More than ever before, today’s consumers have more options about what to buy and where to buy it. With each interaction, they choose which retailers they support with time, attention, personal data, dollars and social capital. That’s no small investment to make, and as a result customers turn to retailers and brands that not only sell the products they want, but deliver the end-to-end experience they want.
Working with our research partner PSFK, Inc., Cisco has identified four key capabilities that support the customer experience while enabling today’s digital transformation. We discuss these capabilities in a recent joint paper on the “Retailer of the Future.”

1. Customer Mobile Experience
Today’s retail industry is shifting from how to acquire customer data to how to extract insights from it – insights that can be turned into differentiation and competitive advantage for the retailer and a better experience for consumers. Customers can shop more efficiently, get mobile help when they need it, receive targeted offers, and gain immediate access to product information. The data you gather also helps to build strong, long-term relationships with shoppers, while respecting trust boundaries, and increasing your revenue opportunities.
2. Associate Productivity
One of the key opportunities of digital transformation is the chance to reduce operating costs by improving staff performance. Today’s mobile capabilities don’t only serve your customers – they also enhance the quality and efficiency of the workforce experience. These associate productivity solutions help create an optimized work environment staffed by productive, agile personnel who work from anywhere and collaborate within and outside your organization.
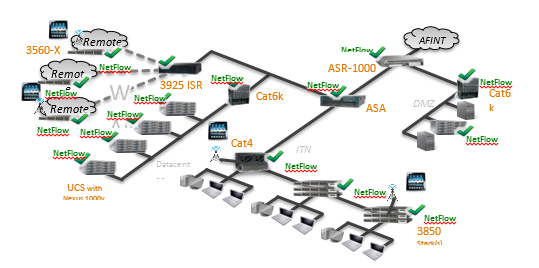
3. Security
It’s said that there are just two types of companies: Those that have been hacked, and those that just don’t know it yet. Retail stores are among the most vulnerable targets for hackers. In such an environment, retailers must take extraordinary measures to protect customers, associates, and stores. A strong, multi-layered defense of data, networks, and devices not only helps to protect your operation, but it spares you the high cost of the damage to the brand and its reputation.
4. Unifying Retail
In this digital age, you must balance customer demands for more personalization and digital services, operational demands, requirements for unified commerce and opportunities for new stores or formats. Unified computing platform address this challenge by consolidating and running critical store functions on a single, integrated system. Services may include security, mobility, networking, video on-demand, video surveillance and loss prevention, cloud connectivity, wireless, retail applications, and many others.
Becoming the Retailer of the Future
Utilizing these four capabilities enables the “Retailer of the Future”: Enterprises that have transformed shopper experiences, platforms, and cost models to completely disrupt their business. Building on a foundation of differentiation and innovation, you are positioned to capture the hearts and minds of today’s shopper. Loyalty becomes synonymous with membership, offering access to a broader set of services, perquisites, and connections.
To learn more about current trends and how you can implement the customer experience, please download our new paper “The Future of Retail.”
https://www.youtube.com/watch?v=M1MPiFEJ0S8&list=PLE122E9E4108CAEBE&index=5