Cisco leads the industry with a Unified, Application-centric approach to computing. Building on the architectural foundations, partnerships, and rapid customer adoption of UCS, today Cisco introduces innovations inspired by customer requirements in two key Data Center technology areas:
- Cisco MDS, UCS and Nexus portfolio Innovations: To help customers grow, consolidate, converge and to adapt to changing business needs, Cisco is announcing new additions and innovations to the Cisco MDS, UCS and Nexus portfolio. Please check the blog post by Tony Anthony Cisco Storage Networking Innovations to support high data growth and scale for additional details about these innovations.
- Cisco UCS Innovations: Inspired by customer needs for greater efficiency and lower TCO, Cisco delivers new UCS features and functionalities with 3rd generation Fabric Interconnect, next wave of unified computing management innovations, new acceleration options for Cisco UCS and scalability options for Cisco UCS solutions.
Let’s take a closer look at these latest Cisco UCS innovations and how they can assist to achieve better business outcomes.
New Cisco UCS Fabric Interconnect 6300 Series and Fabric Extender 2304

The Cisco UCS Fabric Interconnect 6300 Series employs the UCS Fabric, VIC and UCS Manager to enable a high-performance, low latency and lossless fabric architecture for high capacity data centers. The Fabric Interconnect 6300 series adds to Cisco’s successful Fabric Interconnect 6200 series to deploy 40Gb, 40G FCoE, and 16Gb FC to further bandwidth capacity and provide for an adaptable data center fabric. The 6300 Series offers 2.6X increase in throughput, 3X lower latency and high-density 40GbE ports that enable an end-to-end 40 Gigabit solution. For additional details please check: http://www.cisco.com/c/en/us/products/servers-unified-computing/ucs-6300-series-fabric-interconnects/index.html
Cisco VIC 1387 dual port 40Gb QSFP mLOM adapter
Cisco also announced the 3rd generation UCS VIC 1387 dual port 40Gb QSFP mLOM adapter.The VIC 1387 is based on 3rd Generation Cisco ASIC technology and is ideally suited for next-generation networks requiring up to 40Gb bandwidth. It supports network overlay technologies such as VXLAN and carries forward support for advanced Cisco features such as VMFEX, Netflow, and usNIC. The VIC 1387 is supported with the C220 M4, C240 M4 and the C3160 Servers.
UCS Management Enhancements: UCS Central 1.4 (1a) Releases and UCS Manager 3.1(1e) Release:
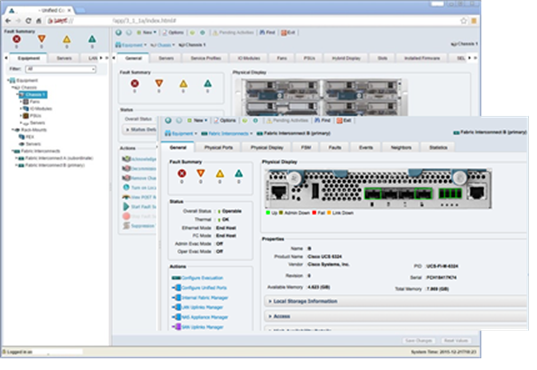
Enhancements to the UCS Management portfolio enable remote operation, automation and policy enforcement across massive multi-site footprints with the UCS Central Software 1.4(1a) Release. The UCS Manager 3.1(1e) Release provides Unified Management for ALL UCS Server Platforms – UCS B-Series, C-Series, M-Series and UCS Mini.
Some of the key UCS Management enhancements include:
- New HTML5 as well as JAVA GUI options
- Unified Release for ALL UCS server platforms – B-Series, C-Series, M-Series, and UCS Mini
- Provisioning and usability Enhancements to UCS Central
- Support mixed UCS domains with M-Series and B/C-Series with support for up to 10,000 servers
Please check Cisco UCS Manager and Cisco UCS Central Software for additional details.
New Acceleration options for Cisco UCS Servers
Cisco announced the availability of the new “Maxwell” generation M6 GPU for Blade Servers and M60 GPU for Rack Servers. Both new GPU technologies enable new VDI use-cases with NVIDIA GRID 2.0 Integration. Cisco and NVIDIA have co-developed the M6 MXM GPU for both Tesla, general purpose Graphics Processing as well as GRID VDI GPU and integrated it with the Cisco B200 M4 Blade Server. This fully-integrated GPU is supported with all CPU SKUs and provides performance on par with the NVIDIA K2 GPU, at less than ½ the power profile!
Here is a complete list of new acceleration options introduced for the Cisco UCS servers:
- NVIDIA M6 GPU Support for B200-M4
- NVIDIA M60 GPU support for C240 M4 and C460 M4
- Support PCIe SSD on M4-Servers
- Support Crypto Card on B200-M4
- Support LSI 9286CV-8e RAID Controller
Enhanced Solutions Scalability with Second UCS Mini Chassis Support
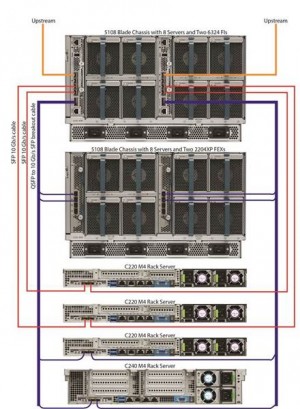
If you need more than eight blades for your small / medium business, remote / branch office, or in your data center for physical isolation, wait no more! You can now have a total of 16 blades and up to six rack servers. Check out these UCS Mini Solutions for integrated infrastructure, business applications, and storage.
New Acceleration Options for UCS M-Series
Part of Cisco’s composable infrastructure, M-Series is designed for scale out applications and dense compute. Four new cartridges have been released. Two each for the M142 and M1414 models featuring the Intel® Xeon ® E3-1200 v4 series processors including Iris Pro graphics integrated GPU. The Iris Pro GPU can accelerate a variety of graphical applications like remote desktops. For additional details please check: http://www.cisco.com/c/en/us/products/servers-unified-computing/ucs-m-series-modular-servers/index.html
Building on the architectural foundations, partnerships, and rapid customer adoption of UCS, Cisco now delivers the next wave of Unified Computing innovations to enhance data center performance and scalability while maintaining operational efficiency. Leverage the latest Cisco UCS innovations to minimize data center complexity and disruption while deploying infrastructure and applications faster than ever before.
Don’t forget to register for the Interactive Webinar on February 11th, 2016 “Cisco UCS Innovations-Adopt the Power of Unification, Innovation and Scalability” where Cisco Data center experts will review new Cisco UCS innovation in detail and you can also hear fa customer testimonial about the latest UCS Innovations.
 Get the Podcast
Get the Podcast Cisco Innovation Centers are where start-ups, accelerators, developers, researchers, ecosystem partners and the venture community come together to create ground-breaking technology and innovative solutions for the future. We have nine of them around the world, and we wanted to share a little insight about what it’s like for a start-up to be part of one. In this guest blog, Jacoby Thwaites, founder of
Cisco Innovation Centers are where start-ups, accelerators, developers, researchers, ecosystem partners and the venture community come together to create ground-breaking technology and innovative solutions for the future. We have nine of them around the world, and we wanted to share a little insight about what it’s like for a start-up to be part of one. In this guest blog, Jacoby Thwaites, founder of