Detecting PowerShell Exploits
Black Hat returned to Asia again in 2017, with two days of technical hands-on Trainings, followed by two days of the latest research and vulnerability disclosures at the Briefings. The backbone of the conference was the WiFi network, built on site by staff from Ruckus. I was honored to be invited to join the Tech Team, as part of the Security Operations Center (SOC) within the Network Operations Center (NOC); developed from the relationships formed at the RSA Conference SOC.
With the smaller size and ad hoc network nature of the conference, the NOC and SOC can be in the same room, but duties are segregated. The primary mission of the NOC team was to ensure the WiFi network was not disrupted, quickly addressing an issue the first day with the WAPs dropping sessions. The primary mission of the SOC team was to protect the network from attacks: external and by attendees; with DDOS and traffic floods being the biggest concerns.
The technology stack was driven by the mission and contributing sponsors:
NOC
- Wireless network infrastructure – Ruckus
- Visualization – Open IP (OIP)
- TAP solution – Gigamon
- IAM – RSA
SOC
- NGFW – Palo Alto Networks
- Full Packet Capture – RSA NetWitness Packets
- Dynamic File Analysis – Cisco Threat Grid
- DNS / IP Intelligence – Cisco Umbrella Investigate
For incident response, no remediation was possible on endpoints, as they are owned by the attendees and vendors. Unlike Black Hat USA, where the network is large and segmented, and every classroom is identified, enabling pinpointing of problems or attacks; the Black Hat Asia network was flat. Only recourse was to block the MAC address of problem users.
As described in the RSAC SOC blog, the SOC team placed NetWitness Packets into Continuous Monitoring mode, where .exe, .dll and other potentially malicious payloads were carved out of the network stream and underwent Static analysis, Network intelligence and Community lookup; before sent to Threat Grid for dynamic malware analysis.
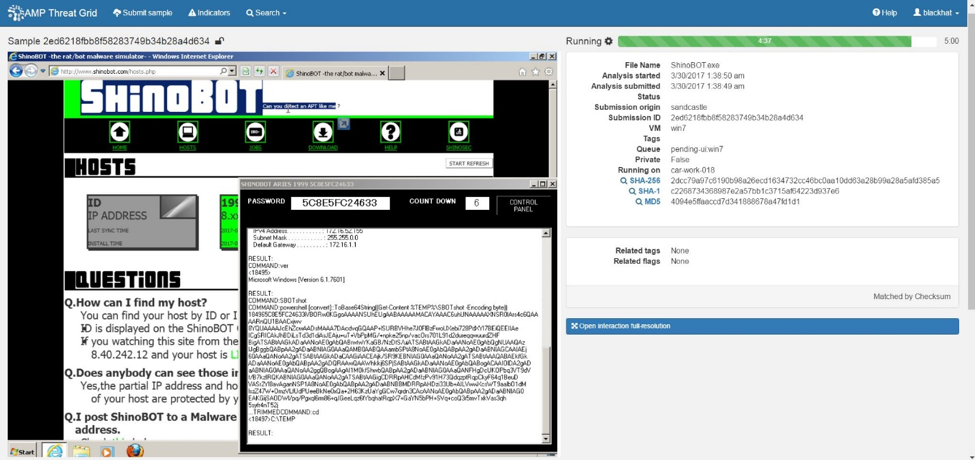
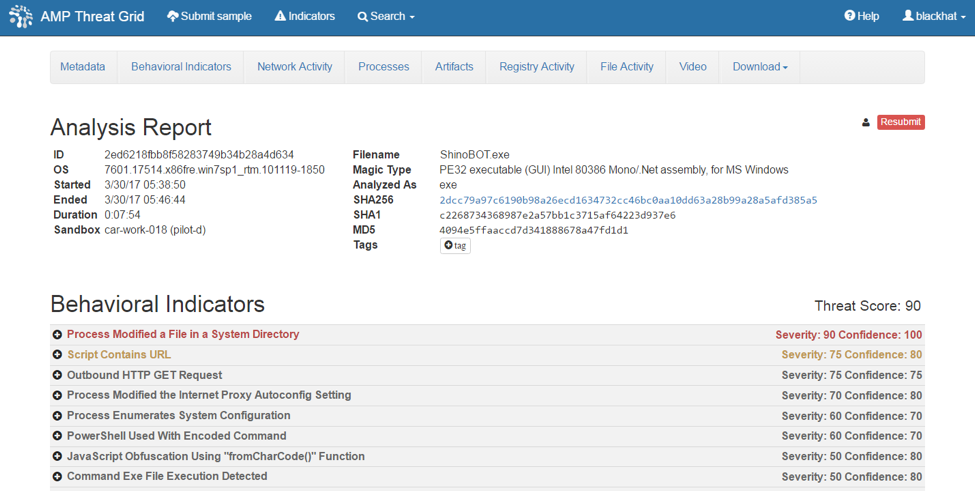
On the first day of the Business Hall, I noticed an .exe enter into the Threat Grid cloud, from NetWitness Packets, for dynamic analysis. I opened the sample in the ‘Glovebox’ to see what was happening, as we had seen many installers downloaded over the week. The interaction in the Glovebox allows for safe interaction with the samples, including full installation and clicking on dialog box pop-ups or checks for a human presence.
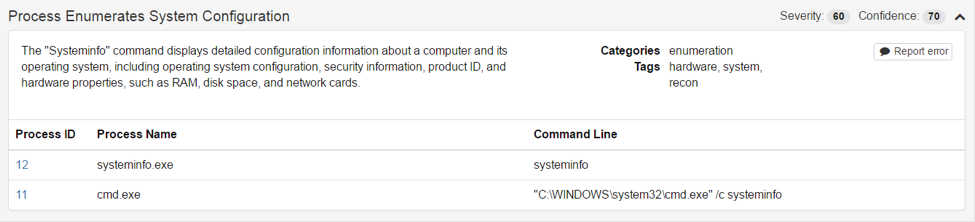
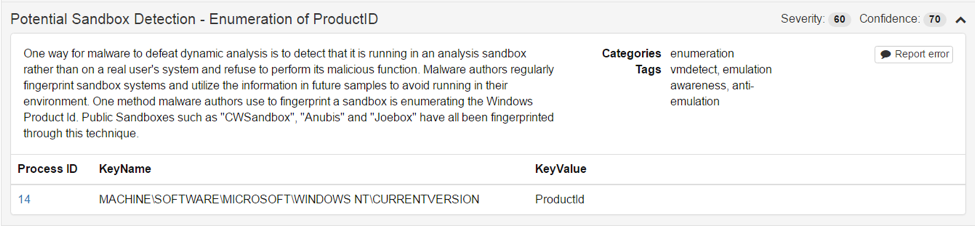
I noticed the sample was enumerating the system and exhibited the characteristics of a Remote Access Trojan.
This is a suspicious behavior for which Threat Grid alerted.
Because Threat Grid has no instrumentation or hooks into the virtual environment, there is no presence to indicate to the samples that they are in a sandbox, in fact the sample checking for was an additional behavior upon which to alert.
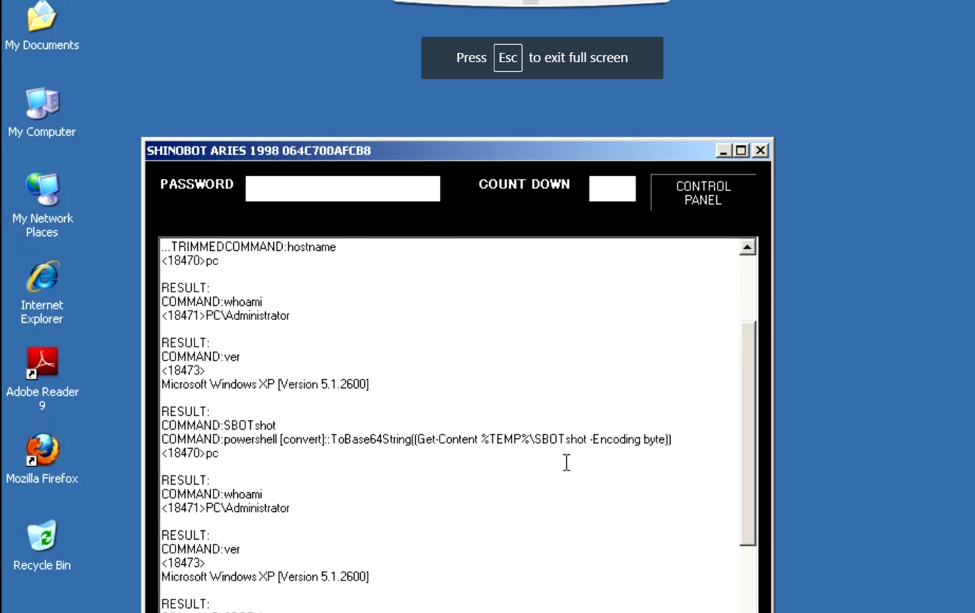
Those behaviors, and the observation in the Glovebox, caused me to escalate the detection to my fellow SOC members, who began the tracing the origin of the sample and the user. The run time for sample submitted via the Threat Grid API is five minutes, to rapidly provide a threat score to the SOC team, who started to investigate the user activity. The sample’s behavior warranted closer examination in the Glovebox; and I resubmitted (can go up to 30 minutes) to examine the Control Panel and command and control (CnC).
The CnC investigation lead me to the controlling infrastructure with the challenge: Can you detect an APT like me?
The answer was “Yes!”
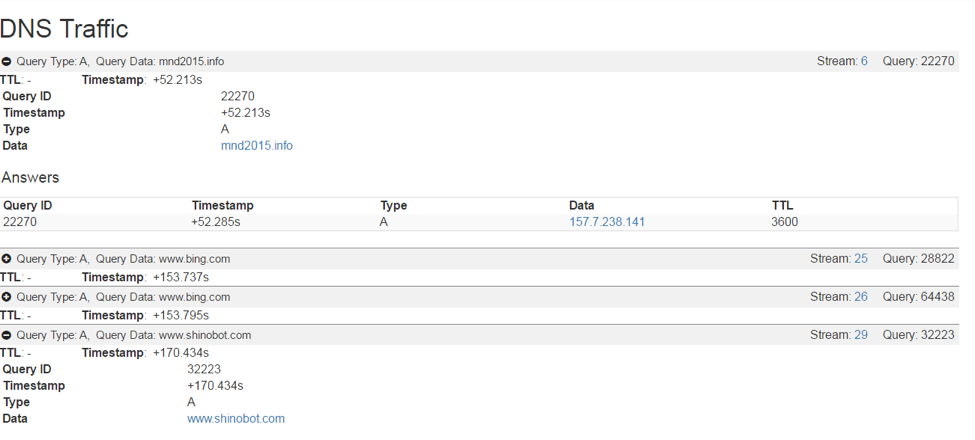
I dug deeper into the DNS traffic of the original CnC.
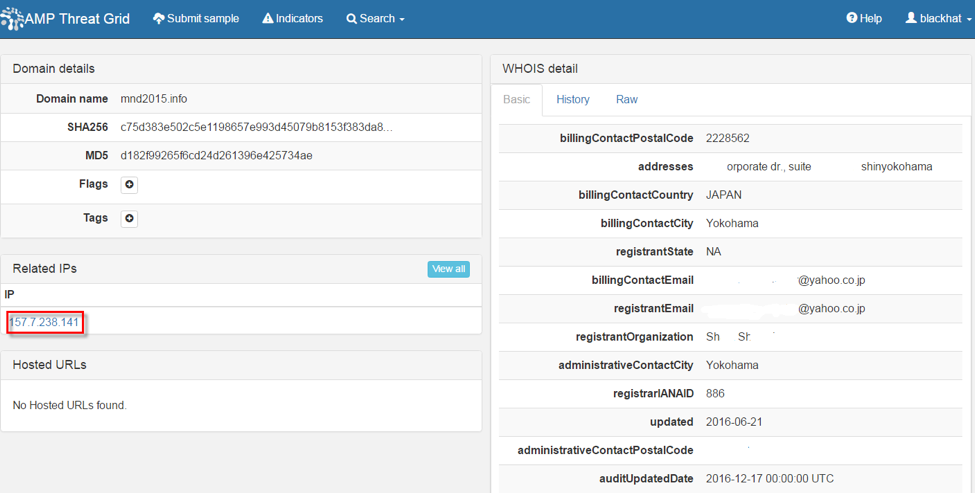
From this I pivoted to the related IP address.
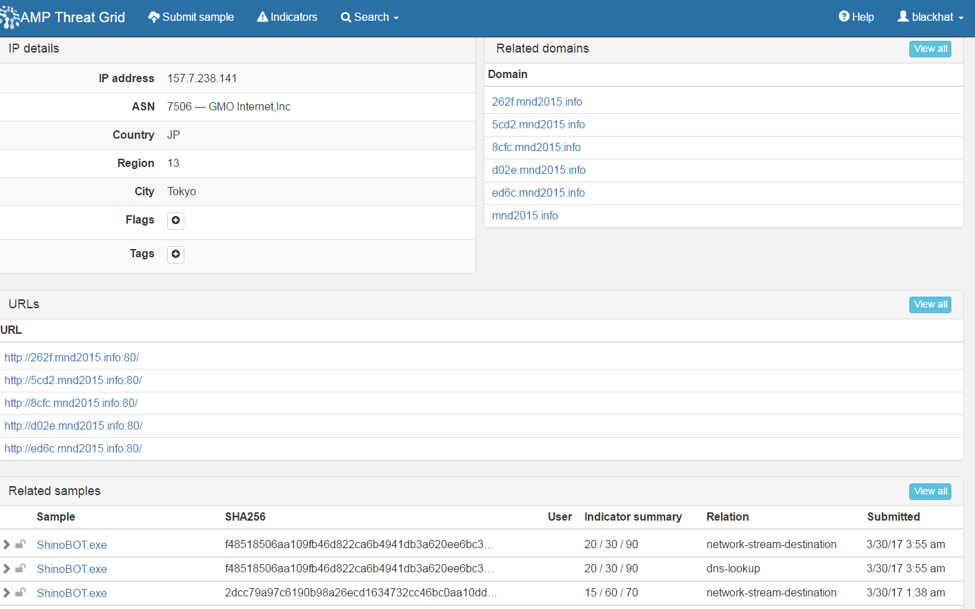
Because Threat Grid is not a “sandbox”, rather an integrated threat intelligence and dynamic malware analysis platform, I was able to examine the other domains associated with this IP address, from the behavior of other samples.
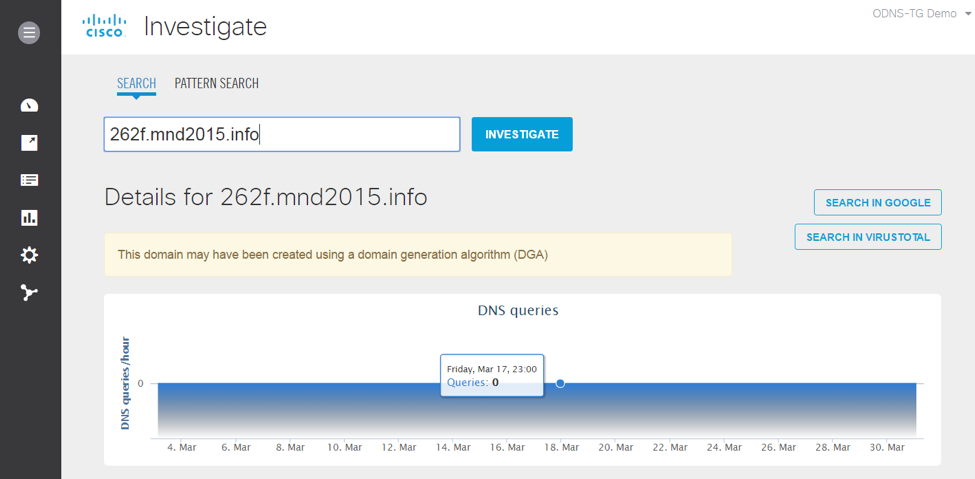
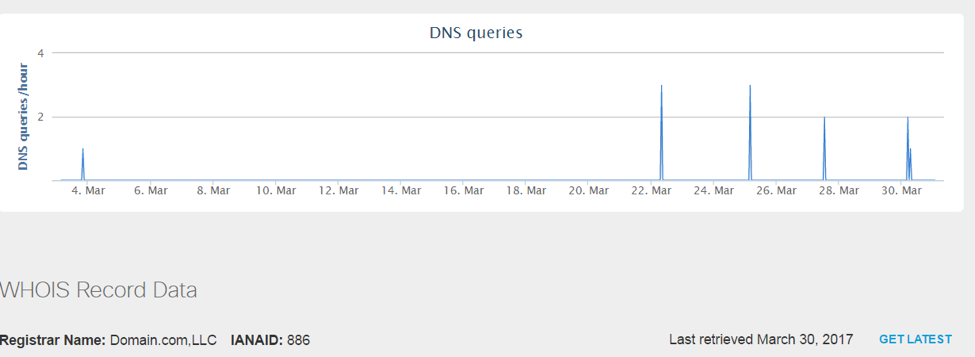
Using Cisco Umbrella Investigate, I was able to investigate each domain for DNS queries and intelligence.
With this additional intelligence, we were able to empower the SOC team members to confirm no malicious traffic was going in or out of the network to this CnC infrastructure.
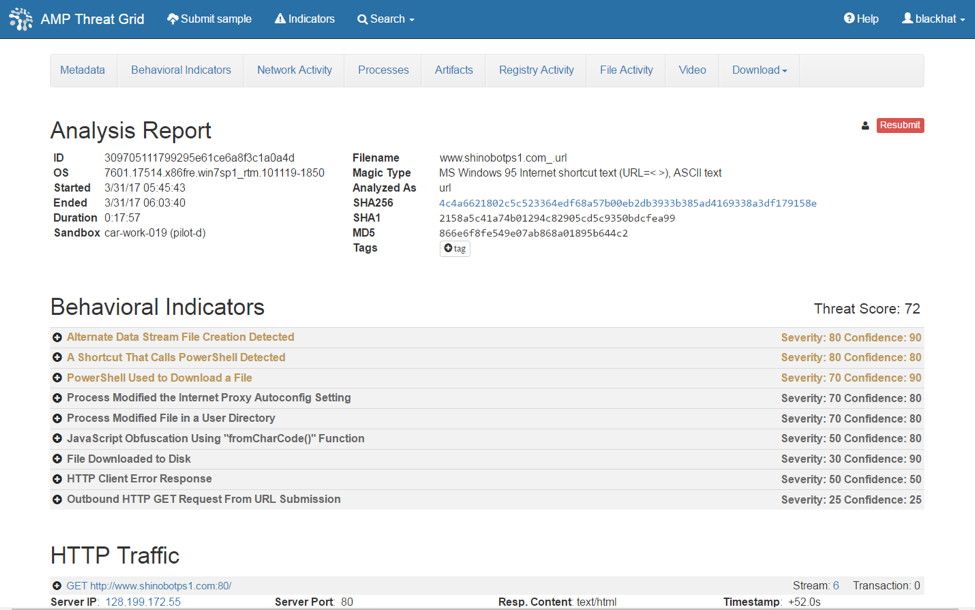
A search of the Black Hat speakers determined that Mr. Shota Shinogi is a security researcher, pen-test tool developer and a pen-tester. His hobby is to find out how to bypass security solutions. I found Mr. Shinogi at the Black Hat Arsenal booth. He has a new version that utilizes PowerShell, so no file is dropped on the disk. He has a website to deliver the PS1 to the endpoint via a link file. The exploit has total control over the endpoint and bypasses traditional endpoint detection. I was able to submit the URL to the Threat Grid Glovebox and simulate the drive by attack. The resulting endpoint behavior and CnC is below.
Black Hat is about sharing and it was great to engage with Mr. Shinogi in a discussion of the detection and further collaboration as security professionals. It was a wonderful conference and I enjoyed being part of the Black Hat SOC team. From the conversations with the SOC leadership, we determined it would be beneficial to bring in Cisco Umbrella to have visualization and statistical analysis of the DNS queries and traffic of the Black Hat conferences. Cisco will sponsor Black Hat with the technology beginning Black Hat USA 2017. See you in Vegas!