Every year the Symposium on Usable Privacy and Security brings together an interdisciplinary group of researchers and practitioners in human computer interaction, security, and privacy, to present and discuss the latest research in the areas of usable security and privacy. Cisco’s sponsorship of SOUPS supports student research and mentorship in this area (see below), as well as leadership by providing the General Chair (me). Here is some of what SOUPS provided this year in privacy and security innovation.
FTC Chief Technologist Lorrie Faith Cranor covered her initiatives in privacy and security policy to date within the FTC. Most recently, she discovered that your mobile phone account can be hijacked by an identity thief with just a fake ID with your name on it, and knowledge of your phone number. How did she discover this? She was the target of exactly that attack. “I called the fraud dept. The first thing they did was blame me, saying you haven’t updated your anti-virus software.” Which turns out to be entirely incorrect.

Want to know what information would be left on Twitter about you if you were to remove your twitter account? Try out twitter-app.mpi-sws.org/footprint/. It shows information leakage from others about you on Twitter. “Forgetting in Social Media: Understanding and Controlling Longitudinal Exposure of Socially Shared Data” is the first study that kind of of information leakage of residual activities of deleted tweets and accounts.
“Snooping on Mobile Phones: Prevalence and Trends” (Distinguished Paper winner) quantified the prevalence of looking through someone else’s phone without their permission. With an estimated 31% of the online participant pool doing so within a 1-year period, weighted to the U.S. population, 1 in 5 people snooped on someone else’s phone in the previous year. Snooping attacks are especially prevalent among young people, and the more people use their devices for personal purposes, the more likely they are to snoop on others.
Brigham Young University surveyed 1,976 individuals on “User Attitudes Toward the Inspection of Encrypted Traffic“, and found that most of them recognized legitimate uses of this practice. Legitimate uses included protecting organizations, protecting individuals, and law enforcement and surveillance. There was also strong support for notification and consent; adding it generally doubled the number of individuals supportive of the practice.
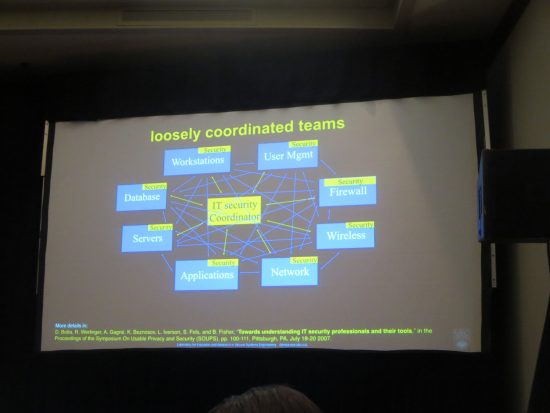
A full day Workshop on Information Security Workers explored research in making security professionals of all kinds more effective, efficient, and productive. A study on penetration testing’s impact on software developers shows it increases developer awareness of security, but in itself does not create long lasting change in developer practice. A survey of cybersecurity competition participants shows their experience built up their reverse engineering and analytic skills, and positively influenced their career decisions to move into cybersecurity. The plenary overview of a multi-year empirically-driven investigation into understanding and improving IT security include an overview of the complexity of the communication patterns for IT security management, across multiple loosely coordinated teams. The sense of the workshop is that these complex communication needs have not changed much in the last nine years.
“Follow My Recommendations: A Personalized Privacy Assistant for Mobile App Permissions” (IAPP Privacy Award winner) built on prior work showing that it is theoretically possible to predict many of the privacy settings a user would want by asking the user a small number of questions. In a field study, they assigned users to privacy profiles based on existing permissions and up to five contextual questions. 78% of the recommendations then made were adopted by users.
“Understanding Password Choices: How Frequently Entered Passwords Are Re-used across Websites” measured online behavior of 134 participants over 6 weeks. They found people reuse passwords that are more complex, and mostly reuse passwords that they have to enter frequently. In the student population, their university password was the most commonly reused by far. The findings suggest that users manage the challenge of having many passwords by choosing a complex password on a website where they have to enter it frequently in order to memorize that password, and then re-use that strong password across other websites.
Other papers and posters covered privacy, security and safety concerns of visually impaired people as input to design considerations for future wearables, the privacy perceptions of drones, what kinds of sounds signal cyber threats well to the visually impaired, and efforts on an interactive privacy patterns catalog.
Supporting education and research to increase the pool of talent working in cybersecurity, Cisco sponsored the inaugural John Karat Usable Privacy and Security Student Research Award. The award honors Karat’s contributions to the usable privacy and security community, and his dedication to mentoring students. The winner was Blase Ur of Carnegie Mellon University, whose breadth and depth of mentoring is sure to inspire the next generation of security professionals. We look forward to benefiting from the future work of all the student nominees as they begin their young careers in privacy and security!






Thanks for reporting of this interesting event. When looking at their website, there are many papers that are worth reading.
Thanks for all this great information. I am going to review the a papers and would be very interested in attending a future conference.
Excellent report! I’ll put SOUPS on my short list of trainings to get to next year