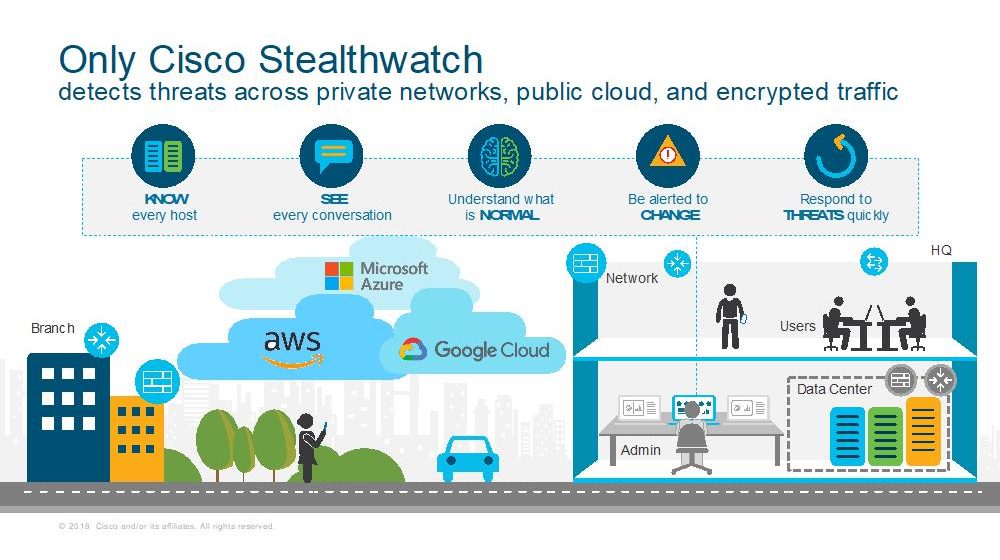
Cisco Stealthwatch becomes the only security analytics product to detect
threats across private networks, public clouds, and encrypted traffic.
You have a bigger, more open, and diverse network than ever before. Whether you want to go all-in on cloud, spread your infrastructure across multiple public clouds, embrace containers and Kubernetes, leverage serverless architectures, or double down on on-premise, Cisco Stealthwatch has you covered! We’ve expanded the capabilities of our Stealthwatch platform to become the first security analytics product to detect threats in unencrypted and encrypted traffic across private networks and public multi-cloud environments.
It’s a win for network architects, for DevOps, and security operations alike. The increasingly dynamic nature of the today’s modern architecture put cybersecurity professionals in a difficult position. Detecting threats across network traffic becomes exponentially more challenging as the infrastructure expands. And is it ever? Spreading across on-premise environments and infrastructure hosted by multiple public cloud providers. Compounding the problem even still is the fact that network traffic is increasingly becoming encrypted. With Stealthwatch, security operations get a common platform to detect threats uniformly across any environment, freeing network architects to design a modern architecture that best meet the needs of the business, freeing DevOps to spin up as many blobs, clusters or functions they need to capture market opportunities faster without putting your organization at risk.
Stealthwatch provides a consistent experience for detecting threats across private networks and multiple-public clouds such as Microsoft Azure, Amazon Web Services, and Google Public Cloud. Stealthwatch closely monitors the activity of every device on the network and is able to create a baseline of normal behavior. Stealthwatch automatically normalizes traffic events gathered natively from your network telemetry and natively from flow logs generated by your cloud infrastructure, presents with you a single view of the threats across your entire environment.
Today, we also announced Stealthwatch as the first to extend visibility, threat detection, and compliance verification to Microsoft Azure without agents or additional sensor deployments within your cloud environment. In fact, only Stealthwatch helps protect your Amazon Web Services, Microsoft Azure, and Google Cloud Platform environments natively without the use of agents. This increases your time to value, as you are able to deploy the product, and begin monitoring for threats within 10 minutes!
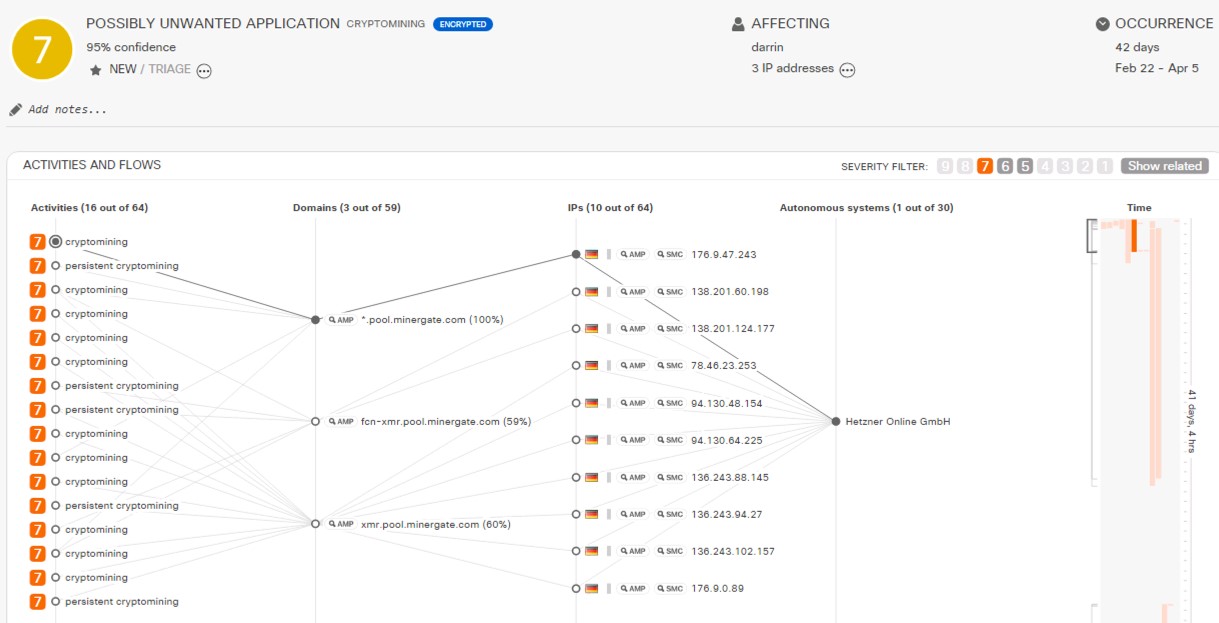
We know there’s nothing worse for a security analyst than a flood of meaningless alerts. They’re time-consuming to wade through to find the ones you need to investigate and take action on. That’s why Stealthwatch surfaces only high-fidelity alarms, prioritized by threat severity, so you get to the threats that are most-pressing faster. Delivering alerts that matter to you is so important to us, we let you rate each one.
To date, 95 percent of Stealthwatch Cloud alerts are rated “helpful” by customers. In other words, when Stealthwatch asks for your attention, there is a good chance you will be glad you investigated it.
We use predictive security analytics underpinned by behavioral modeling, machine learning technologies (yes, we said it…and we back it up too), and global threat intelligence to detect malware even in encrypted traffic without decryption. We apply nearly 100 different security behavioral modeling heuristics that look at various types of traffic behavior, such as scanning, beaconing hosts, brute force logins, suspect data hoarding, suspect data loss. Stealthwatch also applies machine learning, both supervised and unsupervised, to discover the full spectrum of bad communications. It also integrates with a multistage machine learning analytics engine, that correlates threat behaviors seen locally within your organization with those seen globally. A global threat intelligence feed powered by the Cisco Talos™ intelligence platform provides an additional layer of protection against botnets and other sophisticated attacks. With Talos, the bad guys have nowhere to hide. Stealthwatch employs this to automatically detect early indicators of compromise such as insider threat activity, malware, malicious crytomining, and multi-staged attacks. Stealthwatch also identifies policy violations, misconfigured cloud assets, and user error and misuse.
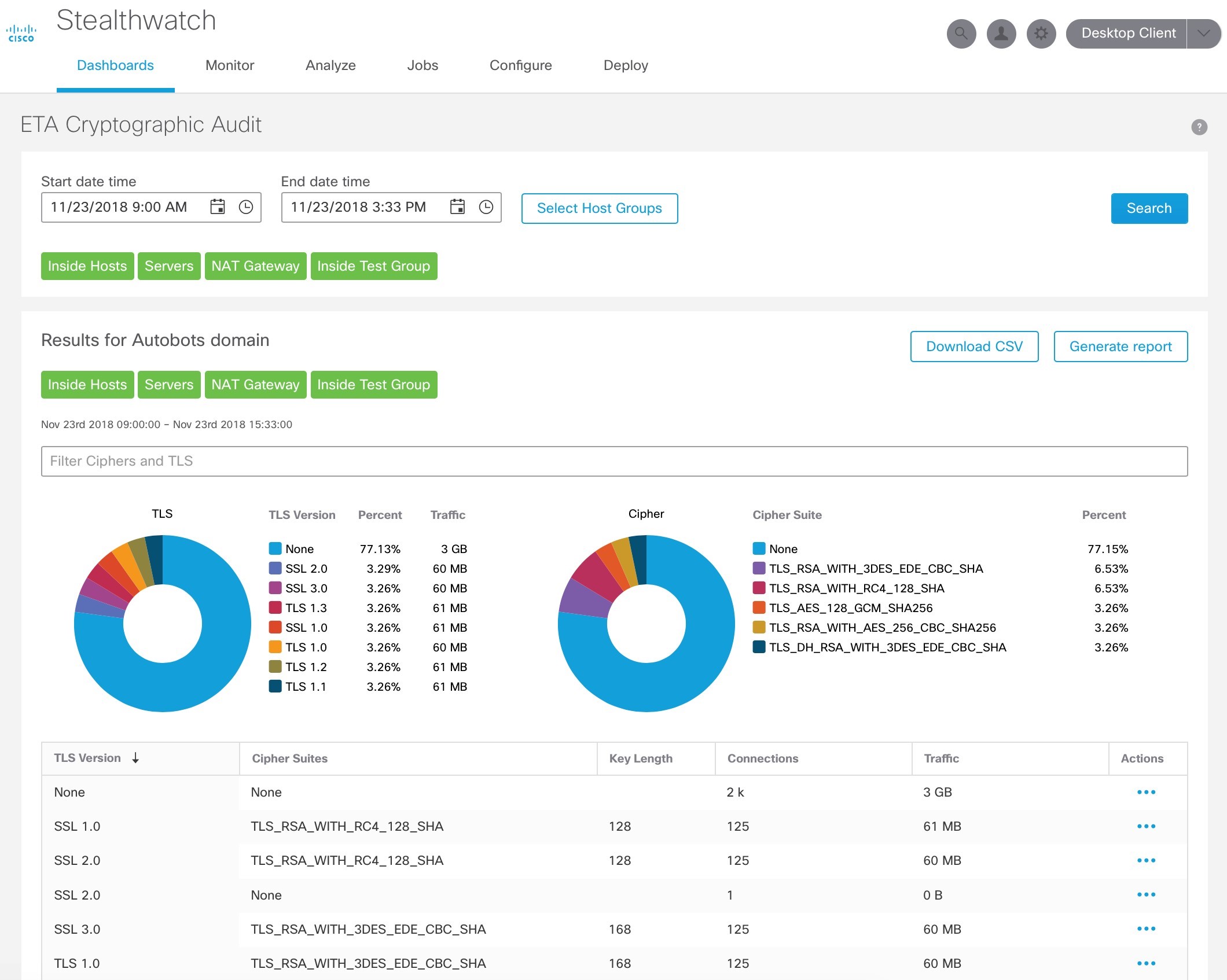
The rapid rise of encrypted traffic is changing the threat landscape. While encryption is great for data privacy and security, it has also become an opportunity for cyber criminals to conceal malware and evade detection. It isn’t feasible to decrypt and analyze encrypted traffic, and with the emergence of TLS 1.3, it won’t even be possible. Cisco has introduced a revolutionary technology, Encrypted Traffic Analytics (ETA), that is enabled by the next-generation Cisco network and Stealthwatch, to analyze encrypted traffic without any decryption. This allows organizations to detect threats in encrypted traffic, and perform cryptographic compliance to know how much of their digital business uses strong encryption and to audit for policy violations.
Our latest version of Stealthwatch includes new apps, one of which allows you to easily audit your network for cryptographic compliance. This app helps to analyze encrypted traffic for cryptographic compliance, using the Encrypted Traffic Analytics (ETA) technology. It provides an assessment of the “quality” of encryption being used, which is helpful to audit cryptographic compliance, for example, using SSL or early TLS violates PCI compliance. It also helps to understand trends and changes in the amount and type of encryption.
Go high-five your network architects and DevOps. Tell them we got this. Tell them to migrate to the cloud, spread your infrastructure across multiple public clouds, bear hug containers and Kubernetes, and embrace serverless architectures. You’re not worried about keeping it secure. Stealthwatch has you covered! See for yourself. Sign up for a free trial.