The market for cloud services is growing like wildfire. But to capture it, cloud service providers need speed and flexibility. In this marketplace, making customers choose between the same old limited infrastructure-as-a-service (IaaS) options, or waiting weeks for custom solutions, is no choice at all. Now, leading service providers like QSS can offer a better option: fast, flexible, custom hybrid cloud solutions.
As the leading cloud provider in Bosnia and Herzegovina, QSS leaders know that staying on top means giving customers better business solutions faster. The company was already known for superior custom on-premises and cloud IT solutions. To grow their business and keep an edge on the competition, they wanted to be able to provide a wider range of hybrid cloud services. They wanted to deliver them with total security and flexibility. And they wanted to be able to monetize them sooner.
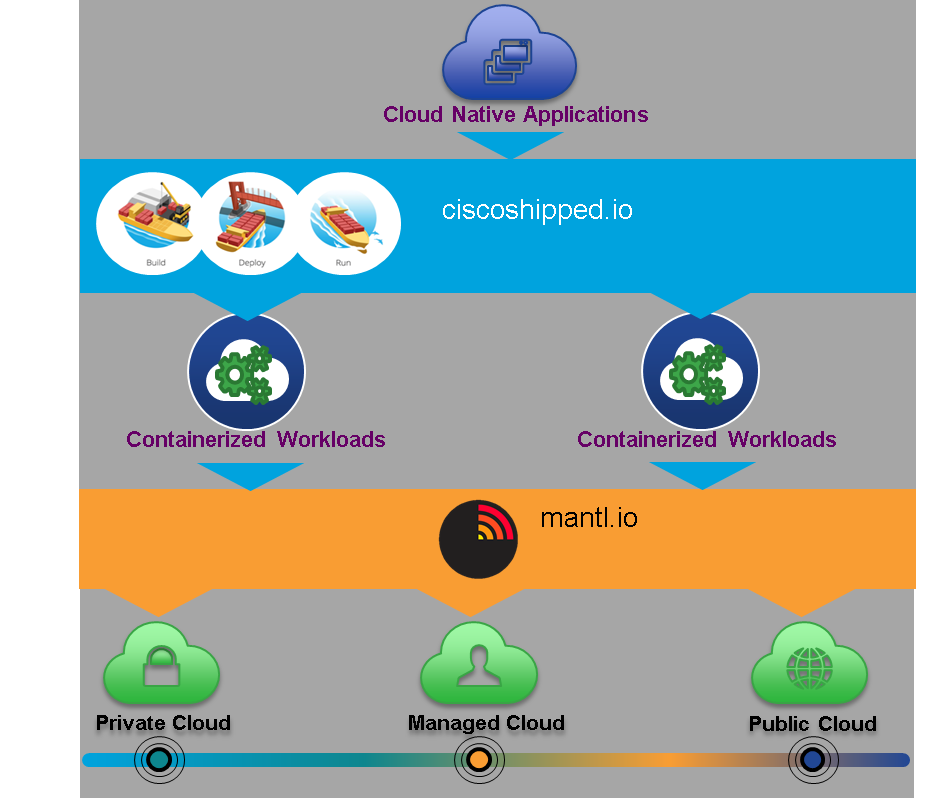
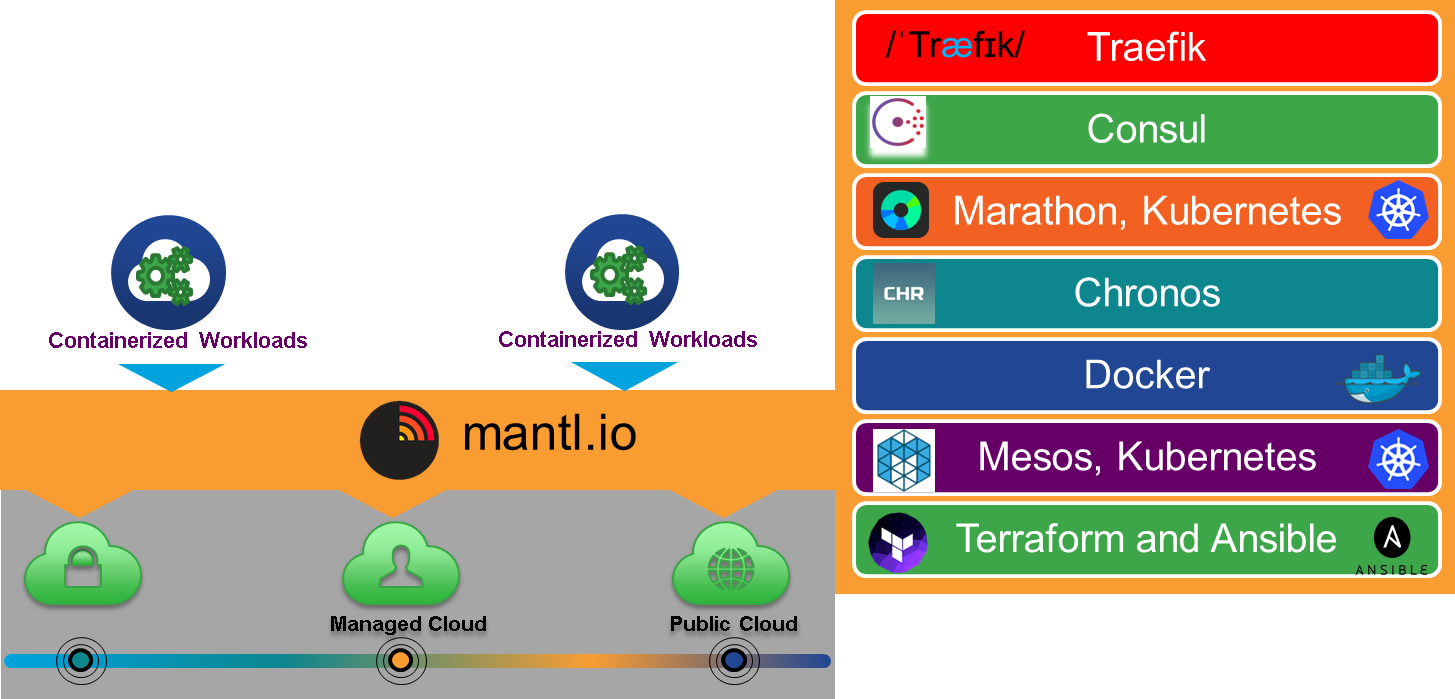
QSS needed a hybrid cloud platform that would let them quickly acquire new cloud business models and revenue streams wherever new opportunities arose. They wanted to build on a proven architecture with strong security. And they wanted the flexibility to continually integrate new cloud services in an automated fashion, with fast, low-risk migration. They turned to the Cisco Cloud Architecture for Microsoft Cloud Platform.
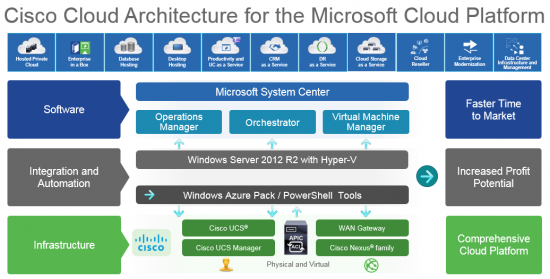
Cisco Cloud Architecture for Microsoft Cloud Platform
QSS launched one of the first Cisco Cloud Architecture for Microsoft Cloud Platform deployments in Europe. The solution uses Cisco Application Centric Infrastructure (ACI) to fuse QSS’ Cisco cloud data center with Windows Azure Pack. With joint design and engineering from Cisco and Microsoft, it all works seamlessly together.
QSS can create new customized cloud solutions for their customers in minutes, and deliver them with little manual intervention. They can offer a broad range of IaaS solutions to customers in financial services, government, and IT. And they can swap easily between private and public cloud domains as needed. Cisco ACI automates almost everything, eliminating the traditional tradeoffs between speed and customizability. 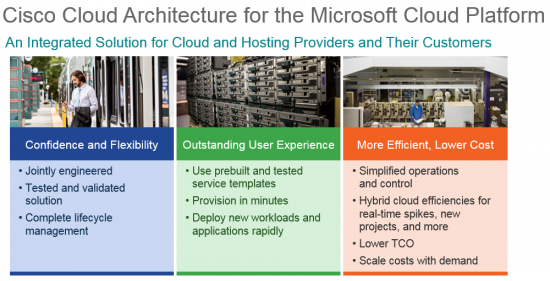
Hybrid Cloud in Action
Today, QSS is leading the race for next-generation cloud services in Eastern Europe. They can create and monetize new hybrid cloud offerings much faster. And they’re now expanding into new markets like home security and remote metering. QSS has also built a flourishing reseller channel, drawing on training, sales enablement, and demand-generation resources from Cisco and Microsoft. And with Cisco ACI, they can continually refresh their hybrid cloud platform to address new opportunities—simply, and with less risk.
Today, QSS is realizing:
- 5x faster time to market
- Setup times reduced from 10 days to 1
- Customer satisfaction scores that exceed targets
- Infrastructure that’s updated every two weeks to drive continuous innovation
As a result of the business growth driven by new hybrid cloud capabilities, QSS leaders expect to see a return on their investment within three years.
“Our customers expect us to simplify technology, so they can focus on supporting their business goals,” says Isan Selimović, Chief Executive Officer, QSS. “Now, our business runs lean in operation and agile in delivery. Everything’s kept secure. And it’s much easier and cost effective to customize solutions.”
View the QSS Success Story


Find Out More
And to find out what Cisco Cloud Architecture for Microsoft Cloud Platform can do for your business, visit cisco.com/go/ccamcp.
If you’re joining us in Las Vegas on July 10-14th, visit the Cisco booth which will feature a demo of the Cisco Cloud Architecture for the Microsoft Cloud Platform.

 customers, IT experts, partners, media specialists, industry analysts and others interested in learning more about Cisco and our offerings. It serves as Cisco’s state of the union to connect Cisco customers and our partner eco-system with an opportunity to showcase how Cisco is changing the way we live, work, learn and play. This year’s event is expected to draw over 29,000 attendees and will bring together Cisco enthusiasts across all business and public sector segments including government, education, healthcare, public safety, and transportation.
customers, IT experts, partners, media specialists, industry analysts and others interested in learning more about Cisco and our offerings. It serves as Cisco’s state of the union to connect Cisco customers and our partner eco-system with an opportunity to showcase how Cisco is changing the way we live, work, learn and play. This year’s event is expected to draw over 29,000 attendees and will bring together Cisco enthusiasts across all business and public sector segments including government, education, healthcare, public safety, and transportation.