Even though Industrie 4.0 and smart manufacturing concepts have been around for a few years, thought leaders are now agreeing that Industrie 4.0 is at an inflection point. In a recent issue of CloudComputing News, this passage was particularly striking:
“Manufacturers are gaining the greatest value from Industry 4.0 by creating pilot projects that create flexible, agile, real-time platforms supporting new business models with real-time integration…For manufacturers in cost-sensitive industries, the urgency of translating the vision of digital transformation into results is key to their future growth. The more competitively intense an industry, the more essential real-time integration.”
We are definitely seeing this as we talk to manufacturers who are looking at different ways to accelerate their digitization projects in factories around the world.
Later this month Cisco will be at Hannover Messe, the largest industrial show, highlighting some of the key steps to securely digitizing your operations. Read more about our presence in Martin Dube’s blog here.

If you are planning to attend the conference, plan on catching many interesting sessions in the various forums on the following topics:
- [Mon April 24 at 10:40 -11:00] Theory of Operations for TSN-based Industrial Systems and Applications by Paul Didier
- [Weds April 26 at 11:10 -11:35] Automotive Industry Challenges and Opportunities by Martin Dube
- [Weds April 26 at 16:00 -16:20] Industries Digitization Journey – Realizing New Industry Business Outcomes with IoT by Bryan Tantzen
- [Fri April 28 at 11:20 -11:40] ‘Smart Connectivity and Data Analytics for Intelligent Process Field Devices with Fog Computing’ by Volker Sorhage
- [Fri April 28 at 12:30 -13:00] Collaborative human and machine insights & interactions to improve decision support and productivity by Daniel Keely
More information including locations for these sessions can be found here.
In addition, we will have subject matter experts presenting on various topics every ½ hour in our booth theatre in Hall 8, Stand C13 on topics such as:
- How to Get Started on your IIoT Journey by NYT best selling author and Cisco executive Maciej Kranz
- Opportunities in the New IoT Industrial Revolution by Bryan Tantzen
- Standard-based security architecture for control systems in a converged IT/OT environment by Maik Seewald
- How To Secure Remote Access Needs For Industrial Systems by Robert Albach
We hope to see you at Hannover and we look forward to helping you jump start your Industrie 4.0 strategies and plans.
For more details, check out our event site here.



 Get the Podcast
Get the Podcast
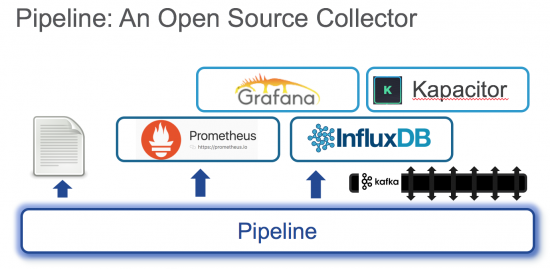 Big data platforms in open source include (among many)
Big data platforms in open source include (among many)