![]()
With Interop less than three weeks away, we are excited to learn that Cisco APIC, the SDN controller for our Application Centric Infrastructure (ACI) fabric, has been selected as Best of Interop 2015 Finalists in Software Defined Networking (SDN) category. As you may recall, when we announced ACI back in Nov 2013, we mentioned that APIC would be the software controller for the application-centric policy model, and would be available in Q3, CY 2014. In a short span of less than a year, APIC has gained broad industry adoption with more than 300 Customers either deploying or in production already.
Interop Vegas, is a great venue to unveil more aspects of the ACI fabric, the policy model, and key APIC features. If you aren’t going to be in Las Vegas the last week of April, now may be the time to start making plans as we gear up for some exciting ACI news and events, and hopefully bringing home this Best of Interop award.
But wait, there’s more…
If you are not familiar with ACI or APIC yet, let me take the opportunity to tell you about APIC and why I think it is a finalist for the Best of Interop.
The Cisco APIC is the unified point of automation and management for the ACI fabric and health monitoring. The Cisco APIC is built with open APIs and an open application-centric policy model designed to simplify the provisioning, monitoring, and management of applications across the data center. Cisco’s Application Centric Infrastructure (ACI) is a fabric architecture with centralized automation and policy-driven application profiles designed to make the infrastructure highly responsive to the needs of applications, while significantly simplifying the data center and cloud operational model.
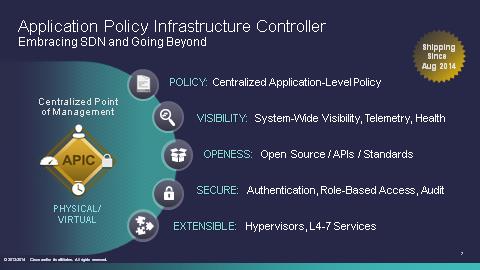
The Cisco APIC is built on the SDN principles of an extensible/programmable centralized controller, standardized north-bound API’s, a protocol for communicating with and orchestrating data center devices and network nodes, and features and agents within the network infrastructure to support the controller’s policy model and respond appropriately.
The Cisco APIC uses an application-centric policy model rather than network-centric SDN policies that do not adequately reflect business requirements. Cisco ACI is an open ecosystem of management, services, and security partners that incorporate best-of-breed solutions across physical and virtual infrastructures. Customers have a choice of flexible workflow automation and orchestration solutions on top of APIC and the ACI fabric, including OpenStack, VMware cloud automation solutions, Microsoft System Center, Cisco UCS Director, and more, rather than being locked into a specific automation model.
The APIC software is delivered on turn-key UCS C-Series server appliances, so the user out-of-box experience is simple.
Apparently these stellar traits weren’t lost on the Best of Interop judges as it made it to Finalist status. We sincerely hope this bad boy brings home the prize too – stay tuned for more excitement to come.
Related Links
 #CiscoChampion Radio is a podcast series by
#CiscoChampion Radio is a podcast series by  Frank Cicalese is a Technical Solutions Architect with Cisco’s Data Center Architecture Team helping customers globally with their Microsoft solutions on Cisco UCS. Frank also worked at Microsoft for over 10 years in several positions that required deep technical knowledge such as Services Consultant, Platform Architect, Database Technology Specialist, Virtualization Technology Specialist and Datacenter Technology Specialist. Frank has in-depth technical knowledge and proficiency with database design, optimization, replication and clustering and has extensive virtualization, identity and access management and application development skills. He is also a writer member of the American Society of Composers, Authors and Publishers with published musical works that have aired on well-known cable and news networks.
Frank Cicalese is a Technical Solutions Architect with Cisco’s Data Center Architecture Team helping customers globally with their Microsoft solutions on Cisco UCS. Frank also worked at Microsoft for over 10 years in several positions that required deep technical knowledge such as Services Consultant, Platform Architect, Database Technology Specialist, Virtualization Technology Specialist and Datacenter Technology Specialist. Frank has in-depth technical knowledge and proficiency with database design, optimization, replication and clustering and has extensive virtualization, identity and access management and application development skills. He is also a writer member of the American Society of Composers, Authors and Publishers with published musical works that have aired on well-known cable and news networks.