“I so look forward to the next firewall hardware upgrade cycle!”
– No One Ever
Always Give More
If I learned one thing from my firewall customers over the many years, it would be that they like to upgrade their hardware appliances as much as an average consumer likes to shop for a new car. No amount of flashy vendor marketing materials with the obligatory “industry-first” promises peppered all over can make up for this unglamorous exercise. No one enjoys forking out gobs of money and spending sleepless implementation hours every few years in exchange for a shiny new box with largely the same architecture as the old one, save for maybe a slightly faster CPU. That said, some hardware upgrades are certainly worth it.
It’s been a minute since our last major hardware refresh, largely due to the future-proof architecture of all Secure Firewall appliances. Something bigger and better has been in the works for a while, but my personal preference has always been to optimize the software first and then purpose-build great hardware for it. Instead of asking you to go through the fun exercise of forklifting hardware more often, we released Secure Firewall Threat Defense 7.0 last year to do something magical. It substantially increased (and doubled in some cases!) both threat protection and VPN performance across all supported firewall appliances – including ASA5508-X from about 7 years ago – through a simple software upgrade. If I want to be an industry-first (if not industry-only) at something, delivering long-lasting customer value like that is definitely it.
Bundle of Power
After delivering that software performance goodness into our customers’ hands, it was time to follow on with a fundamentally new hardware architecture. Something built for resilience and scale while maintaining simplicity. A beast that would stand up to the prevailing trends of pervasive traffic encryption, assume it as a performance baseline, and crush those numbers across the industry. Last but not least, a solution that is incredibly cost-effective against the competition. This is how the new mid-range Secure Firewall 3100 Series was born.
A lot of punch is packed into this industry-leading 1 rack-unit form factor. Building on the years of architectural perfection, it continues to employ an intelligent internal switch fabric for non-blocking external network interface connectivity as well as flexible load-balancing and prioritization logic. It features an enterprise-grade x86-based CPU engine with our extensible Threat Defense software that excels at several critical protection and visibility capabilities. One is the proven-and-true deep packet inspection functionality with Snort 3, backed by the threat intelligence and sheer brainpower of Cisco Talos. It is complemented by inference-based application identification and malware classification with our recently released and completely in-house developed Encrypted Visibility Engine (EVE). All the software components and customer data are hosted on self-encrypting and optionally redundant Solid-State Drives (SSD) for that extra peace of mind.
We are borrowing a page from our higher-end appliances by incorporating the industry-first Multi-Instance capability which provides full resource separation between individually configured firewall tenants. Same goes for the Clustering feature (another industry-first back in its day!) with a fully distributed forwarding plane across up to 8 individual 3100 Series appliances that act as a single logical unit. All this goodness is nicely wrapped into the new unified Firewall Management Center experience, eliminating one complexity after another. Then there is the pricing that should definitely make your budget approvers smile. And just when you thought that we were all out of tricks, there’s just one more thing.
It’s All About Encryption
The big deal about the new Secure Firewall 3100 Series architecture is the emphasis on processing encrypted traffic. The traditional industry approach has been to deploy a look-aside crypto accelerator which works in tandem with the x86 CPU to process IPsec and Transport Layer Security (TLS) traffic for both VPN and transit inspection purposes. This approach expectedly results in a tremendous performance degradation, chiefly due to that look-aside nature that requires multiple traversals of the shared system bus for each encrypted or decrypted packet. Adding insult to injury, most industry implementations also fail to accelerate TLS session establishment in the hardware; we had specifically addressed this problem years ago and proudly published Secure Firewall threat protection throughput numbers with TLS decryption in the publicly available data sheets – can I get another industry-first here?
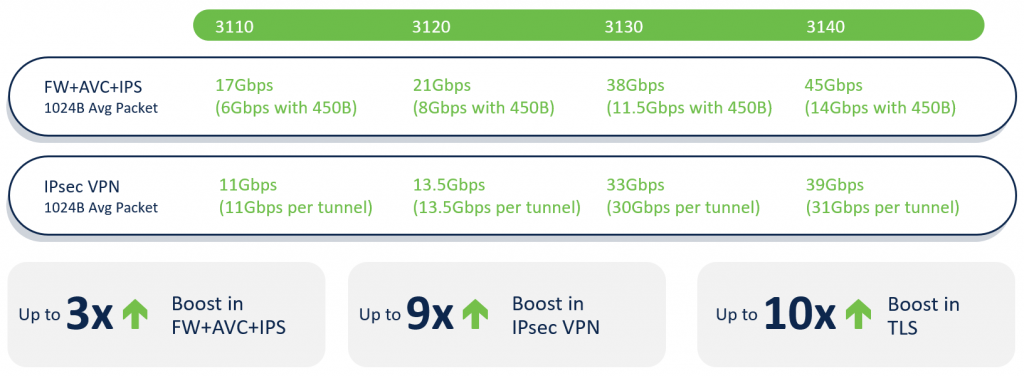
The key difference with the Secure Firewall 3100 Series appliances is in the brand-new custom-built Field Programmable Gate Array (FPGA) component in between the internal switch fabric and the x86 CPU complex. Not only does it implement a next-generation (and a patented industry-first!) Flow Offload engine for both lightning-fast single-flow throughput and high-performance-computing grade latency, but it also provides yet another industry-first in-path crypto acceleration capability across both IPsec and Datagram TLS (DTLS) VPN connections. Once programmed by the threat protection software, this intermediate component can decrypt and encrypt such flows in hardware without having to rely on the main system bus or consuming precious x86 CPU cycles. The raw numbers below are impressive as much as their comparison to the previous-generation Secure Firewall 2100 family, but the single-tunnel throughput with a bi-directional pair of IPsec Security Associations (SA) is mind-blowing – something truly industry-leading for any firewall appliance.
Fun Times Ahead
From fully distributed stateful scalability to isolated multi-tenancy to mind-blowing threat protection throughput and crypto acceleration performance, Secure Firewall 3100 does not disappoint with numerous (and all true!) industry-first claims. Building upon years of architectural perfection, it is a threat protection package that is priced right to convince almost anyone to bite the bullet and get that long-coming hardware upgrade out of the way. Whether you’re a new Secure Firewall customer or a seasoned Firepower aficionado, Cisco has got your back with our unstoppable software innovation for years to come – maximizing the life of your previous hardware investment and keeping your business protected all at once.
For more information on the Secure Firewall 3100 Series, click here.
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels






Cisco all the best
I am virgilio da Cruz froom Indonesia.
Company. PT. Timor Lintas Nusantara (ISP )
Hi Andrew,
Can you please detail a little bit more about the multi-instance capability on Firepower 3100?
According to the quick start guide for this platform, it doesn’t appear to run FXOS Firepower Chassis Manager:
https://www.cisco.com/c/en/us/td/docs/security/secure-firewall/getting-started/3100/secure-firewall-3100-gsg/fmc.html#task_jcn_1n5_33b
“The firewall runs an underlying operating system called the Firepower eXtensible Operating System (FXOS). The firewall does not support the FXOS Firepower Chassis Manager”
Also, I don’t see anywhere any details regarding how many cores does each model have.
BR,
Octavian
Hi Octavian,
That’s a great callout! As a part of unifying the platform experience, we are transitioning both chassis and multi-instance management directly into Firewall Management Center. This capability is not yet released, so stay tuned for future updates.
Andrew
Better than FirePower?
Given the very sub-standard single tunnel/SA IPSec throughput on the Firepower 2100/4100 platform, this was a necessary HW upgrade to compete with Palo Alto and Fortinet who already have decent single tunnel/SA IPSec throughput. In my organization, we had to move DR replication traffic over IPSec off a Firepower 4110 to Palo Alto. Firepower 4110 was just too slow as it tops out at about ~900 Mbps for a single IPSec tunnel.
Hi,
Firepower 4110 is an older model, and something like Firepower 4112 would already use a more modern crypto acceleration components to give you a higher single-SA throughput. There are some implementations which achieve high single-tunnel throughput at the expense of sequence checks and packet injection protection; it all works well until you start seeing legitimate out-of-order packets or malicious actors who try to disrupt your IPsec connectivity. The good news with the 3100 is that you don’t have to compromise on either the performance or stateful protection capabilities.
Andrew
Does 4112 and other new 4100 series have significantly higher single SA throughput? Isn’t the architecture the same, ie an SA can only be processed by a single core? We need 5-6 Gbps of single SA throughput which Palo Alto 3200/5200 series delivers no problem.
Hi,
Firepower 4112 and other 41×5 models have newer hardware acceleration components with faster cores, so single-SA throughput will be higher — albeit much less than what is possible with Secure Firewall 3100 and its new inline crypto design. Crypto accelerator cores aggregate differently, and the x86 side can easily carry 8Gbps of TCP in a single flow on a Firepower 4100 — just not over IPsec. This aspect of any security platform is non-negotiable if packet sequencing is important.
In both our own and customer testing, I haven’t seen a lot of security platforms carry 5-6Gbps in a single SA outside of some carrier-targeted appliances which bypass a lot of the sequence and state checks to parallelize packet processing. The vast majority of mid-range firewalls (including some third-party offerings that you mention above) do not achieve 5-6Gbps of IPsec VPN throughput even across the entire system based on their data sheets.
Andrew
Hope soon I will have a chance to test it.
@Andrew Ossipov does FTD (4100/9100) application support a mix of FTD and ASA instances?