The Enterprise Strategy Group (ESG) conducted research into how cybersecurity professionals view network security monitoring and how they use it in their organization. The report Network Security Monitoring Trends surveyed 200 IT and cybersecurity professionals who have a knowledge of or responsibility for network security monitoring. Some of the key findings include:
- Many organizations now understand the value of network telemetry
- Large organizations collect large amounts of security data but there’s still an opportunity realize its full value
- While network security monitoring is highly valued, practices remain fraught with challenges
- CISOs have aggressive network security monitoring plans for the next few years
Jon Oltsik is an ESG senior principal analyst and the author of this study. We sat down with him to discuss the significance of the findings and the important role network security monitoring plays in today’s cybersecurity market.
How do security professionals currently perceive network security monitoring?
They perceive it as a very important component of their overall security strategy. Eighty percent responded and said network security monitoring is critical to their overall security strategy, and 17 percent said that network security monitoring is important (but not critical) to their organization’s overall security strategy.
So they view monitoring network traffic, understanding network traffic, and being able to detect anomalies as really important to the overall mission. In the past, some companies understood this, but it was largely overlooked.
Why do they view it as so important in today’s threat landscape?
The beauty of network security monitoring is there are a lot of different use cases that can have a drastic effect on security if used properly. For instance, 42 percent of the people we surveyed said they used network security monitoring for proactive querying of the network – really hunting for suspicious behavior. We see more and more organizations, especially large ones, investing in hunting capabilities. You need those clues from the network to understand where the network traffic is flowing, from what devices, and to what external IP addresses. Is there anything anomalous about the traffic? Can I relate or correlate those responses to what is happening in the wild with threat intelligence?
Network security monitoring provides this rich repository of information on what everyone is doing, and from that, you can gauge what is normal and abnormal. If you have the right tools or people in place, you can dig further into investigating anomalous behavior or fixing problems.
What are the challenges to successful network security monitoring?
There are a number of challenges that we found in the research. Seventy-two percent of companies we interviewed said network security monitoring is more difficult today than it was two years ago. Some of this can be attributed to an increase in malware volume – 34 percent said that – and 28 percent pointed to an overall increase in network traffic.
Gaining comprehensive visibility was mentioned as a specific challenge, with 31 percent of organizations indicating they had one or several network blind spots. While they monitor network traffic, there are areas of the network or particular workloads that they can’t see or don’t see very well. That makes it hard to get an end-to-end view of network security.
Twenty-nine percent said there were communications and process issues between the cybersecurity and network operations teams. That is an organizational issue. Network security is really a cooperative endeavor between security and network ops, and maybe they’re not using the right tools or communicating or collaborating well on processes.
Twenty-five percent said they don’t always collect the right data at the right time. Network security data as well as threat intelligence is all about timing, so to detect things quickly, you need timely data. Sometimes they are sampling data, sometimes there aren’t the right sensors in the right place, and sometimes they don’t know what to look for.
Due to the complexity of what they’re after, sometimes there are a lot of challenges across people, processes, and technology. But CISOs appear intent on addressing these issues – 41 percent of organizations say they will significantly increase their investment in network security monitoring, and another 50 percent say they will increase investment somewhat.
You mention issues between security and network operations, how can we address this disconnect?
The greater emphasis on network telemetry is very good because it is a source of truth for both the security and networking teams. Both organizations understand that data. If the data is pointing to a particular host IP address, both organizations can relate to that. If it is talking about rogue connections, rogue traffic, protocols, or encryption that is happening on the network that shouldn’t, both organizations can interpret that data and have it as a common source of truth.
To the extent that we can have those groups collaborate better, we’ll make improvements. Workflow improvements will help. There are tools like ticketing systems to track the problem of detection and remediation of events. But it is important to start with a baseline that everyone understands, and network telemetry can provide that.
Going back ten years, there was a market called network behavioral anomaly detection (NBAD). Those tools were purchased by the security teams, but I noticed that often after the purchase, they were used extensively by the network ops team. I think we are just seeing the fruition of that kind of telemetry in the tools we have today.
What kind of data sources are being used for network security monitoring?
There is a legacy aspect to this in that people have always collected data at the network perimeter – things like IDS/IPS and firewall logs. SIEM tools used to be pointed at those sources. So we are looking at data ingress and egress in the network. That is still important, but it doesn’t give a complete view of network activity. I would say people are now looking much broader at traffic across their network, including internal networks, WANs, and remote offices to get a better understanding of what is going on.
Some of the tools they are using include telemetry like NetFlow, packet capture, and endpoint forensics. There are more data sources now than in the past, and there will be more as computing gets more and more complex and diverse.
What data sources should organizations look toward for future network security monitoring?
Historically, we looked at log data, and we still should. But network telemetry is generally the next step that people take. In the past, it was based on NetFlow, but it has gotten broader than that. It’s NetFlow, it’s packet capture, it’s looking at recursive DNS traffic. Probably the next two things after that are threat intelligence and endpoint forensic data. With that, I can equate what is happening on the network with what is happening on the host and I can compare both of those things to what is happening in the wild. That gives me the right touchpoints to do pretty good analysis.
Looking forward, what are the key ingredients for successful network security monitoring?
Workflows are going to the cloud, and we need eyes and ears in the cloud. The tendency is to do that discreetly, and that really is not helpful. We need our existing network security monitoring technologies to also be able to view cloud connections in a consistent way so we can then apply our analytics and best practices. Part of that is just instrumenting more and more points of data collection. For instance, network security monitoring is generally associated with core networks or data centers, but we have to expand on to access networks, distribution networks, WAN connections, and local area networks in branch offices. Eventually we’ll probably exchange some of the telemetry with our business partners too. So if I am a manufacturing organization and I have ten key suppliers, I may want to exchange that information with them as well to get a better picture of our inter-IT environment.
What should organizations keep in mind when building their network security monitoring capabilities?
There are a few things to keep in mind. One is if they don’t have experience with network security monitoring, they should look for a phased approach where they address some really burning issues in the short term, learn the tools, establish some processes, establish some success metrics and then apply them broader.
They should also view network security monitoring as something they want to integrate with some other types of technology such as endpoint security monitoring, threat intelligence, SIEM platforms, security analytics, and some of the machine learning behavioral-type stuff that is going on. You want to understand the network – and many security and networking professionals do – but you want to be able to correlate that with what is happening elsewhere for better situational awareness.
Was there anything from the research that stood out to you?
I’m pleased to see in the research that there is a clearer understanding what network security monitoring is compared to other types of monitoring and analysis tools. In the past it wasn’t uncommon for something like Stealthwatch to compete with tools like HP ArcSight or Splunk, which are really different tools for different purposes, and the fact that many companies confused those was disheartening.
Now, there is a clear understanding that network security monitoring is an important component and we see that it is the first place people go beyond SIEM. And they typically have a strategy that goes beyond network security monitoring alone that includes things like threat intelligence and endpoint monitoring. The future is continued broadening of the visibility, broadening or integration of the tools, and probably more intelligence solutions – machine learning algorithms and that kind of stuff, but it will take a while before these things come to fruition.
How does Stealthwatch, the Identity Services Engine, and the rest of Cisco security portfolio fit the needs of network security monitoring?
I think it fits very well. On one hand you have telemetry and actionable intelligence with Stealthwatch and the integration with the Identity Services Engine (ISE) gives you some remediation capabilities. I know Cisco talks about Network as a Sensor and Network as an Enforcer, and I think that those two things are starting to be understood more and more. Not only are they important independently but there is an intersection point where you get more value.
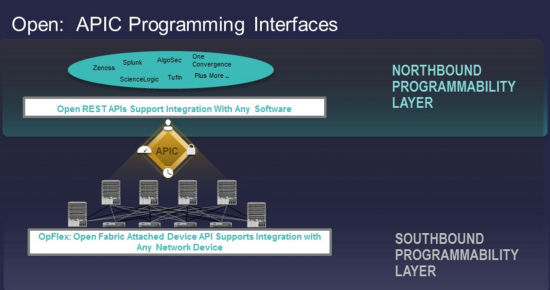
With Stealthwatch, it’s not a new technology, it is a mature technology with a good entry price and install base. The people from Lancope really understand this problem and I think Cisco gives Lancope a lot more scale and resources. Then the integration into things like ISE, TrustSec, and ACI gives you a greater ability to decrease the attack surface.
Cisco has all of the right pieces and the trend to integrating them toward an architecture is very important. It is certainly the right direction. Each piece has to compete on its own and have the integration capabilities, and that is generally what I see.
To learn more about network security monitoring, read the ESG report Network Security Monitoring Trends.
 Written by Christelle Gental
Written by Christelle Gental