We all heard the saying that time flies (when you are having fun). It certainly has been a busy start to 2017 in many aspects and when my colleague Emmeline Wong posted her blog about ‘2017 New Year’s Resolutions: Ideas for Data Center Pros’ a few months ago, it feels like yesterday. With Cisco live Berlin and Melbourne behind us, we were both busy and had fun. Before we get ready for the next round of events and Cisco live Las Vegas in June, I like to provide an overview of the many innovations we announced as part of the ASAP Data Center Architecture in just these past couple of months.
Innovation
Cisco defines innovation as creating something significantly new, better and of value. It is not just an idea, but the ability to bring it to life. Based on five key pillars: build, buy, partner, invest and co-develop.
Flywheel of Innovation
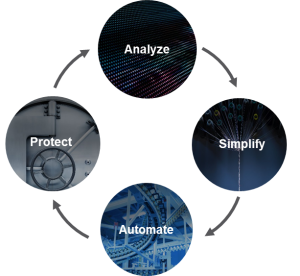
Based on four design principles of Analyze, Simplify, Automate and Protect building an integrated architecture with a consistent policy, the ASAP Datacenter empowers customers with the flexibility to run any traditional or cloud native application across any environment: on-premises, managed or public clouds.
As IDC states in this whitepaper: “Cisco is a strong believer in the merits of the flywheel effect — and thus a virtuous cycle — created by analysis, simplification, automation, and protection. Cisco’s ASAP architecture helps organizations navigate business modernization — and keep their flywheel turning — so they can simultaneously evolve in [these] four critical areas”.
Delivering across the Hybrid-IT stack and pillars of innovations
If you have the time, I encourage you to watch the on demand videos of the innovation talks ‘Go beyond automation: advancing your next gen datacenter’ at Cisco live Berlin and Cisco live Melbourne (log in required, sign up is easy). They cover all the recent announcements and provide insights how customers deploy our products and technologies of the ASAP datacenter architecture to drive better business outcomes, stay innovative and competitive to embrace the opportunities of the digital economy.
Here is a listed summary of our announcements in Q1 of 2017:
- Datacenter Networking/Nexus 9000:
- Datacenter Analytics/Tetration Analytics:
- Compute/UCS:
- Hyper-converged Infrastructure/HyperFlex:
- Converged Infrastructure/Versastack:
- Containers/Partnerships:
What’s Next
As I said at the beginning of this blog, 2017 has started with many memorable moments and news and it has been an eventful ride so far. So hold on tight and together (customer success stories) we keep the flywheel of innovation turning. To stay informed until Cisco live Las Vegas, join one of the Cisco Connect training events in your city or visit one of the innovation centers around the world. And if you are a developer: be part of the DevNet Create event in May, where applications meet infrastructure, to help create more magic.
Additional resources



 We are the single resource for everything ‘developer’ at Cisco, and we are here to help you learn, code, inspire and connect.
We are the single resource for everything ‘developer’ at Cisco, and we are here to help you learn, code, inspire and connect.