We are very excited to announce the new features of Cisco Stealthwatch! With release 7.0, we are introducing significant enhancements for the Stealthwatch administrator and the security analyst to detect and respond to threats faster, and manage the tool more efficiently.
Enhanced security analytics
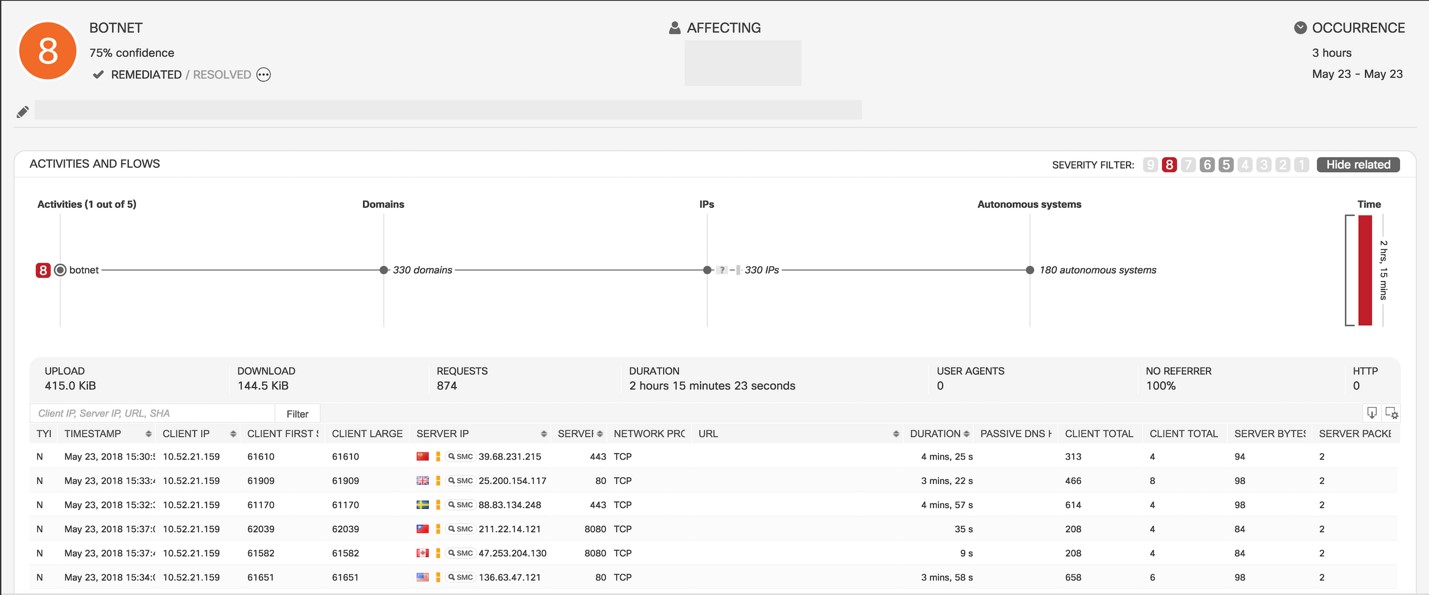
Threats continue to evolve, and so do the analytical capabilities of Stealthwatch for faster and high-fidelity threat detection. The cloud-based machine learning engine (Cognitive Intelligence) includes:
- enhancements for more efficient botnet detection
- ability to analyze and correlate proxy logs to network telemetry for increased efficacy
- option to apply analytics to specific internal servers
- auto-update for cryptomining classifier to detect unusual and new cryptomining pools, and more!
Context-aware mitigation
Stealthwatch is integrated with Cisco Identity Services Engine (ISE) to provide additional user and identity context around a threat detection. This integration also allows the security professional to take action to mitigate the threat right from within Stealthwatch. Here’s what’s new:
- Now, take selective mitigation actions based on the severity of the threat using ISE ANC (Adaptive Network Control) policies
- TrustSec Security Group Tags (SGTs) can now be pulled from ISE and are mapped to IP addresses, which provides the ability to implement more efficient network segmentation by using SGTs to create Custom Security Events within Stealthwatch
- Performance improvements and support for multiple ISE clusters allow large customers to scale user sessions
Watch video to learn more about Rapid Threat Containment with Stealthwatch and ISE
Better Control
Every organization is different with its own workflows. What might be considered suspicious activity within one, might not necessarily apply to another. And with security teams already strapped for time and resources, you don’t want to spend time chasing down irrelevant alerts, or worse, miss critical threats. Stealthwatch gives you an unmatched level of control to fine-tune security and customize it to the business logic.
Policy Manager Enhancements
These new enhancements provide:
- Unmatched control over security policy tuning in order to receive relevant alerts that are customized to business logic
- All three types of Stealthwatch security policies: core, custom, and relationship events, can be managed centrally by the admin, using the web interface
- Create, edit, or delete events easily
- With just one click, view the “effective policies” that are currently applied to a specific host, or drill down into an alarm to tune the event
Watch video to check out the security policy creation and management within Stealthwatch
User Manager and Host Group Manager enhancements
Now, you can manage users and host groups right from the web interface:
- Add Stealthwatch users and configure access to data based on their roles
- Classify hosts into Host Groups to effectively monitor for anomalies and threats based on the business workflows
Easier management
Don’t let management and upgrade hassles get in the way of effective and most up-to-date security! With the centralized appliance and update manager in the web interface, now you can configure, manage and update all the Stealthwatch appliances like the Stealthwatch Management Console (SMC) and the Flow Collector from one place. Spend less time managing the tool and more time using it for better security.
Stealthwatch Apps
Get new features on-the-fly that are completely independent from the rest of the functionality of your core system:
- Easy – addition of relevant functionality outside of the normal product update process
- Dynamic – Quicker adaptation of app features based on customer feedback
- Flexible – with your organization’s existing change and release processes
- Secure – Apps are vetted through the Cisco Secure Development Lifecycle (CSDL)
We are introducing three apps with this release:
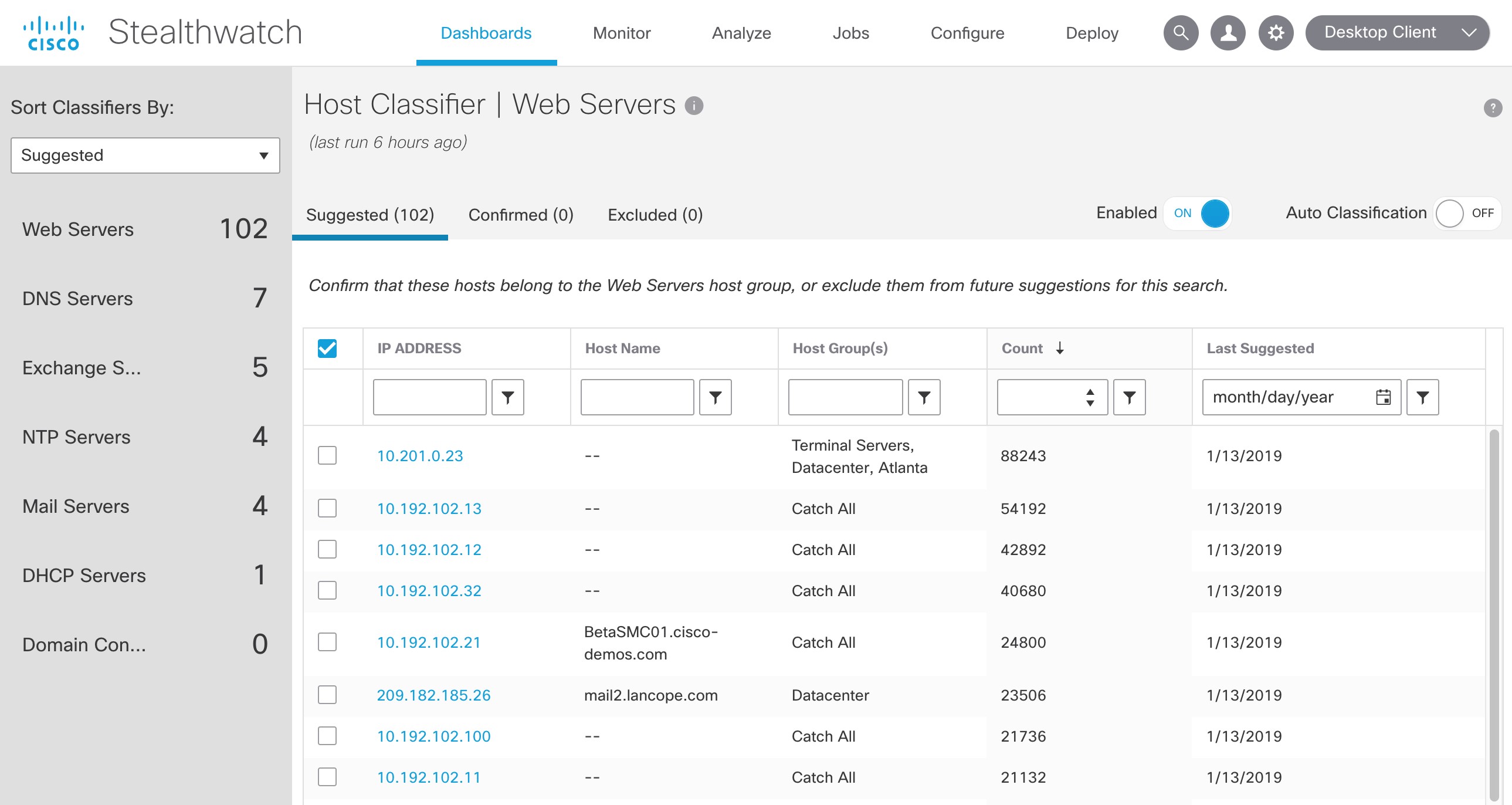
Host Classifier
This app provides dynamic discovery and classification of core assets in the network. It’s useful for initial system configuration as well as to continuously maintain host classification. Well-defined host groups lead to contextual and accurate alarms. Analysis is performed on-premises.
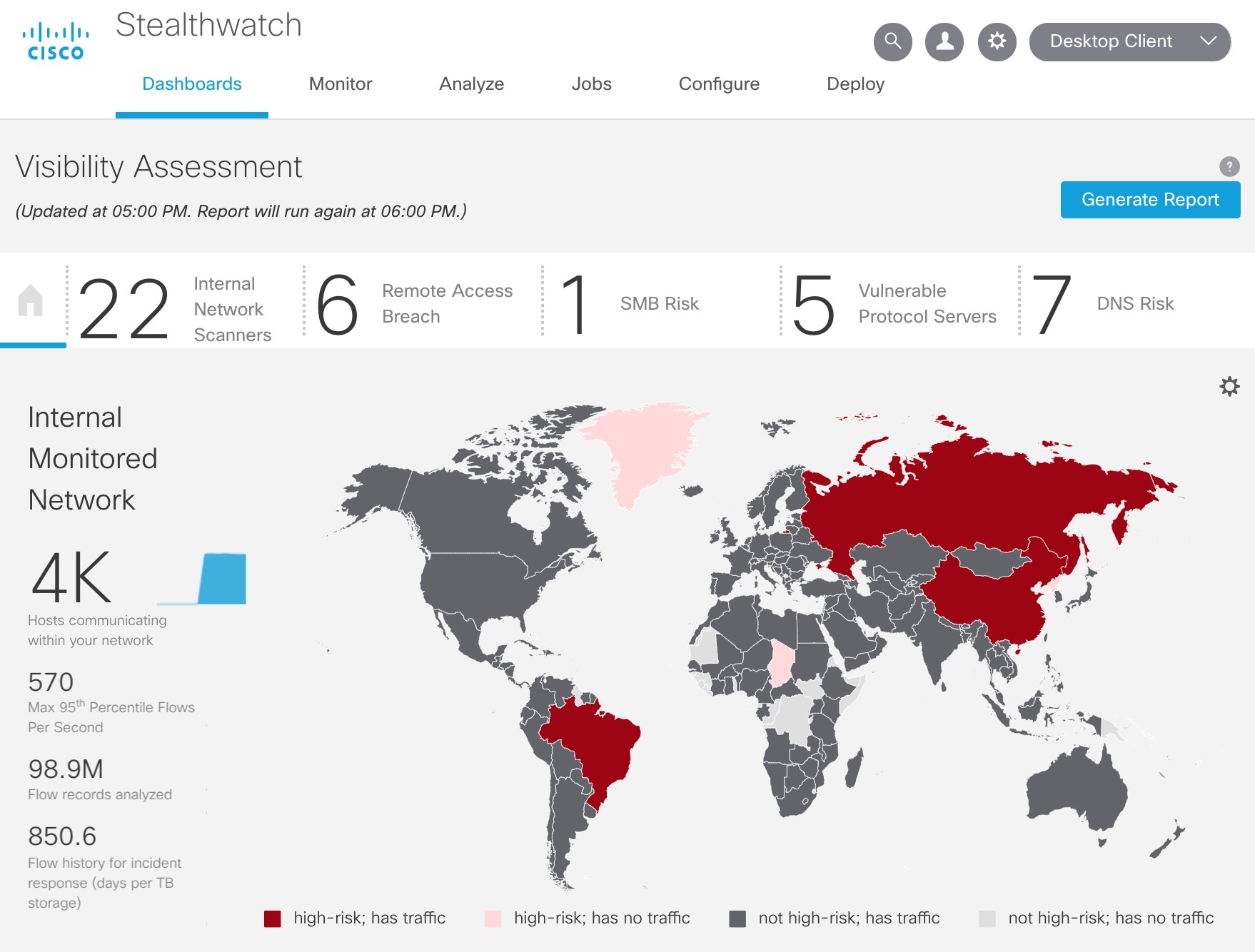
Visibility Assessment
Quickly gain insights into areas of security risks within the network, traffic to high-risk countries, and key network metrics. The app requires little to no tuning or host configuration. Stealthwatch users can also easily generate a printable summary report of the network for the executives.
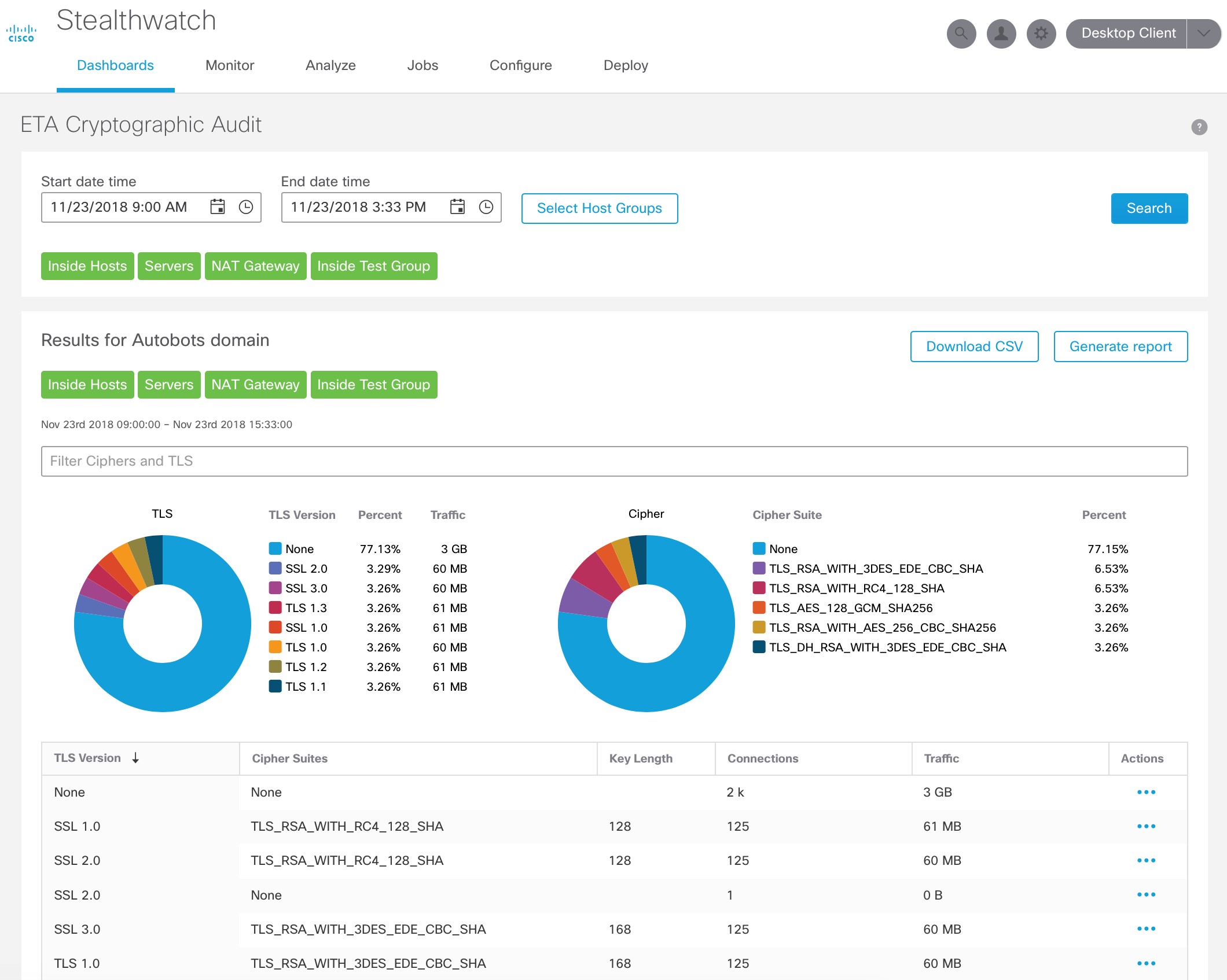
ETA Cryptographic Audit
This app helps to analyze encrypted traffic for cryptographic compliance, using the Encrypted Traffic Analytics (ETA) technology. It provides an assessment of the “quality” of encryption being used, which is helpful to audit cryptographic compliance, for example, using SSL or early TLS violates PCI compliance. It also helps to understand trends and changes in the amount and type of encryption.
To learn more about this release, check out the Release 7.0 At-a-glance and the Release Notes.
Don’t have Stealthwatch? Get started today with a free visibility assessment to find what’s lurking in your network.






When is it getting released to the public
Don: Stealthwatch release 7.0 that has all these features is already available to customers.