The concept of no-touch automated bookings is a very straightforward one: How do we reduce the need to “touch” or spend time and energy on the low-dollar contracts that we renew in the market? How do you enable a sales team to focus on the larger revenue opportunities and still drive solid renewal capture in the low-dollar space? And how do we automate the revenue capture from that segment of the contract opportunity?
Watch the On-Demand Webinar: Renewals for Low-Value, High-Volume Customers
The reasons to aggressively pursue this strategy are simple: automated revenue is lower cost and higher margin revenue.
Pursuing a low-dollar renewal automation strategy is smart and necessary. However, the very fact that these service contracts require a renewal event – a defined period after initial purchase when the contract expires and must be manually renewed (by human hands or platform automation) – is, in fact, a strategy that must be evolved even further. The very act of having to pursue and capture a renewal of these agreements is an outdated concept and strategy. We need to think bigger.
The Power of Recurring Revenue
There has been an unrelenting shift in IT over the last decade toward recurring revenue business models – selling IT products and services on perpetual, or recurring contracts. These are contracts with no defined end date – meaning the contract entitlements do not end or expire.
A recurring revenue or subscription model is defined as a product or service that is delivered to a specific expectation for a defined period of time (or unlimited period of time) for a specific dollar amount per month or year (subscription fee). This subscription fee might be fixed or variable, depending on the terms of the product or service being delivered.
We are all familiar with these types of contracts: SaaS subscription software licensing, cloud computing models for storage and backup, and content streaming services such as Netflix and Hulu. A monthly gym membership is an example of this type of service contract. There are even commodity products being sold in this manner, such as Dollar Shave Club.com. These revenue models are typically called “subscription revenue models” or “recurring revenue models.” You can check out my deep dive on the economics of recurring revenue in my post here.
What are the true value drivers of such a revenue model for the companies that invoice revenue this way? The significance of recurring revenues and the importance of the recurring nature of those revenues to the companies that earn them cannot be understated.
Perpetual Contracts Deliver Recurring Revenue
The concept of a perpetual contract is simple: It is a contract with no specific end date. If linked to a hardware product, it may have an end date at the end of life of the equipment it covers, but otherwise there is no set expiration of contract entitlements so long as the customer is current on their payments against the contract.
Basically, a perpetual contract is a subscription contract – payments can be structured to happen every month or annually. The important thing is that the contract does not end and then necessitate a costly and logistically complex effort to renew or re-capture that contract. The customer is automatically billed each contract term. If the customer stops paying, the contract terminates (perhaps with penalty fees or other such restrictions) and the entitlements go away.
Perpetual contracts and recurring revenues are where every IT provider is headed – there is no choice. This is not optional. It’s critical that we continue to evolve to a model where service contracts, and other offerings, behave and are structured in similar ways as subscription software offerings and cloud service contracts are structured – as recurring, or deferred revenue.
The Move Toward Deferred Revenue
Deferred revenue is revenue booked today, but recognized over a future period of time. What does that mean? Let’s say I sell a two-year service contract today, and the customer pays me for the full two years up front. I can book the two-year revenue total today – meaning I can tell Wall Street that I got the money and can account for it as booked revenue. However, because the value of the contract will be delivered to the customer over a future period of time – in this case two years – I cannot recognize the full booked value in revenue immediately – I must defer the revenue, or recognize the value of the contract over the period of time in which the contract entitlements are being delivered to the customer.
In the two-year contract example above, let’s say the customer paid me $24,000 (upfront) for the two-year contract. I book the $24,000 today and that money sits on my balance sheet as deferred revenue. Because the contract terms is 24 months, what I must do is defer the revenue recognition over the 24 months. One option to do this would simply be to recognize 1/24th, or $1000, of revenue each month over the 24-month contract term.
Why Is Deferred Revenue So Important?
Deferred revenue is critically important to a business because it is contracted over a future period of time and guarantees a future revenue stream that the business can forecast and count on. These contracted revenue streams are highly valuable, and a company is worth more if it can demonstrate large contracted future revenue streams. Contracted future revenues also make it easier to make investments in the business and plan for growth.
Deferred revenue, and the transition to deferred and recurring revenue streams, also poses challenges for businesses that have traditionally booked and recognized large amounts of revenue up front, such as selling hardware and other transaction oriented offerings. Why? Because the company typically suffers a loss of up front revenue in favor of longer-term deferred or subscription revenues.
Let’s use the $24,000 contract example above to illustrate this concept of the balancing act that companies must manage through this deferred revenue transition.
Suppose I have a choice to sell either a piece of hardware worth $24,000 to a customer today, or a two-year subscription revenue contract to a customer for $24,000 dollars. If I sell the hardware, I get the $24,000 today and can recognize the entire $24,000 of revenue today as well. My current revenues look strong in this model and I have also generated cash today.
If, instead, I sell the service contract for $24,000, I can record $24,000 of booked revenue today, but must defer revenue recognition over the 24-month term. So my up front revenues don’t look as strong, even though I have strong deferred revenues, typically at higher margins. The deferred revenue stream is actually more valuable to the company because it is higher margin and demonstrates contracted future revenues, but my lower current revenue number needs to be managed carefully so that I am not punished by analysts and other short-term revenue dependent measurements. I also have lower cash to work with today, since I cannot recognize the full revenue up front, so cash flow and other cash-dependent metrics need to be managed carefully through this transition.
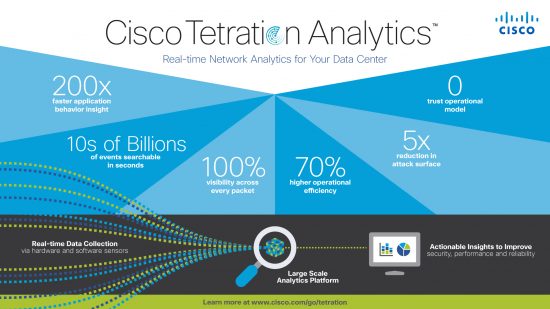
Getting Out Ahead of the Market Transition
It’s clear that recurring, subscription and deferred revenue offerings are growing, both in prevalence and importance. Their potential for partners is powerful, but they also create new levels of complexity. As we all make the transition, the challenge is to keep pace with current contract vehicle types while preparing for requirements that future contract types will demand of us. One thing is clear though – digitization and automation of business practices are going to play an essential role in the transition and beyond. Cisco recognizes this and is investing in programs to help partners adapt. Innovative, data-driven platforms such as Cisco Impact and AutoQuote are already helping partners transition to the new economy and digitize customer engagement. Powered by data-driven automation, these tools and others can give partners entirely new capabilities and a leg up for capturing recurring, subscription and deferred revenue — and competing more effectively as the dynamics of the market are changing.
The age of perpetual contracts is here. Are you ready?