Hello! My name is Kevin Wood, and I am a retail business architect here at Cisco for both Retail and Hospitality. I have done a lot of work providing security to retailers – one of the most vulnerable industries in the world today.
We all know that staying ahead of security threats is a dynamic and rapidly growing challenge. Since your retail business has to handle cardholder data, run Wi-Fi networks, and manages email and other private transactions, maintaining security and staying compliant is a critical factor in your success.
For most companies, detecting the average breach can take more than 200 days with point security solutions, and 60 percent of data is stolen in the first few days. What is this costing you?
- Statistically, there is a 26% chance you will have a material data breach involving 10,000+ lost or stolen records
- The average total cost per data breach is estimated at $4 million
- We are seeing a 29% increase in the total cost of data breaches since 2013
- The largest financial impact is lost business due to lost customer trust, which can run up to millions and last for years
At the same time, hackers are reselling your information for a profit. Here are some of the going rates for your data on the black market:
- Data Exploits: From $1,000 to $300,000
- Credit Card Numbers and Data: $0.25 to $60 per record
- Malware Development: About $2,500
- Facebook and Social Media Accounts: About $1.00 per account with 15 friends
- $34M/year income from ransomware per campaign
As the number of exploits increases, they may occur in the store, in the hotel, across the network, on the mobile device, or through mistakes made by well-meaning but uninformed employees. Today, hackers cost our global economy about $1 trillion per year.
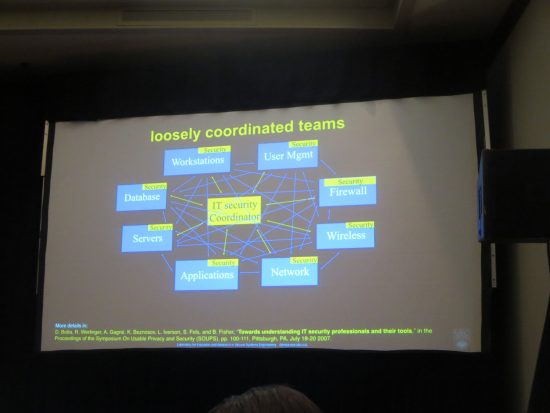
What can you do to protect your organization? Deploy network security that underlies every single thing your company does – from customer welcomes to operations management – to protect you no matter what the threat. This integrated approach also has the benefit of making your system less complex and fragmented, and thus easier and cheaper to run.
Cisco gives the network the ability to protect itself and its data at any point before, during, or after an attack. Let’s look at some examples of how a threat defense strategy can detect and mitigate events.
Data Loss Prevention Before the Attack
In this scenario, a valid employee device is the source of a data leak. A valid corporate asset is compromised unknowingly by a hacker or malware. The device starts to send large amounts of data outside of the network. By leveraging the threat defense strategy utilizing tools such as LanCope, we already know the typical behavior for that device and that user. When a traffic pattern change is detected, an alert is sent to network administrators while the intelligent network automatically takes the device offline.
Unauthorized Device Access During the Attack
A hacker decides to steal cardholder data or corporate data from a store chain network. He accesses an employee’s permissions by “eavesdropping” on their device to gain their username and password. Once credentials are obtained, he uses a client or mobile device to log in to the network. However, the network has prior knowledge of approved users and devices. When the hacker tries to join the network, access is immediately blocked since the device itself is not authorized to join the network. Even though he had the credentials, the hacker’s incorrect device alerted the system to his illicit attack, before any access was granted. Who said that switch security isn’t important?
Malware and Vulnerability Detection After the Attack
A new piece of ransomware has been placed on an approved device. Without quick action, this malware will spread and lock the store out of its data. However, the store has real-time, up-to-date research on vulnerabilities and alerts thanks to Cisco’s Threat Grid and Talos organization. Talos provides multiple daily security information feeds into Cisco Firepower, allowing them to identify new threats and quarantine them on the fly. The system’s quick action can save thousands, if not millions, of dollars and lost man hours.
The philosophy of continuous security has been hugely successful for retailers working with Cisco, allowing them to reduce breach detection from 200+ days to just 17.5 hours. This gives you every chance to detect, identify, and manage potential problems across the business – minimizing issues or making them completely transparent to shoppers and guests. To learn more about our Before, During, and After security methodology, go here.
Follow us on @CiscoRetail or Facebook, and join our Cisco Retail LinkedIn Group.