Dennis Perto is a Cisco Champion, an elite group of technical experts who are passionate about IT and enjoy sharing their knowledge, expertise, and thoughts across the social web and with Cisco. The program has been running for over four years and has earned two industry awards as an industry best practice. Learn more about the program at http://cs.co/ciscochampion.
==========================================
I am about to take you on a tour of the last few generations of Cisco firewall and their architecture to give insight in why the Firepower 2100 is not at all like the Firepower 4100 and not like a ASA5516-X either.
First, I would like to make a note of the lack of presenting the architecture of the ASA5505 and ASA5585-X even though they are still being used today. This is because they differ too much from the architectural evolution of Cisco firewalls and will not help with understanding why Cisco is choosing this specific path for the Firepower 2100 series.
I will start from the top down, with the best performing firewalls continuing to the least performing firewalls and why Cisco is replacing these.
High end architecture – Firepower 9300
A couple of years ago Cisco released a new architectural platform going away from the well-known ASA platform. We were first introduced to Firepower 9300 and subsequently to the Firepower 4100, primarily focused at data center deployments. These models are born with supervisors to make them modular, like several other high-end Cisco platforms. I hope that it will be possible to upgrade the supervisor to enable the use of two single-width 2x 100Gbit network modules (NM) in the 9300, or even to enable the use of future security modules requiring more than two 40Gbit links to the internal switch fabric. I am hoping for these theoretical wishes to come true.
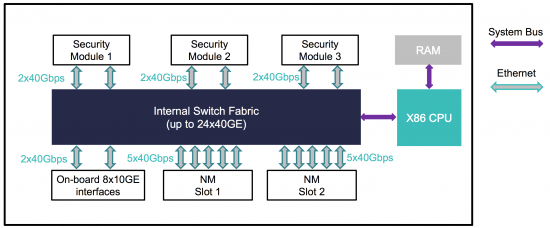
Looking at the block diagram of the 9300 above you see that the supervisor has its own CPU and RAM for controlling the operating system (FX-OS), which is used to deploy Firepower Threat Defense or ASA software to a security module and manage the network interfaces.
Downscaling great architecture – Firepower 4100
Firepower 4100 came to be due to the exorbitant cost of the 9300 series. The one thing not supported on the 4100 platform is the 100Gbit interfaces. There are 8x 10Gbit interfaces soldered in the chassis and it is possible to buy additional 1, 10 or 40Gbit interfaces in a network module. Fail-to-wire network modules is also a possibility on this platform.
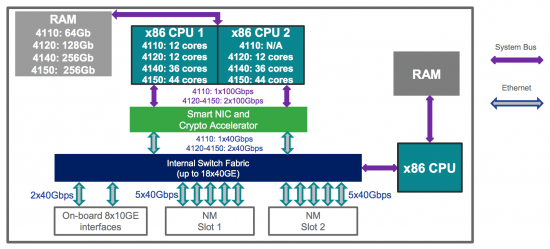
As seen on the image above, the 4100 series only have one security module compared to the possible three security modules in the 9300, but the architecture is the same as in its older brother.
Legacy firewalling – ASA5512-X to ASA5555-X
This ASA platform is probably the most used today. The reason for this is the performance and modularity. It does support three different IPS engines and the possibility to add more 1Gbit interfaces on the higher end devices.
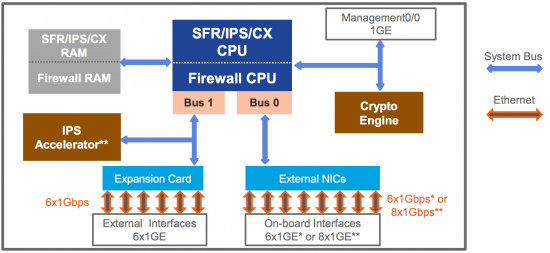
This block diagram above depicts the architecture of the ASA5512-X through ASA5555-X. The ASA5512-X and ASA5515-X have already been replaced with the newer ASA5508-X and ASA5516-X platform, and now the Firepower 2100 is supposed to relieve the ASA5525-X, ASA5545-X and ASA5555-X platforms of their duties.
Legacy upgrades – ASA5508-X and ASA5516-X
The replacing of the ASA5512-X and ASA5515-X was long overdue, but Cisco hit a soft spot with the customers with the ASA5508-X and ASA5516-X. The price-performance ratio was great for small customers and branches with the option to install Firepower Threat Defense for increased security.
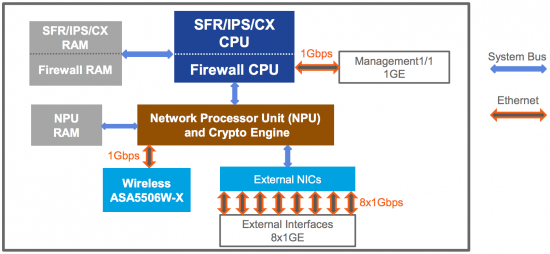
You should make a note of the placement of the NPU and compare it to the ASA5512-X to ASA5555-X platform. The NPU on this platform is doing most crypto tasks for IPSec and SSL VPN, just like the crypto engine used to do without the limitation of a system bus connecting the external NICs.
Finding the sweet spot – Firepower 2100
With Firepower 2100 being the youngest brother in the Firepower appliance series, Cisco took a step back towards the ASA X-series architecture. In this we have no supervisor in charge of the switching fabric or the networking interfaces. Everything is owned by the security module itself and this gives us an advantage in the direction of single box deployment management. On-box management is possible on the new Firepower 2100 series appliances but it is not possible on the 4100 nor the 9300 series. Under the hood of the operating system on the 2100 there is a small subset of the FXOS features needed to handle the interface configuration. The main difference (secret sauce) between the 5516-X architecture and the Firepower 2100 is that the NPU is not just used for crypto operations anymore. The new line also uses this NPU for layer 2 – 4 firewall operations and “fast path” traffic offloading. This is a great architectural step forward, but it is of course not as streamlined as the 4100 or 9300 series, where the Smart NIC is doing the traffic offloading and yet another NPU is handling the crypto operations. Personally, I like that every chip is made for specific problems, in opposite to one chip doing all kinds of tasks it was not optimized for.
As of Firepower Threat Defense 6.2 Active/Standby failover is possible on both the 2100, 4100 and 9300. Active/Active will be possible when the multi-context feature will be included in the FTD image. Clustering is unfortunately only supported on the 4100 and the 9300 appliances. Five 9300 chassis can be clustered with three security modules each, while sixteen 4100 appliances can be clustered.
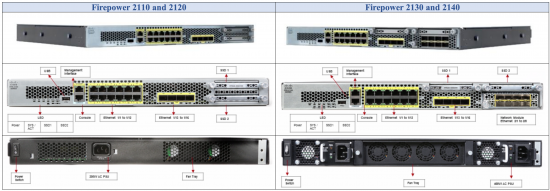
The Firepower 2110 and 2120 appliances come with 12 x 1Gbit RJ-45 ports and 4 x 1Gbit SFP ports with no options to expand this. This is a great rip and replace option for the current owners of the ASA5525-X, ASA5545-X and ASA5555-X firewalls. If you need to upgrade the edge firewall to 10Gbit you will need to buy either the 2130 or 2140 appliances. The Firepower 2130 and 2140 also come with the same 12 x 1Gbit RJ-45 ports as the lower end Firepower 2100 models. Along with this there is 4 x 10Gbit SFP+ ports and the option to put a network module (NM) card to add an additional 8 x 10Gbit SFP+ ports. Fail-to-wire network modules will be available. I do not expect 40Gbit interfaces to be available for this platform.
The Firepower 2100 is a great next generation firewall. As I see it the popularity of this will depend on two things;
1. The price. If it is too expensive customers will find another firewall manufacturer and buy a cheaper model with the same specifications.
2. The feature set. If the features of the ASA software is not implemented in FTD in haste the customer is forced to keep buying ASA X series or, again, go to another manufacturer.
Learn more about the Firepower 2100 appliances at Cisco.com.





Nice overview Dennis.
I would add that the stability of the features being built into the FTD image will be a key point in how quickly these new platforms are adopted.
Hi Marvin.
I agree. I can live with a lot of Firepower related bugs but I really need the basic ASA features and the stability hereof to back this operating system up. 🙂
Thanks for the informative article. I had to read it twice to ensure that not all of the ASA are becoming obsolete or as you say exorbitantly costly. It will be interesting to see what price Cisco puts on the 2100.
I’m sure that you will find the prices on the global price list within too long. 🙂
I think that the old ASA X will still be sold to those customers only needing ASA software for legacy firewalling.
Dennis,
Do you have a hardware overview slide for the 2100?
How about memory and CPU details?
I do.
For easy access of the hardware specs you can go to http://firepowerngfw.com 🙂
Good write-up. I certainly like this website. Thanks!
http://wwwcenturionwealth.com/
Hello,
very good overview. Do you know if it is already available the FTD image with multi-context feature to achieve the Active/Active high-availability for the 2100 series?
Thanks