When I think of data protection, I think of it like the protection of our homes: We know burglars may be out there “watching” us where we live, picking up on our daily patterns and scouring our home’s exterior to find the easiest way “in.”
Acknowledging this, we buy door and window locks, alarm systems and perhaps even security cameras. With these safeguards in place, we can then prepare for incidents that require quick, decisive action by assessing all possessions in the house and prioritizing their value – what do you need to save first if your house catches fire?
Enterprise data protection is much like that: We know the bad guys are watching, scheming for a way to compromise our network and systems. We develop a strategy for the implementation of modern cyber defense tools. Then, we inventory our data to prioritize what is most mission-critical and/or potentially valuable for our adversaries to target, and therefore identify that which demands the greatest attention.
A sampling of recent research reveals that enterprises need to focus on putting their data protection “house” in order: There were more than 1.9 million data records lost or stolen every day in 2015 – at an average cost of $158 per record equating to $300 million per day. Malicious outsiders account for nearly three of five breaches, with the remainder mainly attributed to accidental loss.
With the expected boom in the Internet of Things – an estimated 500 billion devices will be connected by 2030 – hackers will have more attack vectors to exploit. Organizations must respond with data protection programs that take advantage of tools that are easy to deploy. These programs must seamlessly navigate within on-premise and cloud-based environments, providing security teams the insight to make quick connections to potential incidents – and immediately act upon them.
Cisco’s Data Protection Program focuses on eight key elements: Policies and Standards; Identification and Classification; Data Risk and Organizational Maturity; Incident Response; Oversight and Enforcement; Privacy by Design and International Privacy Policy; Security by Design and Data Loss Prevention; and Awareness and Education.
Last week I shared case studies on the elements of our Data Protection Program at Cisco Live U.S. in Las Vegas. Here’s a recap of a few of those areas – Incident Response, Oversight and Enforcement and Awareness and Education.
Incident Response – Cisco’s incident response process is integrated with business continuity plans enterprise-wide. Time is of the essence when corporate or customer data is at risk, so Cisco’s Computer Security Incident Response Team (CSIRT) members are monitoring 24×7 and providing the initial triage of possible incidents in swift, systemic fashion. Whether it’s a training video on YouTube or unintentionally compromised employee credentials, the team is fully prepared to investigate and respond to potential data leaks.
Oversight and Enforcement – There is ongoing, internal governance of the Data Protection Program, which includes policy adherence monitoring, remediation, third-party vendor management and, when appropriate, engagement with the Cisco Board of Directors. IT and business leader’s work together to ask questions like:
- What data do we have access to?
- Why is the data important?
- How can we segment and protect what matters most?
With this information we are able to prioritize data, so defense layers’ are assigned accordingly.
Awareness and Education – Data protection isn’t only about technology solutions. It’s about people too. Employees at all levels of the enterprise must understand their role in the process, and the need to focus on creating a security and privacy-aware culture. Security must to be part of the fabric of the organization, using education and best practices during all activities where data could be breached. The ‘think before you click’ mentality.
Like all companies, we feel the pain of adversaries seeking to “break in” to our house. Our Data Protection Program is a “cybersolid” foundation that provides the framework and processes to ensure we keep the bad guys out. Our number one goal is to protect the security, trust, privacy, and resilience of Cisco, our partners and customers. Let us lead the way and keep the lights on. For more information on Data Protection at Cisco, visit https://trust.cisco.com.
Michelle Fleury is a Senior Director and the Chief Data Protection Officer at Cisco.



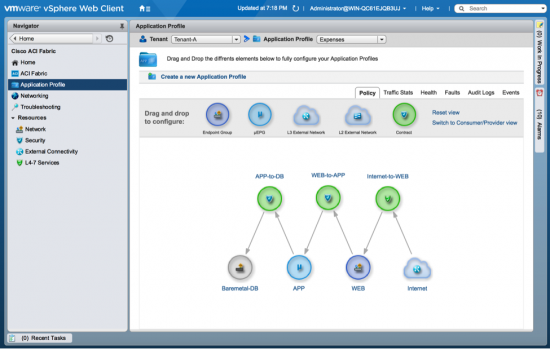

 Consistent Experiences Across Clouds
Consistent Experiences Across Clouds 
 This weekend, I evinced a big change in my youngest daughter. She emerged from her summer couch potato cocoon and blossomed into an active youngster chasing after fictional creatures in natural sunlight. Within 2 days of its launch, Pokémon Go had number of users almost at par with Twitter, the popular social media network that has been around for more than 10 years. What does this latest of mobile gaming phenomenon have in common with the latest
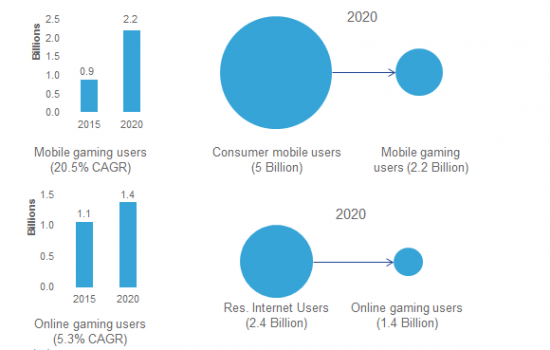
This weekend, I evinced a big change in my youngest daughter. She emerged from her summer couch potato cocoon and blossomed into an active youngster chasing after fictional creatures in natural sunlight. Within 2 days of its launch, Pokémon Go had number of users almost at par with Twitter, the popular social media network that has been around for more than 10 years. What does this latest of mobile gaming phenomenon have in common with the latest  VNI service adoption research also projects that out of the 8 consumer mobile applications that we track, mobile gaming will be one of the higher growth services with a healthy 20.5% compound annual growth rate (CAGR) from 2015-2020. The number of users for mobile gaming will grow 2.5-fold during this period. This growth is driven by improved hardware performance; launch of new form-factors, new interactive, social media integrated as well as VR augmented games.
VNI service adoption research also projects that out of the 8 consumer mobile applications that we track, mobile gaming will be one of the higher growth services with a healthy 20.5% compound annual growth rate (CAGR) from 2015-2020. The number of users for mobile gaming will grow 2.5-fold during this period. This growth is driven by improved hardware performance; launch of new form-factors, new interactive, social media integrated as well as VR augmented games.