Why all the buzz around pursuing group-based policy management to achieve zero trust?
Adopting zero-trust initiatives and best practices is all the rage. And rightly so. With network environments continuously growing in terms of both size and complexity, abolishing the notion of trust outright is a great way to prevent breaches, contain unwelcome lateral movement, and protect the ever-growing volume of sensitive data that traverses modern enterprise environments. Simply put, applying “never trust; always verify” to anyone and any device attempting to access an enterprise network is a no-brainer nowadays. So much so that every organization must be doing it, right?
Not so fast. The caveat? Adopting a genuinely ironclad zero-trust security model is predicated on successfully implementing effective group-based network segmentation policies, which can be REALLY hard in today’s exceedingly vast and complicated network environments.
How so?
Policy adoption can be challenging for multiple reasons. Some practitioners don’t know how to create the right policies, for starters, simply because they lack an awareness of everything that’s running in their environment. Second, even those who have effectively mapped out their networks often struggle to understand enough about what all their devices are doing to take any action, and find themselves asking questions like who’s talking to who? How are they communicating with one another? Why are they speaking? Are the ad hoc policies that are currently in place actually working as intended?
Ok, although that does sound complicated, my security team will find a way to just get the job done, right?
Well, not exactly. As if that weren’t enough, to make matters worse, this lack of visibility into what devices are doing can result in practitioners feeling hesitant to create and implement new policies that could have unintended consequences. For example, a user could unintentionally allow unauthorized groups to access sensitive information or even bring down an entire manufacturing line simply because they applied a misconfigured policy update that restricted operationally critical devices from communicating.
Yikes!
Yikes indeed. This complexity can increase security risks to your organization through inaction, as teams end up “stuck” and unable to create and implement the right policies for their environment. All these factors combined ultimately add up to delays in deploying and benefiting from a more secure group-based policy solution.
Security professionals need comprehensive visibility into all devices on their network to know what groups are speaking with one another, how they’re communicating, and why they’re doing so.
Confidently embrace network segmentation and achieve zero-trust with TrustSec Analytics
Deploying Cisco Secure Network Analytics (formerly Stealthwatch) and Cisco Identity Services Engine (ISE) allows practitioners to move beyond these roadblocks via the new TrustSec Analytics Reports that enable users to visualize all group communications across enterprise networks.
TrustSec Analytics reports offer new ways to visualize group communications
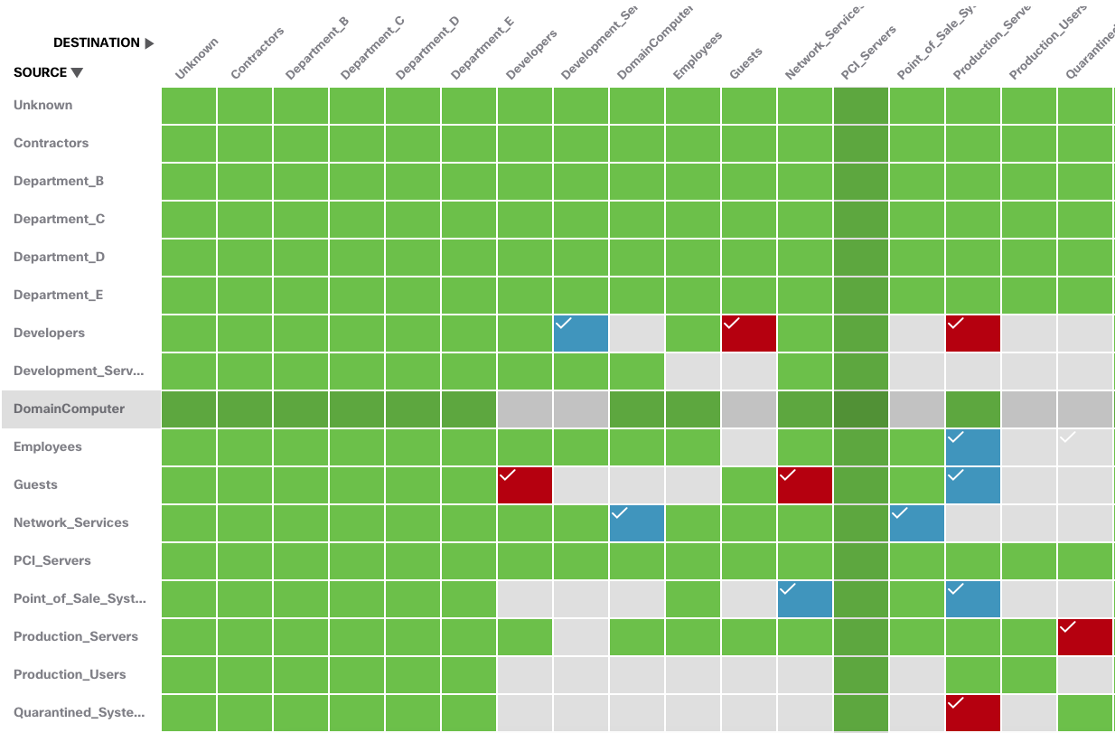
TrustSec Analytics reports lower the entry point to adopting group-based policy management programs to build network segmentation. Now any Secure Network Analytics user can effortlessly visualize, analyze, and drill down into any inter-group communication, validate the intent of policies, adopt the right policies, and adapt them to their environment’s needs.
Streamline policy violation investigations with TrustSec Policy Analytics reports
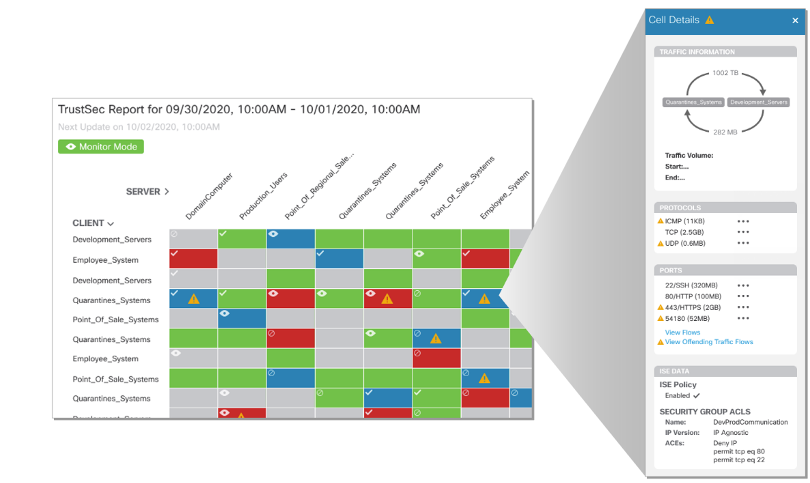
Users can also generate TrustSec Policy Analytics reports to assess whether policies are being violated. By clicking on any cell in the report, users can gain insights into the volume of data being sent between any two groups, how that data is being distributed, the protocols being used, what ports they are operating on, and more.
Additionally, when it comes to the typically lengthy processes associated with determining the root cause of a policy violation, the capabilities offered by the TrustSec Policy Analytics report quite literally enable users to find the proverbial “offending-flow needles” in their vast “network haystacks”. Rather than performing hours of cumbersome tasks such as conducting manual searches and cross-references across different datasets, users can get granular by drilling down into policy violations to view all associated IPs and related flows, associated endpoints, ISE-registered usernames, and events with timestamps on a single pane. TrustSec Policy Analytics reports effectively enable users to streamline their root cause analysis efforts and expedite their ability to diagnose why a policy violation occurred.
Bottom line: Secure Network Analytics’ TrustSec Analytics reports lower the entry point to achieving zero-trust via network segmentation. To summarize, users can:
- Observe more intergroup communications effortlessly by visualizing what groups within their environment are communicating with one another, using TrustSec Analytics reports that map group communications between up to 250 security group tags (SGTs).
- Validate the efficacy of policies by examining near real-time network telemetry flows between groups to monitor whether trusted ISE policies are being observed as intended and adapt them when necessary.
- Streamline investigations of policy violation by generating TrustSec Policy Analytics reports, which provide granular insights into all relevant flows between SGTs and associated IPs to enable quick and effective responses to policy violations.
- Analyze changes in traffic patterns with TrustSec reporting data that is retained for 30 days across all SGTs to better understand how policy changes have impacted network telemetry flows over time.
And by facilitating policy adoption efforts, TrustSec Analytics reports essentially allow users to immediately achieve the benefits of zero trust and intent-based networking via their existing Cisco architecture while also positioning them for future adoption of software-defined access.
Stay tuned for our next two upcoming TrustSec Policy Analytics blog posts in which Matt Robertson will dive deeper into these new reports and how they can be used to develop, monitor, and verify security policies.
Don’t have Secure Network Analytics? Learn more or try the solution out for yourself today with a free visibility assessment.





