Part 1: What does it take to win in an OTT world?
In this blog trilogy, I will try to shed some light on one of the more intriguing topics in the video industry– OTT video. I will discuss the reality of OTT video, the service provider’s perception of it, the future of the paid video industry and what service providers should do today in order to win in an OTT world.
I just returned from beautiful Budapest. But alas, I was not touring. Instead, I spent a couple of days with a group of smart people from the pay TV industry; service providers, media producers, analysts and technology vendors. We were gathered together to discuss the future of TV.
Over The Top video, or in short OTT, was top of mind in the discussions.
Let’s remind ourselves of what OTT video is.
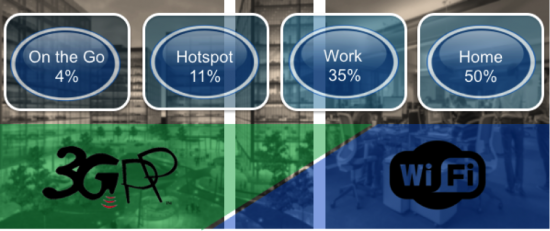
It’s the delivery of video over an unmanaged network, meaning the Internet, as opposed to managed networks, like pay TV cable.

Over 80% of IP traffic today is video. Practically speaking, this is OTT video. It comprises paid VOD libraries, like the Netflix’s of this world, as well as free video of all kinds, like YouTube. Very little of it is in fact linear video (like TV channels).
What does this mean for the pay TV industry? Is OTT even a concern?
Well, given the fact that OTT dominated most of the discussions, I’d say it’s a big concern.
Attendees were asking:
- “Is it an opportunity or a threat for our business?”
- “What does it mean for us?”
- “How will the future with OTT look?”
It was interesting to note that most of the viewpoints expressed at this conference discussed the short and mid-term implications, rather than the long term impact. That’s because most attendees felt that OTT does not present a risk for the pay TV industry. Here are some of the reasons that they gave:
- “It’s not targeted to our subscribers, nor localized to our market. Our subscribers wish to see the content they like, in their language, and only local SPs can provide it”
- “Our subscribers care first and foremost about linear channels and OTT doesn’t provide them”
- “Subscribers are using OTT as a supplement to SP services, not instead of them”
- “There is no real commercial benefit in moving to OTT… our subscribers will not save much, if at all”
The majority of attendees nonetheless felt that SPs should integrate OTT services into their guide. After all, subscribers do want them. And so it’s better to ensure that they get all they need directly from the service provider, rather than sending them to the Internet.
It was also clear that service providers should offer OTT services, mainly to serve mobile devices, but also home CE devices.
But let’s be clear.
There was no commercial justification or revenue opportunity behind these sentiments. They were about satisfying subscriber demand in order to maintain loyalty and avoid churn. My impression was that service providers were treating OTT more as a necessary evil, the unwanted guest. It seems that they don’t see OTT video as an immediate threat. But they do feel it needs to be addressed.
Are they being too ambivalent with respect to OTT?
I will discuss that in my next blog by examining what we can in fact learn today from OTT video providers and where their business is going.
Stay tuned for my next post, but in the meantime check out this brand new eBook: Transform your video services with a cloud platform