The upcoming collaboration launch at Cisco is a little more personal for me than most launches. Alan Kay, Doug Engelbart, and Steve Jobs have inspired me since I started designing collaboration products 12 years ago. This launch continues the journey they began.
Steve Jobs is widely recognized as one of the big visionaries of the digital age. He loved to talk about the Mac as “a bicycle for the mind,” empowering individuals to be more creative. But he didn’t come up with this idea all on his own.
The computer age started earlier, and Steve Jobs met and worked with some of the visionaries that set out the direction for it. Jobs would bring parts of these visions to reality, but completing them required reimagining what computers should do for people. That is just what we have set out to do at Cisco.
Creative Thinking for Kids of All Ages
When Jobs visited Xerox’s Palo Alto Research Center (PARC) in 1979, he saw the future in the form of a graphical user interface (GUI), which he later commercialized with the Macintosh. Alan Kay was one of the key contributors to this at PARC, and he later joined Apple as an Apple Fellow. Some of Jobs’s favorite quotes can be attributed to Kay:
“The best way to predict the future is to invent it.”
“People who are really serious about software should make their own hardware.”
But Kay’s true heart child was the Dynabook concept; a personal computer for children of all ages. His visionary concept, developed years before Apple was even founded, gives the impression of a blend between a tablet and a laptop. Most importantly, Kay envisioned the Dynabook as a collaborative device that could foster creative thinking in kids. It could handle any existing content but in a networked and editable form.
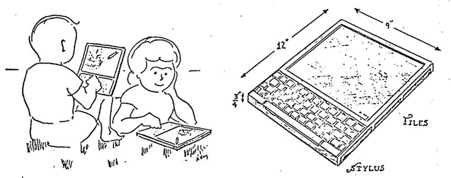
Kay’s original intent was not just passive consumption, but both creation and consumption where users could easily develop and modify simple applications. But even Alan Kay didn’t come up with this idea in a vacuum.
The Mother of All Demos
In 1968, a year before joining Xerox PARC, Kay attended an event in San Francisco that later become known as “The Mother of All Demos.” In it, SRI’s Douglas Engelbart revealed NLS, short for oN Line System, which included actual instances of:
- hypertext
- video conferencing
- screen sharing
- windows
- word processing
- revision control
- collaborative real-time editing
- a mouse as an input device
Remember, this was 1968. The computer professionals in the audience were blown away. Most key innovations that followed with the digital revolution trace back to Engelbart’s NLS.
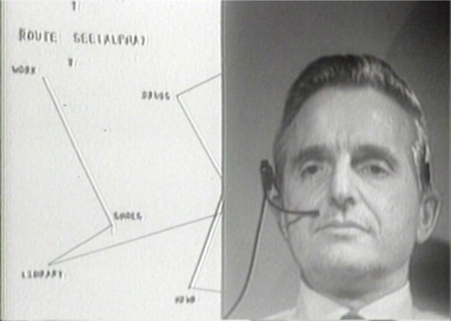
Kay was one of the few in the audience able to grasp Engelbart’s ideas beyond the individual technical innovations he demonstrated. “It was one of the greatest experiences in my life, Kay later recalled.
Engelbart’s vision for the future was highly collaborative and clearly stated: He intended to boost collective intelligence by augmenting human intellect. Engelbart envisioned people working together in shared intellectual space to collectively solve urgent global problems in a symbiosis between computers and humans.
Fulfilling the Collaboration Vision
People picked up on Engelbart’s individual innovations but failed to see the bigger idea that gave birth to them. And so, the digital revolution happened with individual users in mind, and the personal computer became its poster child.
When Jobs shared the Mac’s capabilities with Engelbart in the early 1980s, Engelbart pointed out that it had no access to other people’s emails, documents, or shared information repositories. To Engelbart, the Mac was like having an exotic office without a door.
Jobs brought MacBooks, iPhones, and iPads to the market. Although similar to the Dynabook in form factor, Kay felt they were designed for individuals. He believed there was still a need for a device that enabled collaborative creativity and problem solving.
We agree. Merging hardware and software that fully materialize this vision of collaboration has proved difficult. We believe it’s time to see it fulfilled.
Join us on January 24, when we take another step closer to a device focused on collaboration, teamwork, and creativity.