There’s been a lot of big talk about IoT for the past several years, and I admit, I’ve been skeptical.
Thermostats. Toasters. Fitness trackers. So what? Why is this so transformative for Cisco’s customers?
I wanted to understand this “transformation” more deeply. So, I read every report I could get my hands on. I talked to our customers, partners, academics, and other IoT experts. I even looked back at the history of IT itself.
Here’s what I learned.
IT has fundamentally transformed business twice in the last 50 years. First, in the 1960s, the entry of computers and IT into business changed processes and activities. Then, in the 90s, the introduction of the “Information Superhighway” connected processes and activities together.
Now we are entering the third era — the Internet of Things. However, I believe the term “Internet of Things” is fundamentally misleading. It’s not so much about the Internet, which is just a mechanism for transmitting information. It’s actually about the changing nature of the “Things” themselves. The true power of smart, connected Things and the data and insights they generate will create the next era of business.
To be clear, by “Things,” I do not mean smart phones or tablets. I mean everyday Things – from pillows to snow plows, from turbines to tents, from whistles to wind farms. These are the Things our customers make. And these Things have remained largely unchanged, despite how IT has transformed business processes and productivity for the past 50 years.
What we are seeing now is a shift in which IT becomes a fundamental part of a company’s products, not just that company’s operations. Thus, the real magic of IoT will be inside the products themselves.
IoT is underhyped – Yes, underhyped.
IoT is producing tangible business outcomes – today. Just ask the automakers. GM will net $350 million in net new revenue for GM over the next three years using Cisco Jasper to underpin all of its connected car offerings in all new vehicles to provide entertainment, safety, vehicle diagnostic capabilities and other services.
And this is just the beginning for GM and others. In Q1 of this year, new cellular connections in cars surpassed new cellular phone connections, (source: Chetan Sharma) – incredible. In fact, Cisco is working with over 50 brands from 23 different auto manufacturers, and industry forecasts predict that by 2025, all vehicles will have connectivity built in as standard.
Cars, elevators, beer kegs, and literally every other product in the world could be affected. This will transform business models, and I believe there’s a real opportunity for IT to go from a cost center to a revenue generator as its company’s Things become connected.
 At Cisco Live this week, I outlined several ways that we’re making it easier for IT to take advantage of this unprecedented shift by addressing the following challenges:
At Cisco Live this week, I outlined several ways that we’re making it easier for IT to take advantage of this unprecedented shift by addressing the following challenges:
- Connectivity – How does IT connect everything, identify and authenticate devices and then handle the volumes of data that result?
- Data Intelligence – Today’s networks tend to be focused on connecting systems, whereas future networks will be data, information and resource-based. Increasingly, IT will need a higher-level view of the network to make it more consumable and robust for IoT services. So we are looking at how data flows can enable intelligence and analytics.
- Security – The other major inhibitor to IoT success today is security. We are taking a secure end-to-end approach to help customers evolve their existing networks to cope with this influx of new devices, users and data flows.
Cisco offers numerous solutions today to help. We recently announced several new industrial IoT solutions that provide a highly secure architecture for connected factories, and help eliminate unplanned downtime by bringing IoT to connected machines.
We also have new, incredibly powerful IoT Cloud solutions through our acquisition of Cisco Jasper. The Control Center solution from Cisco Jasper is being used to monitor, manage and control cellular connected devices for use cases as diverse as optimizing route planning in logistics to a farmer knowing exactly when a cow is about to give birth.
Get IoT today
 We know getting started may feel daunting. That’s why we launched an IoT Starter Kit with AT&T today, and we invite you to take the tour.
We know getting started may feel daunting. That’s why we launched an IoT Starter Kit with AT&T today, and we invite you to take the tour.
The kit provides provides everything needed – including hardware, software and services – to help developers take advantage of next-generation 4G LTE connectivity and start developing new IoT services. This also includes a major evolution of the service development model with six months of IoT data services for new customers. This is the most advanced starter kit available today!
While the opportunity is real and here now, only 7% of IT managers report having an effective IoT strategy. I cannot wait to take this journey with the other 93%.

 Video now accounts for the majority of global mobile data traffic and is forecast to be the key driver of data traffic growth globally. To date, mobile video (and the ability to monetize the content) has been dominated by Internet players, such as YouTube, Netflix, with the operator role simply one of connectivity provider.
Video now accounts for the majority of global mobile data traffic and is forecast to be the key driver of data traffic growth globally. To date, mobile video (and the ability to monetize the content) has been dominated by Internet players, such as YouTube, Netflix, with the operator role simply one of connectivity provider.
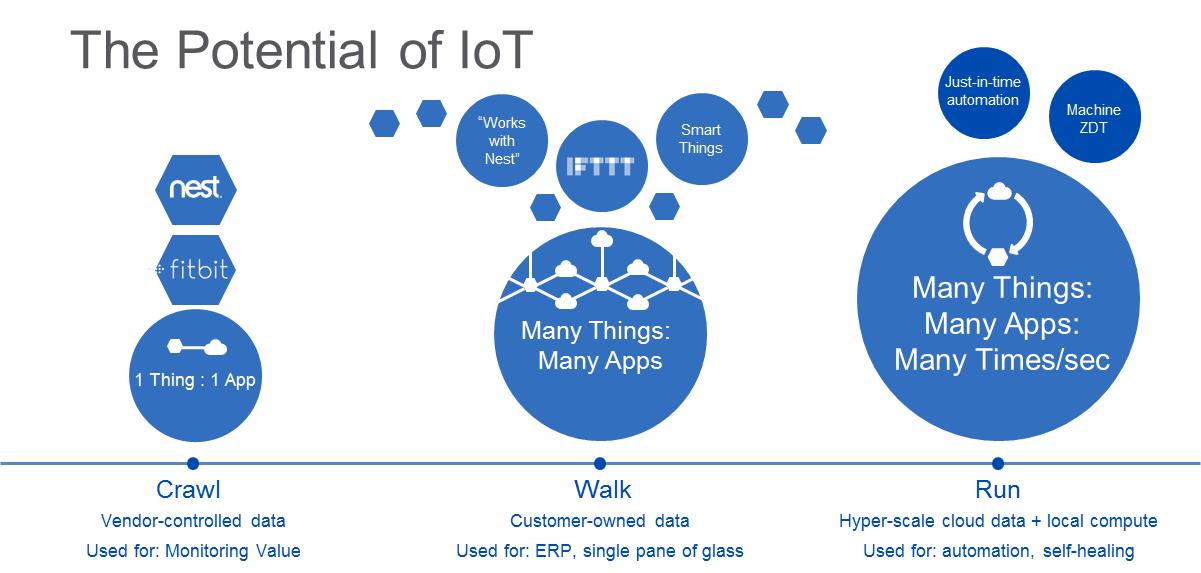
 Crawl: Data goes from one thing to one app.
Crawl: Data goes from one thing to one app. Walk: Data can be exchanged from many things to many apps.
Walk: Data can be exchanged from many things to many apps. Run: Many things to many apps, many times a second.
Run: Many things to many apps, many times a second. distributed and remote data, to solve critical challenges in multiple industries like energy, manufacturing, and financial services. Until now, IoT data has been managed in centralized, cloud-based systems. In traditional settings, data is moved from a connected ‘thing’ to a central system over a combination of cell-phone, Wi-Fi and enterprise IT network, to be managed, secured, and analyzed.
distributed and remote data, to solve critical challenges in multiple industries like energy, manufacturing, and financial services. Until now, IoT data has been managed in centralized, cloud-based systems. In traditional settings, data is moved from a connected ‘thing’ to a central system over a combination of cell-phone, Wi-Fi and enterprise IT network, to be managed, secured, and analyzed. you’ll be able to get an in-depth view of this solution, Cisco’s ongoing data and analytics innovation and more when you join us at the
you’ll be able to get an in-depth view of this solution, Cisco’s ongoing data and analytics innovation and more when you join us at the  a modern container terminal in the Caribbean, are using Cisco Edge analytics and the Watson IoT Platform to expand its monitoring of equipment conditions such as engine temperature, engine speed and run hours to improve maintenance costs. Bell Canada is pushing the edge with analytics to deliver 4G LTE connectivity throughout the country, regardless of the location of the business.
a modern container terminal in the Caribbean, are using Cisco Edge analytics and the Watson IoT Platform to expand its monitoring of equipment conditions such as engine temperature, engine speed and run hours to improve maintenance costs. Bell Canada is pushing the edge with analytics to deliver 4G LTE connectivity throughout the country, regardless of the location of the business.