While 2020 brought a barrage of unexpected disruptive challenges, they were mitigated somewhat by a variety of technologies that helped people stay safely connected and collaborating. Organizations of all types began using key technologies—from video conferencing for virtual meetings, connecting home offices to work applications, and extending compute resources from multiple clouds to micro-office sites—in order to maintain some semblance of normalcy in decidedly abnormal circumstances.
So, what will 2021 bring? What digital transformations should CIOs and CSOs be enacting to adapt to disrupted workplaces and workforces while supporting innovation in applications and workloads that drive business resiliency? Looking at the near future from the perspective of the Cisco Intent-Based Networking Group, here are five areas of digital transformations that deserve their share of consideration as we prepare for more potentially disruptive years ahead.
1. Preparing for Returning to Work with Connected Workplaces
Returning to the workplace will be very different for everyone. Post-pandemic, roughly 30% to 50% of the workforce will work partially or entirely at home. In the resulting hybrid workforce, some occupations will return to the office for hands-on collaboration, and others will either work full time at home or visit the communal office space for “moments that matter”.
Reconfiguring the workplace is essential to adapt to new health safeguards. Workstations will be dynamically allocated according to daily capacity. Video conferencing will likely replace group conference room meetings to meet social distancing requirements. One of the key findings from our Cisco 2021 Global Networking Trends Report—which included a survey of IT professionals by TechValidate ending in Aug 2020—is that 62% are deploying more pervasive video conferencing; 38% will monitor social density; and 32% are deploying proximity reporting.
Now—before the workforce returns—is the time to consider upgrading the infrastructure to support the new working environment. Streaming video to every device and desktop will require rethinking Wi-Fi coverage and capacity. Updating wireless access points to Wi-Fi 6 or 6e can alleviate the extra demand that video places on a building’s network.
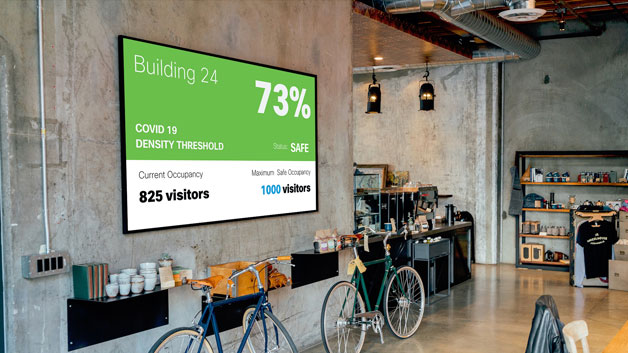
The location-enabled wireless access points also facilitate more efficient and safe use of spaces by monitoring usage and occupancy thresholds. Enterprises that deploy location detection and tracking can monitor activity on a floor by floor or even room by room basis to ensure that distancing rules are enforceable in real-time with automated notifications.
A natural follow-on to adapting the workspace for health and safety measures will be retrofitting entire buildings to make them smarter with sensors and Operational Technologies (OT) to better manage the internal environment.
2. Making Buildings Smarter to Improve Energy Efficiency and Safety
With the US re-entering the Paris Agreement in 2021, world governments will unify again to deal with climate change. One significant push by governments will to be demand and support smarter, healthier, and more energy efficient buildings—for both new construction and by renovating existing structures. This endeavor goes hand in hand with return to work planning as smarter buildings will include more sensors, more IoT devices, and thus more connectivity.

Enabling devices to monitor and control lighting, energy, occupancy, and filtration will increase network utilization. Availability of more spectrum with Wi-Fi 6 and 6e will help IT adapt to the increases in device density and provide different device types with their own Wi-Fi “swim lanes” with appropriate SLAs. Additionally, the arrival of fault-tolerant Universal Power Over Ethernet+ (uPOE+) providing up to 90 Watts of power, enables a vast set of connected use cases that were not previously possible. Phones, video conferencing systems, displays, computers and much more can now be powered and connected with the same easy and cost-effective Ethernet connections that are ubiquitous in almost all buildings.
The exponential increase in unmanaged devices—non-IT managed laptops or desktops—that are dependent on networks for connectivity and power means that IT must fundamentally change how they monitor and troubleshoot the network. IT must leverage next generation analytics for their operations and move to a more proactive stance. They will need to increasingly utilize AI/ML to rapidly discover the problems that matter most for business resiliency and workforce experience.
3. Unmanaged Devices Will Increasingly be Used for Cyber Attacks
The security of smart building devices and networks will of course be a priority. With so many different types of IoT woven into a building’s nervous system, any device that has the ability to connect to the internet is subject to malware and other threats. The network that integrates the IoT and OT of smart buildings must be able to augment an enterprises’ security capabilities and provide another layer of defense.
Unmanaged IoT devices are everywhere—at home, work, schools, hospitals, and transportation hubs—increasing the attack surface in proportion to their numbers. The number of cyber-attacks on IoT devices surged by more than 300% in 2019[i], and over 75% of vulnerabilities discovered in 2019 were from IoT devices[ii]. A recent IT survey revealed that internet-connected devices on enterprise networks can be hacked in as little as three minutes and breaches can take months to uncover. Botnets of hacked IoT devices have repeatedly wreaked havoc on many industries through DNS attacks.
To secure the constellations of IoT and OT devices, you first have to know what and where they all are. While it is relatively easy to view a list of generic devices connected to the same wireless network, for example, knowing their type, purpose, and what other devices they are communicating with requires a higher level of analytics. Here the network plays a dual role of connector and guardian with end-point analytics and a Device Classification System for group-based policy management.

Using passive network monitoring of telemetry and deep packet inspection to scan the network and identify devices by type, manufacturer, communication protocols, and ports, IT can automate the cataloguing all the devices on the network—wired and wireless, campus, and remote on the SD-WAN—and model the communications among them. With this understanding, IT can define policies for enforcing access permissions. If an inventory already exists in separate Configuration Management System, such as ServiceNow, or from Cisco Identity Services Engine (ISE) and Stealthwatch, those assets can be imported and assigned to appropriate groups. As new devices come online, they are automatically identified, tagged, and added to the appropriate security groups.
Understanding device types is the foundation for creating logical groups of IoT access control policies. Adding the ability to map ports and protocols to devices, along with deep packet inspection to identify malware in traffic, provides an early warning system for threats. Devices that suddenly start using different ports or protocols to communicate can be automatically isolated.
An Intent-Based Network employs a combination of device classification and monitoring, software-defined access, and intelligent segmentation to limit east-west propagation of threats and automatically quarantine devices when unusual behavior is detected. With an intelligent network as a platform for smart buildings and the connected workplaces, you’re well on the way to solving three of the biggest challenges of 2021.
4. Working @Home Will Remain a Necessity—or a Benefit—for Knowledge Workers
Even as organizations prepare for the return to the office by certain sectors of the workforce, many types of occupations benefit from the ability to work at home all or part of the time. Beyond the elimination of wasteful commutes and risky exposure to illness, working at home provides prime time for concentration on creative projects and much desired flexibility in work-life balance. It also enables organizations to hire the best talent no matter where they are located. Governments struggling to reduce carbon pollution to reach climate objectives will likely encourage organizations to support a significant contingent of remote workers. In order to do that effectively, IT will need to provide office-like connectivity to their remote workers while keeping enterprise assets secure.
From a teleworker’s point of view, an ideal home-to-business connectivity solution provides the optimum application experience for key collaboration and productivity applications that are core to their job. The foundation that makes this possible is reliable and secure end-to-end connectivity. However as many of us have experienced in 2020, quality of service can be severely impacted by local ISP outages, congestion from multiple devices at home, or bottlenecks across the internet. In 2021 IT will continue to enhance the teleworker experience by:
- Supporting more diverse office equipment in the home, making working at home more like working in the office. For example, home video conferencing systems can make a tremendous difference in the quality of experience for collaboration applications.
- Making the line between the office and home even more fluid, Cellular LTE/5G connectivity will augment broadband at home for business continuity or as secondary connection if the home broadband is overloaded with student classes and gaming.
- End-to-end observability of application performance and user experience that is inclusive of the home, the internet, and deep into the clouds to manage all the remote connections will be increasingly deployed.
- High-value workers’ intolerance for poor experiences will drive IT to deploy advanced SD-WAN solutions to the home that optimize the quality of experience for key SaaS and cloud applications.
- IT will have to take a proactive role in protecting home workers from other people and smart devices on the home network—such as keeping family and home IoT device traffic separate from sensitive business communications.
5. Unification of Ops Teams in the Applications Everywhere Paradigm
Now that we’ve covered digital transformation projects for workforce and workplace to maintain business resilience, let’s consider how the network can enhance the development and deployment of workloads to increase innovation. With operations increasingly distributed, workloads are quickly moving to multiple clouds. However, while new applications are primarily being built as cloud-native, there is often not a business case that justifies refactoring existing applications. Therefore, a hybrid environment will exist for the foreseeable future. Thus, there is an urgent need for Ops teams to work more closely together to manage application deployment in hybrid environments.
The internet is now a critical link in enterprise connectivity among public and private clouds, colocation centers, corporate data centers, and edge compute. Enterprises need a way to manage the infrastructure of these intertwined fabrics that connect developers, workloads, and hybrid-cloud platforms in order to facilitate innovative application development. Managing the security of such a wide-ranging network fabric is best accomplished with a unified NetSecOps team using a Secure Access Service Edge (SASE) framework with both edge and cloud-delivered security services. Combining the capabilities of Secure SD-WAN and cloud SASE enables NetSecOps to jointly deploy security to where it is needed to protect workloads in data center, cloud, and edge, as well as securing the workforce no matter where they access enterprise resources.
To orchestrate workloads in multiple public cloud and hybrid environments, automation is going to be key to enable businesses to provision infrastructure and run a Continuous Development pipeline. Infrastructure teams will want to retain control over the IT environment and choose what APIs they expose to development teams. One way to do this is to build an automated and secure interconnect between on-premises and cloud data centers for ease of provisioning and monitoring at scale in the hybrid environment.

From definition to deployment, application services will define networking and security requirements at the infrastructure layer, in an automated and fully synchronized way. Infrastructure as Code (IaC) enables IT Ops teams to embrace a DevOps model and accelerate application deployment, monitor operations, and optimize network compliance in a secure and predictable manner. Ops teams are using IaC platforms, like Terraform and Ansible, to programmatically configure data center and cloud infrastructures. This enables DevSecOps teams to work together on a unified platform to automate the management of both the network and server infrastructure, from data center to cloud.
Here again we see the importance of observability—the ability to monitor and maintain consistent network performance and access policies using deep analytic capabilities with machine learning for workloads deployed across on-premises and cloud locations. With these insights, NetSecDevOps can validate investments in cloud and data center container applications compared to business outcomes such as customer response times and application availability for teleworkers. Application development success depends on a highly flexible, available, and secure network that works in unison with the most popular IaC platforms.

Business Resiliency Requires an Intelligent Agile Network
While these five areas are ripe for digital transformation, the challenges we all face extend well beyond them. The resilience of all types of organizations depends on how quickly they can adapt to new disruptions while keeping their workforce productive, the workplace safe, and new innovative application workloads securely deployed on time wherever they are needed. We are here to build a bridge to make that possible. The network is fundamental to connecting people to the resources they need for businesses to stay competitive, safe, and resilient. Our teams at Cisco Intent-Based Networking Group are focused on ensuring the networking solutions we are developing today support your ability to stay agile in a complex world tomorrow.
[i] (Melissa Michael, Attack Landscape H1 2019: IoT, SMB Traffic Abounds, December 2019)
[ii] (Martin Zeisser, Talos Vulnerability Discovery Year in Review–2019, December 2019)






Such a clear, well-written, and really interesting blog- thank you!