For many people, 2016 was a year full of surprises. Not only did the world lose some of the most famous names in music and film, but the outcomes of both the EU referendum and the US presidential elections caught many of the so-called “experts” off guard.
What does this have to do with innovation? More than you might think. It shows how we live in a VUCA world (Volatile, Uncertain, Complex, and Ambiguous) more than ever before. Disruption is everywhere and the events of 2016 have shown that predicting the future is neither simple, nor reliable.
As a result, many businesses are entering 2017 with more fear than in the past. Such fear will inevitably have an impact on the way you explore and implement new innovation projects. But with some inside knowledge, you can set aside some of that fear. I recently sat down with my team to discuss the three most likely trends to emerge over the next 12 months.
As you plan for 2017, you can use our insight as guideposts.
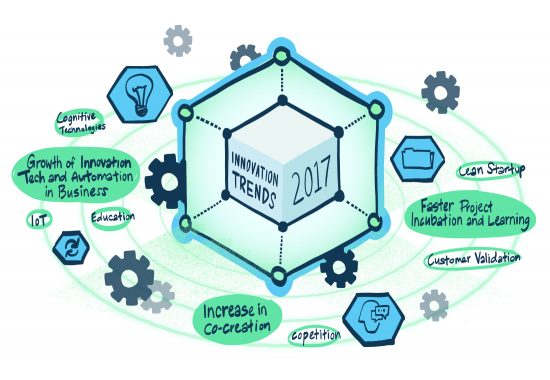
1. A move towards faster project incubation and learning
In the face of growing uncertainty, innovation project timeframes have to get shorter. More corporate businesses will adopt the Lean Startup approach of experimentation, rapid incubation, and fast failure.
By taking this approach, you create more rigor around the evaluation of both problems and ideas. This allows innovation teams to stay focused on genuine problem solving, while helping to identify dead-end ideas early in the process. Customer validation will play a more prominent role in the innovation process, testing concepts in the real world and helping to keep new concepts and initiatives relevant.
The Lean Startup is a strong framework for innovation, but this methodology must be understood and applied correctly. It’s not a linear process as genuine disruptive innovation is often messy and ambiguous. The best ideas will only emerge after several iterations and refinements, something that many businesses aren’t ready to allow.
So the question becomes, “Is your business ready?”
2. A growing presence of innovative technology and automation in business
The prevalence of technology in business continues to grow at an unprecedented rate. 2016 was the coming of age for exciting technologies such as augmented reality and virtual reality, which are now finding genuine uses in fields such as medicine and real estate.
2017 will also bring incredible innovation. Artificial Intelligence, machine learning, other new cognitive technologies, and the continued expansion of the Internet of Things (IoT) will transform the way many organisations fundamentally operate and interact with their customers. As a result, we’re likely to see more experimental innovations emerge using technology such as these at their core to push the boundaries of possibility.
New technology undoubtedly improves the way we live and work, but it mustn’t come at the detriment of people and jobs. Technological innovation should be accompanied by a conscious effort to reskill people of all ages for the future. Children must be educated for a workplace very different to the one we inhabit today, but older generations of workers, and their skills, must not be lost either.
Ask yourself, “How will my organization reskill for the future?
3. An increase in co-creation around innovation
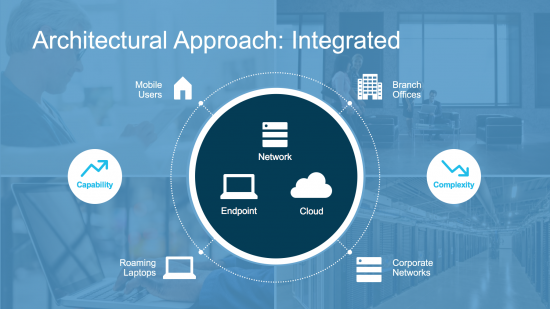
The concept of co-creation has long been known, but largely unpracticed in the business world. However, a growing desire to protect their futures has led many companies to become less guarded in recent years, paving the way for an exciting new collaborative movement. Tesla Motors is perhaps the most extreme example of this, opening up all of its patents to the public in a bid to move the electric car industry forward. There are many other collaborations now taking place as well, between companies normally seen as direct competitors. Cisco itself works closely with Apple, Intel, and Microsoft on a variety of innovation projects that move all partners forward.
Of course, with collaboration of this nature there comes a point where a natural divergence occurs. By that point, however, a great deal of healthy innovation and progression has already taken place. Remember, as an innovator, you don’t need come with completely new ideas, but with fresh eyes or a new angle. This is often all that’s needed to make a breakthrough. Look out for the term “copetition”—cooperating with competitors!
Look around and be prepared to say, “Let’s co-create.”
As 2016 has shown, predicting the future is never easy. We’re confident, though, that we’ll be seeing more of these three innovation trends over the next 12 months.
What are you expecting to see in 2017? Let me know in the comments below.
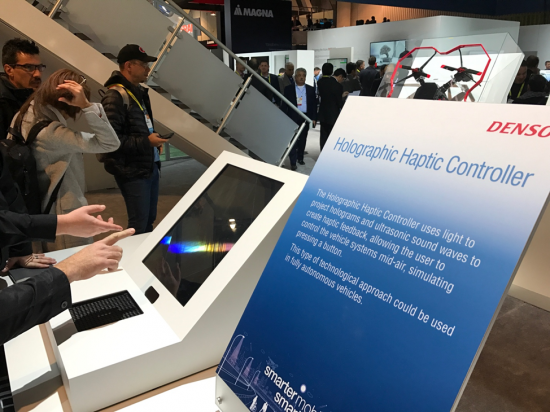
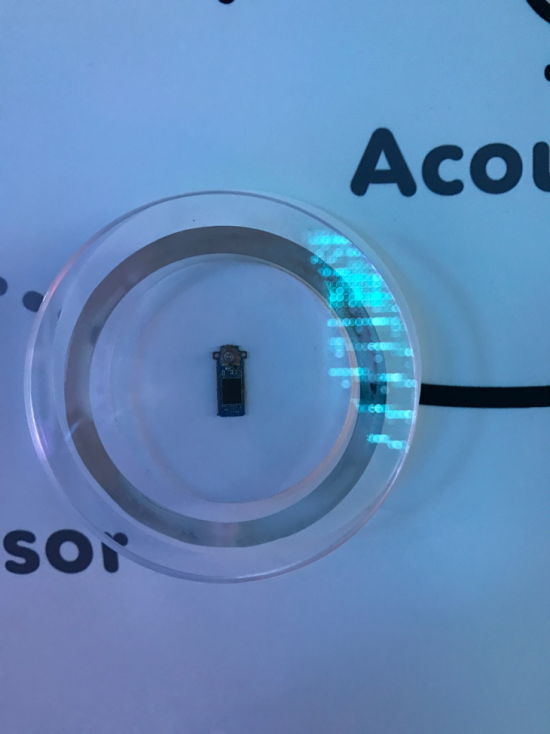 clarity of speech in noisy environments. In the Denso booth we saw a wide range of imaginative innovations from vacuum cleaner shoes to a robot barista; we also saw a novel contactless haptics system based on an array of ultrasound speakers. Combined with holographic projections and a leap motion hand sensor, this could create a revolutionary HMI where you not only see and interact with a software defined “virtual dashboard” but you can feel it as well! In the ChangHong booth we saw a contactless EEG brain control device. Embedded in a headrest, this smart sensor picked up enough brain waves for a user to control the speed of a car in a video game!
clarity of speech in noisy environments. In the Denso booth we saw a wide range of imaginative innovations from vacuum cleaner shoes to a robot barista; we also saw a novel contactless haptics system based on an array of ultrasound speakers. Combined with holographic projections and a leap motion hand sensor, this could create a revolutionary HMI where you not only see and interact with a software defined “virtual dashboard” but you can feel it as well! In the ChangHong booth we saw a contactless EEG brain control device. Embedded in a headrest, this smart sensor picked up enough brain waves for a user to control the speed of a car in a video game!