Have you ever dreamed about a network where your users get exactly the experience they need? A world without frustrated people complaining about poorly performing applications or video calls? With the recent introduction of the Cisco Digital Network Architecture (or Cisco DNA, as we like to call it), those days are not as far off as they may have seemed.
The Cisco DNA platform delivers on Cisco’s commitment to innovative, flexible, and secure networks. Along with the announcement of DNA came the first wave of solutions that take advantage of it. And that is just the beginning. There’s much more on the way that can help you realize the benefits of network programmability, analytics, and virtualization.
A perfect example: Our Collaboration engineering team has been working to leverage DNA’s controller-based automation and open APIs to deliver a better collaboration user experience.
A major benefit of DNA’s programmability is that things that were statically defined—configured once and usually left alone—can now become dynamic. This provides capabilities that simply weren’t possible before. We’re leveraging this in Cisco Unified Communications Manager (CUCM) with a new feature called Dynamic QoS.
Before DNA, IT teams deploying desktop and mobile clients like Cisco Jabber had to make a decision:
- Make things very secure by disabling QoS and living with the resulting poor audio and video quality
- Trust and prioritize some or all client traffic, leaving an opening to potential abuse of the QoS policies and the risk of degraded network performance for business-critical apps
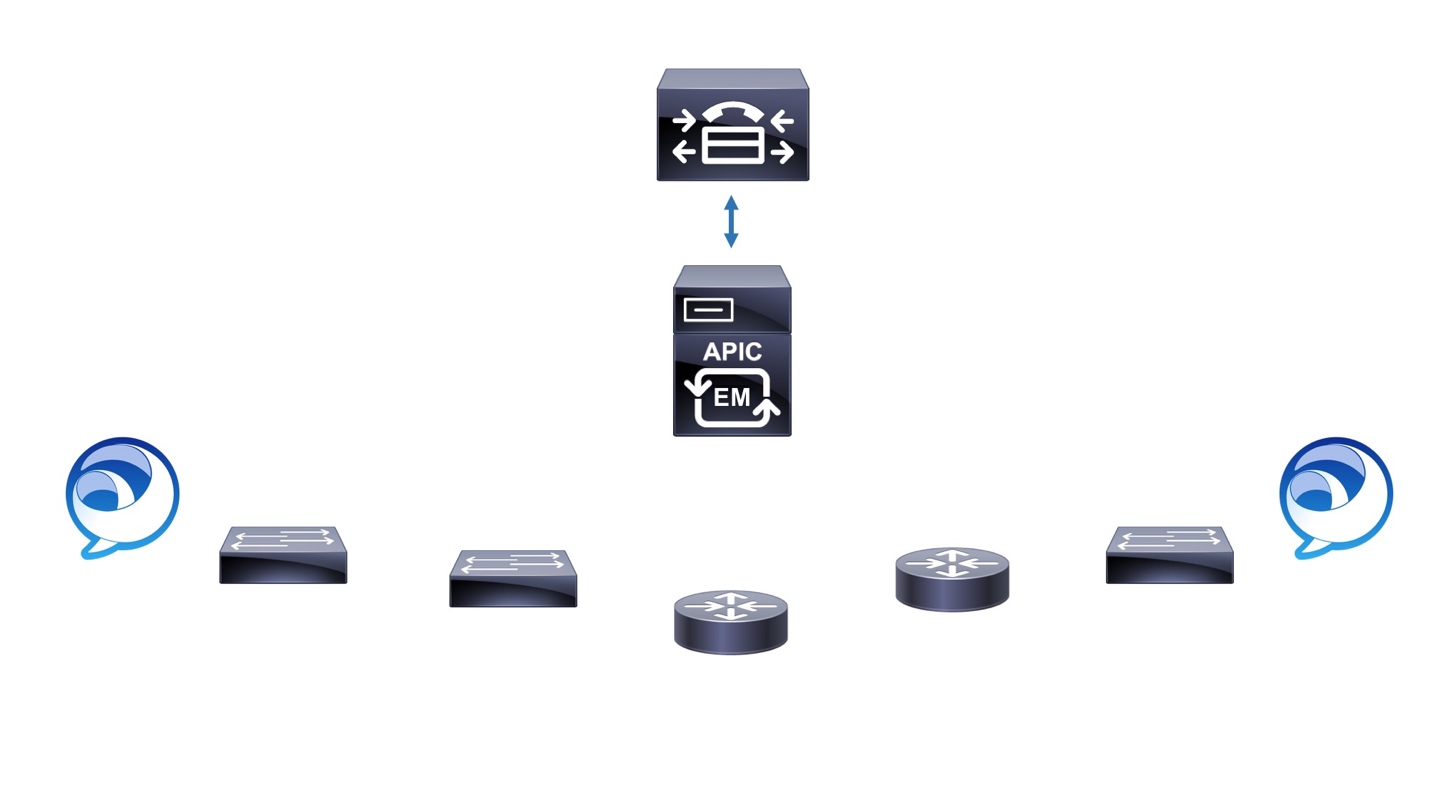
With DNA, CUCM can program the network by means of the APIC-EM controller to dynamically set up QoS for calls at the time they are placed. This is an elegant solution that gives IT and users the best of both worlds:
- The proper QoS marking and treatment policy is applied end-to-end in the network, specifically for the audio and video traffic from the soft client.
- Trust established on the back end, between CUCM and APIC-EM, requires nothing special on the client device. When the call is over, the policy is automatically removed from the network.
You can get a good view of how this works by watching the recent Cisco TechWiseTV on DNA. (Start at 11:00 minutes into the session for the specifics on Dynamic QoS.)
https://www.youtube.com/watch?v=314-NyizsCA
 Troubleshooting problems is another area in which DNA helps Collaboration. It can be extremely tedious to find the root cause of poor video quality across a complex network. It’s a bit like looking for needle in a haystack:
Troubleshooting problems is another area in which DNA helps Collaboration. It can be extremely tedious to find the root cause of poor video quality across a complex network. It’s a bit like looking for needle in a haystack:
- Is there a misconfigured switch port?
- An overloaded link?
- An SP not meeting the SLA?
Finding the device or link at the source of the problem can take the majority of the time spent resolving it. Prime Collaboration Assurance integrates with a DNA network to provide a visualization of the layer 2 and layer 3 network devices along the media path and speed up the identification of the root cause.
These are just two examples of the power of DNA. We’re already working on several other areas of integration, enabling Cisco Collaboration to leverage DNA. Creating these integrations is relatively easy and sustainable using DNA’s open, model-driven RESTful APIs. In fact, these same APIs simplify the ability of IT organizations to create their own integrations for their specific business needs.
Cisco DNA can give you the control to support your organization’s digital ambitions — faster, easier, and more securely than ever before. Here’s to the new exciting chapter in software-driven networking.
 With this context in mind, and wearing my dual hats as both the Vice President, Australia New Zealand for Cisco and President of
With this context in mind, and wearing my dual hats as both the Vice President, Australia New Zealand for Cisco and President of 

![pratap_picture[1]](https://blogs.cisco.com/gcs/ciscoblogs/1/pratap_picture1-150x150.png) Guest Blogger: Pratap Pereira, Distinguished Engineer, Enterprise Networking Group.
Guest Blogger: Pratap Pereira, Distinguished Engineer, Enterprise Networking Group. In the internal development environment, I am proud to say that for the entire routing, switching and wireless control plane to data plane interface we have completely converted to a formal model-driven software interface. This is an internal model, which gives us an independent foundation on which to rapidly develop functionality with zero impedance mismatch or translation layers. The distinction between internal interfaces and external interfaces is an important one. The internal models are the essence of the core competency of Cisco as a software organization. It has to progress at the pace of internal innovation and must withstand the test of time. Setting the expectation for a large development organization to have a simple, single mental model for how software is developed paves the way for excellence. Equally, introducing capricious wanton changes that chase after every shiny new object would not do well when setting expectations with a large group of engineers. The ability to change our very foundation is a deeply deliberative task, which we successfully accomplished with evolved IOS-XE. The expectation is that evolved IOS-XE will be our stable foundation for a period of time until the next substantial software stack upgrade. We will speak more, in subsequent blog posts, about how the complete software stack at Cisco lines up.
In the internal development environment, I am proud to say that for the entire routing, switching and wireless control plane to data plane interface we have completely converted to a formal model-driven software interface. This is an internal model, which gives us an independent foundation on which to rapidly develop functionality with zero impedance mismatch or translation layers. The distinction between internal interfaces and external interfaces is an important one. The internal models are the essence of the core competency of Cisco as a software organization. It has to progress at the pace of internal innovation and must withstand the test of time. Setting the expectation for a large development organization to have a simple, single mental model for how software is developed paves the way for excellence. Equally, introducing capricious wanton changes that chase after every shiny new object would not do well when setting expectations with a large group of engineers. The ability to change our very foundation is a deeply deliberative task, which we successfully accomplished with evolved IOS-XE. The expectation is that evolved IOS-XE will be our stable foundation for a period of time until the next substantial software stack upgrade. We will speak more, in subsequent blog posts, about how the complete software stack at Cisco lines up.