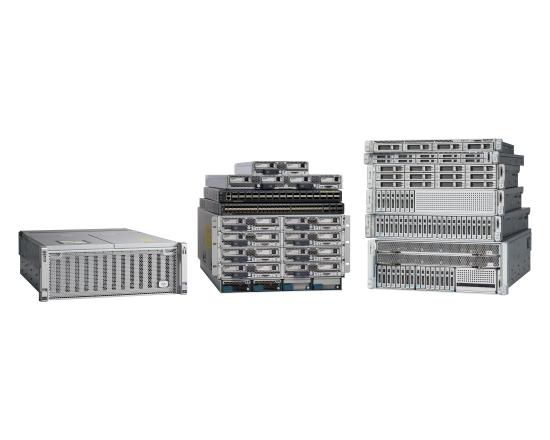
Next-Generation Performance: Businesses strive for faster decisions and to do that they need applications to run fast. To deliver that needed speed, VersaStack will now include the latest Cisco UCS M5 systems that bring new levels of performance for traditional, data intensive, and scale out workloads. Additional enhancements to IBM FlashSystems with FlashCore technology and IBM HyperScale capabilities can also increase performance while making it easy to scale capacity.
New SDS Cloud Capabilities: IBM Spectrum Virtualize for Public Cloud will now be available with VersaStack, providing real-time disaster recovery and data replication and migration possible between on-premises storage and public cloud resources. In addition, IBM Spectrum Access offers IT leaders the ability to deploy simple, cost-efficient, and secure VersaStack private cloud solutions.
Flexible Consumption Model: The combination of IBM’s Storage Utility Offering and Cisco’s Open Pay consumption model to enable IT organizations to deliver on premise infrastructure with the dynamic advantages of the cloud. IT teams can scale capacity instantly to meet the needs of the business while paying for only what they utilize.
For additional information on VersaStack, UCS M5 systems, and IBM VersaStack and storage announcements please check out the links below:

What’s a day in the life of a Cisco Cat Club member? Well, you’re about to find out.
This Friday was supposed to be a slow Friday. It started out like I intended – with a good morning workout (at the fabulous Cisco LifeConnections fitness center, of course!) and a cup of coffee from the Cisco Café. From there, I was off to answer emails and wrap up my projects for the week. The first email changed all of that!
When I opened my inbox I saw an urgent message from the Cisco Cat Club alias.
One of the members, Cora, reported that a cat was stuck in a tree right outside the building I was in. I dropped everything to see for myself. And there it was, a fluffy little ball of fur – a kitty named “Spotty” was perched in a tree approximately 50 feet in the air, crying out for help, and clearly in distress.
The cat lover side of me went into crazy cat lady panic mode. Fortunately, the Cisco project manager side of me went into problem solving mode! Spotty needed to be saved, and I was going to do my best to help her. I called Cisco Security and found out that many fellow Cisconians had also reported Spotty’s dire situation.
Cisco Security did not have the equipment to rescue him, however. Luckily, when Cisconians ban together – anything is possible, and that is where this tale is headed!
Enter the Cisco Cat Club and Community! They immediately sprang into action offering suggestions for help. After several emails, one of the members, Erika, contacted Cisco facilities and they suggested that Cisco’s landscapers could help since they have the proper equipment.
Soon after, they showed up with their truck with the long arm and cab. As they were starting to get close to Spotty kitty, it panicked and starting wiggling down the tree. A group of us were worried that the cat would jump, so another employee, Nhan, took off his shirt and we wrapped it around the tree to catch Spotty in case she fell. Then the landscaper gave us an even larger sheet to ensure we covered more ground.

Finally! Spotty kitty got herself down the tree, and ran off…scared, but safe.
This is just one example of how the Cisco community and “Cat Club” regularly come together to care for the feral cats on the Cisco San Jose campus. I joined this group just over a year ago after reading about them on this blog. I reached out and their awesome Chief Cat Club Coordinator, Jennifer Hull gave me a tour and I signed up to care for the cats at Building 12 and 17.

Every Wednesday morning, I give them food and water, and a once-over to make sure they look OK. It is truly one of the highlights of my week and makes me feel proud to work at Cisco.
On a regular basis, this dedicated group of Cisconians cares for all the known feral cats and kittens on Cisco’s massive San Jose campus. In fact, just as I am writing this blog, the community is trying to save a Mama cat and her newborn kittens.
Cisco has always been known for giving back, and this group is living proof of that. #WeAreCisco #LoveWhereYouWork.
Are you looking for a company that shares your soft spot for helping furry friends? We’re hiring!
So we’re a few weeks after the very first Mobile World Congress Americas (MWCA), and it’s interesting to look back and see how the event matched up to expectations. For an inaugural event, MWCA had some hits and some misses. We held some very interesting customer meetings. The Innovation City area was buzzing. But elsewhere, there was a lot of open space that created a feeling of sparse attendance. In fact, attendance was off forecast with 21,000 or so attendees, and the construction activity around the expansive Moscone Center area served to make the physical layout a bit disjointed. However it was a great start for this new event. Let’s see if the move to LA next year shows the event going more mainstream.
Nevertheless, 21,000 attendees and 1,000 exhibitors makes for a challenging network environment! And Cisco was happy to have worked with the GSMA to successfully provide carrier-grade Wi-Fi network experiences for MWCA, which allowed the GSMA to offer free high-speed Wi-Fi service to MWC Americas attendees as well as connectivity services to exhibitors. During the event, nearly 22,000 devices authenticated to the network and, amazingly, roughly 65% of them did so via Hotspot 2.0 (aka, Wi-Fi Certified Passpoint) enabled by Service Providers who support it for carrier offloading from cellular to Wi-Fi. Cisco has been an early proponent and supporter of HS2.0 in our Wireless LAN solutions to enable automatic authentication of mobile devices with SIM and SP-profile based connection on the Wi-Fi network.
With our Wi-Fi network analytics solutions, we also harvested a lot of interesting event-level data. For example, we know that 7.5 terabytes of data were carried throughout the conference. For more, check out some of our published results here:
- Press Release from Cisco about the MWCA network
- YouTube: Cisco at Mobile World Congress Americas 2017
We’ll see you next year at Mobile World Congress Americas!
On September 12, Gartner – the leading research and advisory company – released a competitive report on the secure web gateway (SWG) market. The report highlights the significant transformation as the traditional SWG gives way to a new platform –– the secure internet gateway (SIG).
Gartner states, “the SIG service platform offers a new promise to its customers — a richer overall set of capabilities delivered by a single entity — that could potentially offset or displace some or all of the bulk of on-premises solutions of yesterday (especially for branch office locations) and stand-alone SaaS offerings.”
By combining SWG functionality with other solutions such as a DNS resolution service and a CASB, a SIG provides:
- Ease of deployment
- Higher performance and lower latency
- Ability to filter network traffic
- Threat prevention beyond just HTTP, HTTPS & FTP
- Deeper control of SaaS applications
Why is this shift significant for Cisco? Because we have a role in leading this transformation.
Cisco Umbrella, the industry’s first SIG, is already delivering core functionalities outlined in the report and is designed as a platform in which additional capabilities can be added. Today, Umbrella combines DNS-layer security with a selective proxy to perform deeper inspection. This allows our customers to take advantage of the higher performance of DNS for the bulk of requests and leverage deeper content inspection for only unknown or risky websites.
This is just one example of how Umbrella is challenging traditional SWG providers. Cisco will continue to evolve and lead the transformation to SIG. To learn more about this transformation, download a copy of the Gartner report.
Source: Gartner, Competitive Landscape: Secure Web Gateways, Lawrence Pingree, Ruggero Contu, 12 September 2017.
Gartner does not endorse any vendor, product or service depicted in its research publications, and does not advise technology users to select only those vendors with the highest ratings or other designation. Gartner research publications consist of the opinions of Gartner’s research organization and should not be construed as statements of fact. Gartner disclaims all warranties, expressed or implied, with respect to this research, including any warranties of merchantability or fitness for a particular purpose.
Applying for E-rate can be tricky at times. With its complicated processes and strict form deadlines, it can feel like you are applying for funds that are sometimes difficult to get. Rest assured though, there really are funds at the end of the E-rate rainbow for you to take advantage of ($3.9B worth, to be exact). Wouldn’t you like to treat yourself to some of those dollars to improve your network infrastructure?
Think of all of the crazy network advancements you could make with $3.9B… bandwidth of 100 Mbps per student perhaps? A network so secure, not even Alan Turing could hack? So many network policies in place you’d never have to answer a help-desk ticket or trouble shoot a problem again? Though these ideas may be a little far-fetched, you can still use your piece of the E-rate pie for Cisco Meraki to get you closer to having your IT wishes granted.

Imagine being able to centrally manage your entire network from one simple interface. The Meraki dashboard puts the network at your fingertips, from quickly configuring hundreds of high-density access points, to traffic shaping your students’ music streaming apps, it gives you complete visibility into your network without needing specialized training. Cisco Meraki is specially designed for K-12 environments in a few key ways:
- Meraki MR wireless access points are designed for high-density classroom environments—so all of your second-grade students can stream educational YouTube videos on their iPads, while your fifth-grade students take standardized tests without any downtime or interruptions.
- Meraki MS switches are built to scale to support school districts of all shapes and sizes. Whether you have one location to manage or a hundred, you can remotely configure your network without being on site.
- Meraki MX security appliances enable you to create and maintain CIPA-compliant networks, which are mandatory for E-rate funding, so that you can sleep soundly knowing that student data remains protected and secure.
- By deploying a full stack of networking products that are easy to deploy and manage, you get back time to focus on projects that are important to you, allowing you to keep your school(s) on the cutting edge of new technology.
Treat yourself to Meraki! Our access points, switches, and security appliances and licenses are eligible* for E-rate funding. Learn more about our eligible E-rate solutions. To get a deep dive on our solutions for K-12, and specific product offerings, attend an upcoming live webinar. And don’t forget to get started with your E-rate application today!
* MX Advanced Security Licenses are 50% eligible; SM licenses and MC/MV hardware and licenses are not E-rate eligible per Funding Year 2018 eligible services list.
With the constant news headlines about data theft it is mandatory that organizations understand what data is entering, traversing, and leaving their networks and have the ability to examine that data if necessary for conducting network forensic investigations. Two popular style of attacks that are constantly in the news are data hoarding (Edward Snowden) and data exfiltration (large media companies) attacks. In all of these incidents, organizations were blindsided to find out massive amounts of data had been hoarded and then exfiltrated on physical media or via the internet.
To help with quickly investigating and differentiating data hoarding and data exfiltration attacks Cisco is releasing the latest software version 6.3.1 for the Cisco Security Packet Analyzer solution. This release has new tools for viewing and analyzing the data packets traversing networks. Along with capturing and allowing pcap analysis via a web based Wireshark type interface, the Packet Analyzer tracks all files it captures traversing the network and makes this list available for file carving (extracting files from captured network packets). That is, you can view a list of all files that were contained in the network traffic captured by the Packet Analyzer. Further along this line of investigation, you can search this list for specific files, source and/or destination IP addresses as well as port, protocol and other network related filters. Now if the file names do not give you enough information regarding the file contents the next step you can take is to actually select any files of interest and extract them. The Packet Analyzer will allow you to download the files and open them in their native application on your desktop. That is, you could view any document, spreadsheet, diagram, or image file traversing the network, or examine a piece of malware. As well, you could view any images including vacation photos captured in the network traffic. With the Security Packet Analyzer, you can quickly differentiate between malicious data hoarding of critical files and harmless data hoarding of internal manuals, data exfiltration of sensitive company data and data exfiltration of an employee’s vacation photos to a family member’s ftp server.
This file extraction capability is amplified by the Security Packet Analyzer’s native integration with Cisco’s Stealthwatch security solution. Stealthwatch is capable via network analytics of detecting and alerting an analyst of data exfiltration and data hoarding activities. From the Stealthwatch console with one button click a packet query can be auto-populated based on alert parameters and then executed against multiple Packet Analyzers throughout the network for analysis of a specific conversation. Once the query executes the analysis interface will load with the queried conversation available for intelligent packet analysis. From the interface, a list of all files in the conversation will be available and the option to download them will be accessible so you can very quickly understand what files were involved in the alert.
In addition to the file extraction capabilities of the new software release for Packet Analyzer, Cisco has added support for packet decryption of a wide range of private key cipher suites. This means if you are using an internal application with encrypted conversations using a known corporate key or private key, Packet Analyzer will be able to use a key and other session details to decrypt a conversation. Once a conversation is decrypted, deep packet analysis would be available along with the capability to extract any file contained within the decrypted capture.
As of October 2, 2017 the new software is available to download for installation on your existing Packet Analyzers. All new Packet Analyzer appliances will ship with the new version 6.3.1 of the software.
To learn more about Stealthwatch and Security Packet Analyzer integration read Brian Ford’s great post here.
Stay tuned for updates as the next release of Security Packet Analyzer will include a new virtualized version for lower capture rate branch-type deployments and integration with Cisco’s Firepower NGFW. Be sure to check out the Security Packet Analyzer site for product details and announcements.
