Why Endpoint Security Matters in Protecting Remote Workers – Part 1
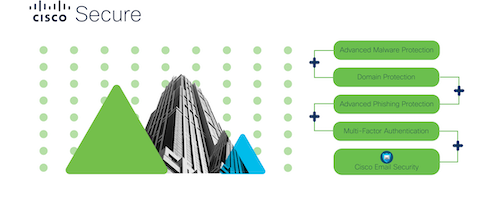
Enabling your workforce to work securely on any endpoint, anywhere, is now more important than ever. See our customer’s thoughts on the value that AMP for Endpoints brings to their business.