Looking back at 2018, malicious cryptomining emerged as one of the most prominent threats. As described in-depth in this blog, cryptocurrency mining, or cryptomining for short, is the process by which new coins are created or earned. However, the one key aspect that separates your regular, everyday cryptomining from what we consider malicious cryptomining is that the latter runs on the victim’s device, using up compute assets, without their knowledge or authorization. So that’s obviously a cause for concern.
Cryptomining is an activity that has a lot of variability in terms of how to respond to it and manage it: the client software can vary, the servers can vary, as well as the protocols used to communicate between the client and the server. Building a comprehensive defense will end up using multiple technologies and techniques to prevent, detect and respond to the activity. In this post, we will explore detection techniques using the network visibility and security analytics capabilities of Cisco Stealthwatch.
Let’s first zoom out and take a look at what cryptomining is from the network point of view: a very long-lived TCP connection between a client and a server, where the client device is continuously getting work from the server, doing the work (computing hashes), and submitting work back to the server. In this communication, the ports and protocol can vary, and the TCP communication can be encrypted. However, the nature of the communication must persist: because without constant communication to the mining pool, the asset will be unable to successfully complete its task.
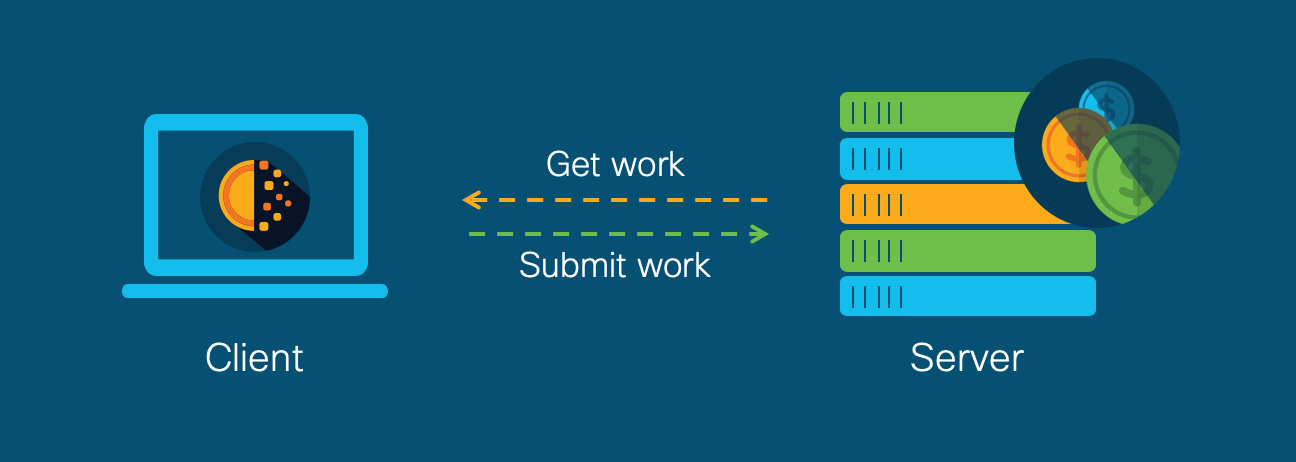
And therefore, security analytics applied on network telemetry, is an ideal method of gaining visibility and detecting the presence of cryptomining activity on the network, regardless of the endpoints involved. This is particularly of interest given the wide variety of software, including in-browser, and devices (think IoT devices like cameras, printers and phones) that may end up cryptomining.
Stealthwatch, a collector and aggregator of network telemetry for the purposes of security analytics and monitoring, has a number of analytical techniques that are relevant to the detection of cryptomining activity on the network. Let’s break down the three different ways in which Stealthwatch can detect cryptomining activity:
- Detection using unsupervised machine learning: Stealthwatch collects network telemetry and builds up a statistical model of entities in your network, creating observations of interest and generating alarms when behavioral or anomaly conditions are met. Two behavioral algorithms of direct applicability to cryptomining are the Suspect Long Flow and the Suspect Quiet Long Flow.
- Suspect Long Flow: Triggers when a logical Client-Server flow has been observed for a sufficiently long time (the threshold for duration of time can be tuned)
- Suspect Quiet Long Flow: Triggers when a logical Client-Server flow has been observed for a sufficiently long time and is of low byte count.
The nature of the unsupervised learning engine that constitutes the behavior algorithms of Stealthwatch helps to identify the cryptomining activity based entirely on its most fundamental behaviour: long lived communication between the client and the server, regardless of other factors.
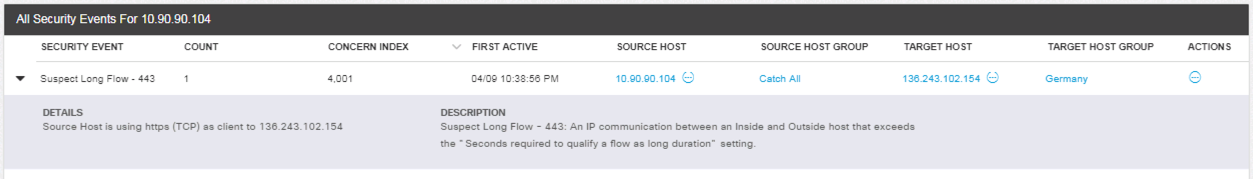
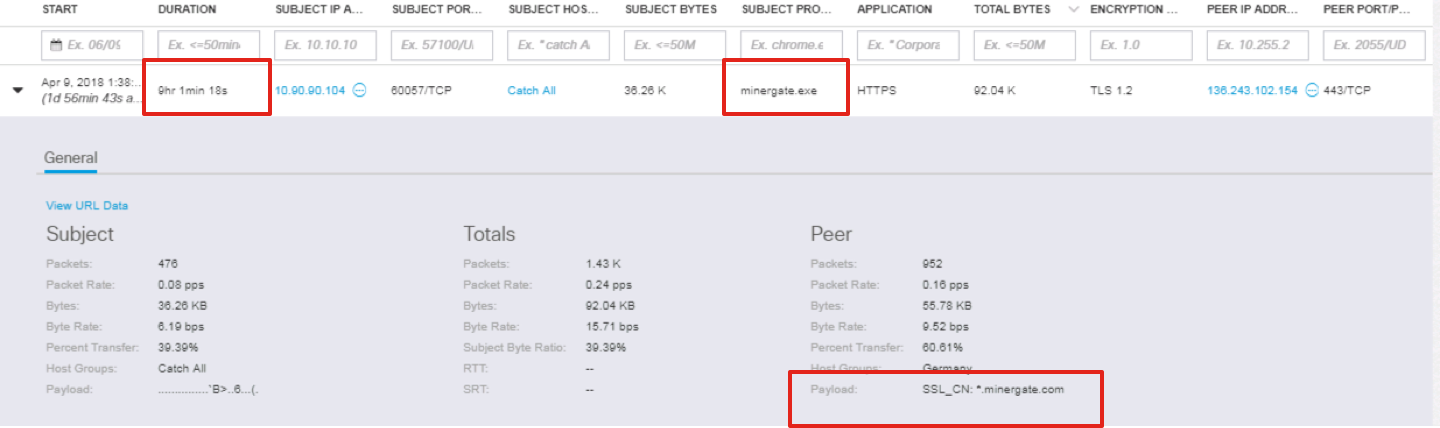
The below figures are an example of the occurrence of a Suspect Long Flow Alarm and the corresponding flow for a host that has been mining Monero using Minergate.exe for 9 hours, 1 minute and 18 seconds.
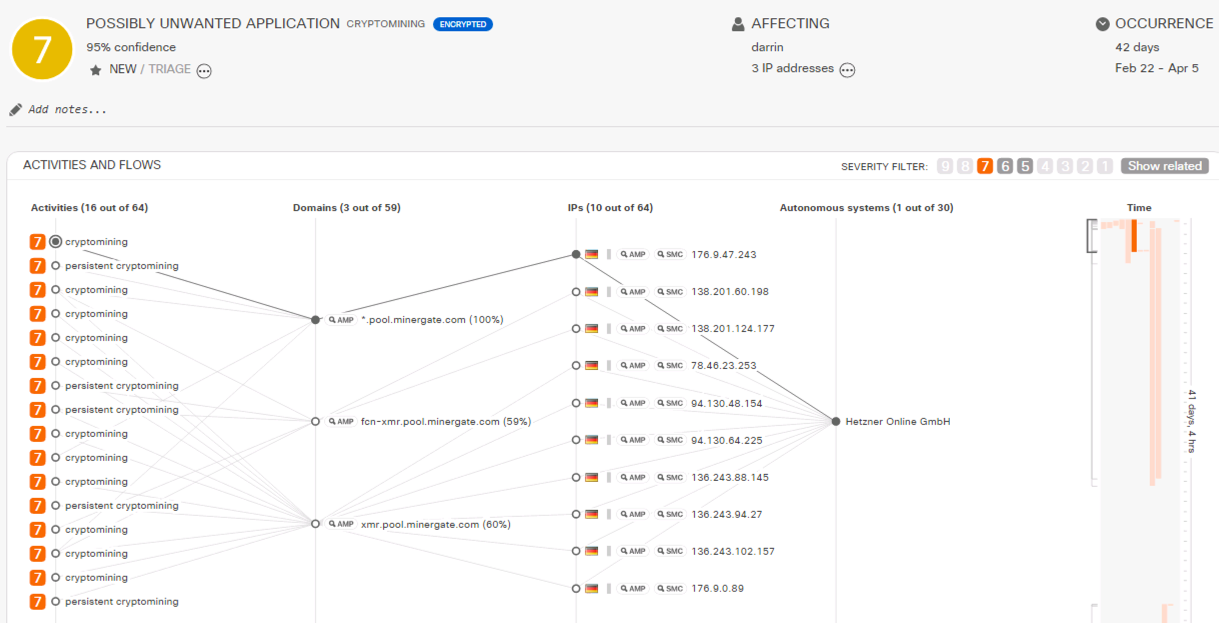
- Advanced detection using multi-layer machine learning: Stealthwatch is also integrated with Cognitive Intelligence, a cloud-hosted multi-layer machine learning engine that makes use of multiple analytical techniques including both supervised and unsupervised components. The advantage of operating in the cloud is the ability to actively profile servers around the world in addition to just those your organization would ordinarily interact with. This is often referred to as the Global Risk Map or Global Feature Cache. In addition to identifying suspicious activity such as Anomalous Periodic Flows, the supervised learning engine has been trained with classifiers to identify, with high confidence, cryptocurrency mining activity, as well as specific classifiers for certain cryptocurrencies, such as Monero and Litecoin. The figure below is an example of the identification of the user Darrin, having performed Monero cryptomining over three different IP addresses, over a period of 41 days and four hours.
In addition, leveraging the Global Risk Map, Cognitive Intelligence engine also tracks specific instances of threats, known as campaigns, such as in the screenshot below where the host 10.90.90.101 was confirmed to have been cryptomining using the Coinhive miner (#CCMM05).
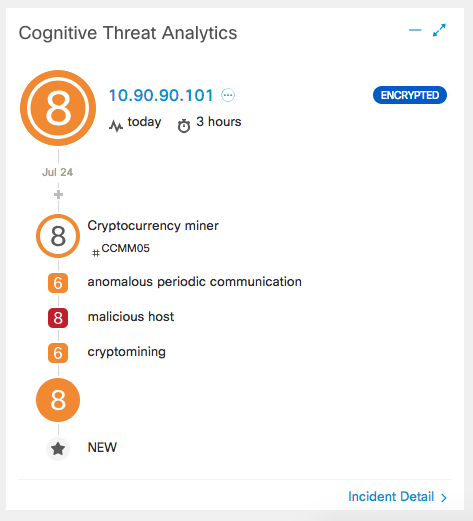
You’ll also notice the “Encrypted” tag in these detections. Stealthwatch, using Encrypted Traffic Analytics, has the ability to detect malware in encrypted traffic without any decryption. So you can also detect cryptomining activity occurring over encrypted channels!
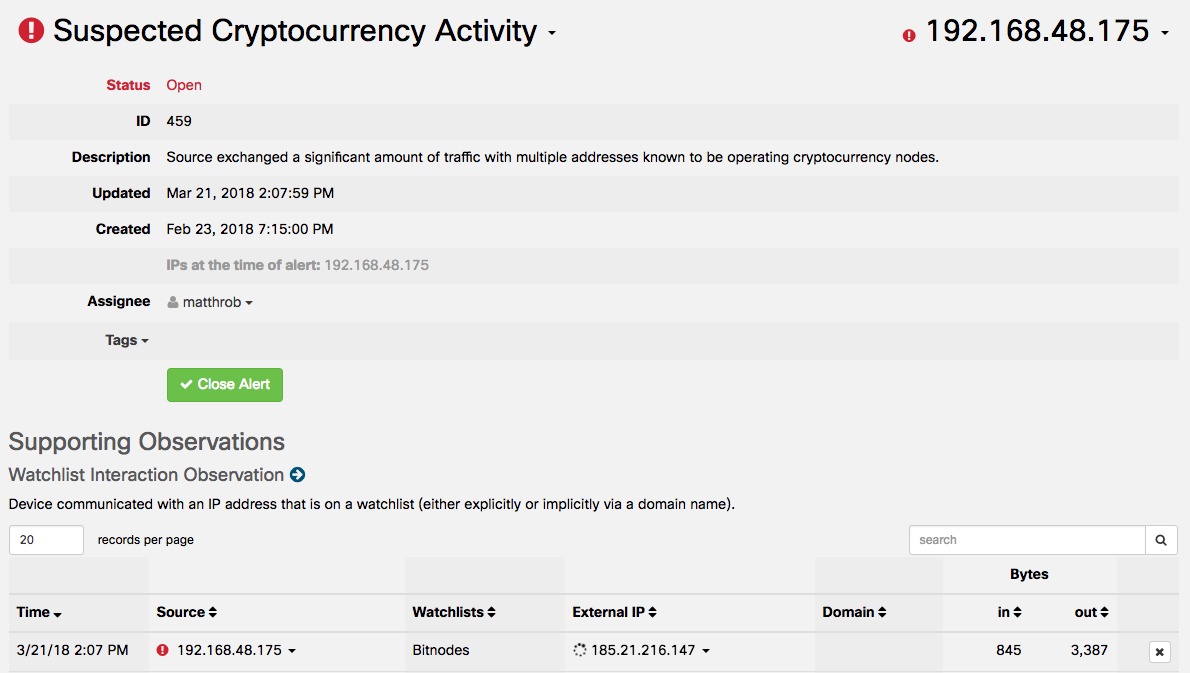
- Detection within public cloud infrastructure: Stealthwatch is also available as software-as-a-service with the ability to monitor on-premises network activity, as well as cloud-hosted infrastructure such as Amazon Web Services, Microsoft Azure and Google Cloud Platform, using native telemetry, such as VPC Flow Logs. It then analyzes this data using sophisticated modeling and machine learning techniques to identify suspicious and malicious activities. Cryptomining on cloud-hosted workloads can become very expensive, very quickly and having quick and effective detections of misuse of those assets is incredibly valuable to an organization. In addition to identifying activities like long flows, Stealthwatch Cloud also looks out for communication to known nodes for the Bitcoin and Ethereum networks. Below is an example of a detection in Stealthwatch where the host 192.168.48.175 exchanged a significant amount of traffic with nodes in the Bitcoin network.
Conclusion
Malicious cryptomining is a convenient way for threat actors to make some money and as such, can often be considered as a symptom to a larger problem: the threat actor’s presence on your systems. Building a defense against the cryptomining activity and ultimately the detection and management of the threat actor can take multiple technologies to prevent, detect and accelerate a response. The advanced and multiple security analytics techniques provided by Cisco Stealthwatch are capable of detecting cryptomining activity and surfacing evidence of that larger problem across the entire enterprise network, including IoT and cloud infrastructure.
Joining us at Cisco Live Barcelona? To learn more about dealing with malicious cryptomining using various Cisco Security technologies, check out breakout session BRKSEC-2323 – Claim Jumpers: Dealing with Illicit bitcoin miners in the network (Thursday, Jan 31, 2:30 pm – 4:00 pm).
To learn more about Cisco Stealthwatch, visit https://www.cisco.com/go/stealthwatch and take our free visibility assessment to see what might be lurking in your network.





