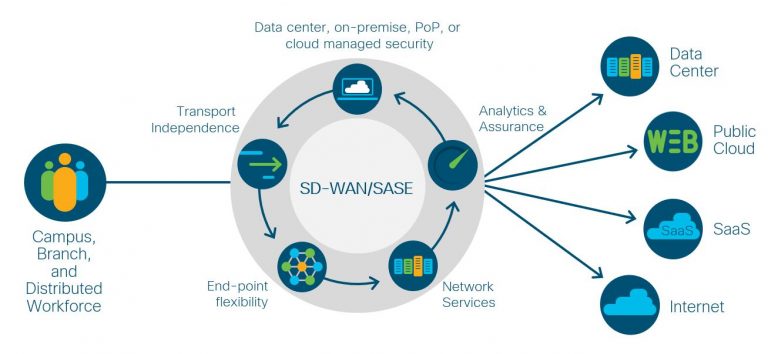
As the workplace becomes more disrupted and the workforce more distributed, data and applications need to be accessible from anywhere with both security and optimized performance. Organizations need a secure, agile network fabric to keep everything and everyone securely connected and collaborating. Just in time to meet this new normal of operations, Cisco SD-WAN is playing an outsized role in securely connecting data centers, cloud resources, SaaS applications, and the distributed workforce. Cisco Secure SD-WAN supports organizations in the ways in which they need to work today, while preparing for as yet unforeseen connectivity challenges in the future.
With Secure SD-WAN in use by over 6000 organizations, there is another evolution of wide-area networking on the horizon that will enable IT to adapt to the constant stream of disruptive forces from security threats and workforce realignments. It’s called various names by the IT analyst community, but typically referred to as Secure Access Service Edge (SASE) or Software-Defined Branch (SD-Branch). SASE is a software-defined architecture executed primarily in the cloud edge along with security and many network functions, including SD-WAN, Secure Web Gateway (SWG), Cloud Access Security Broker (CASB), Zero Trust Network Access, and Firewall as a Service (FWaaS).
There are critical use cases for SASE—especially in the context of remote workers and distributed branches that have minimal on-site IT support—where cloud-hosted security and networking is very efficient and effective. However, I think the key question IT needs to answer is: “What is the best architecture to meet the needs of business operations?” Are pure cloud networking and security services as defined in the SASE framework the most appropriate for all aspects of an enterprise? Are there cases when Secure SD-WAN is a better fit to solve application access and data protection scenarios? Are there remote sites—branches, WFH—that do not have access to high-bandwidth connections needed to send all SaaS traffic to a SASE cloud for security screening? What about using a flexible combination, so that SASE (pure cloud) and Secure SD-WAN (hybrid cloud, point of presence (PoP), and on-premise) can be applied as needed to fit specific use cases while relying on the same software-defined architecture to implement and manage it all? Let’s look at some of the reasons why you may want to differentiate implementations of secure wide area networking.
Traffic Flows, Latency, and Data Privacy Regulations Inhibit Cloud-Only Security
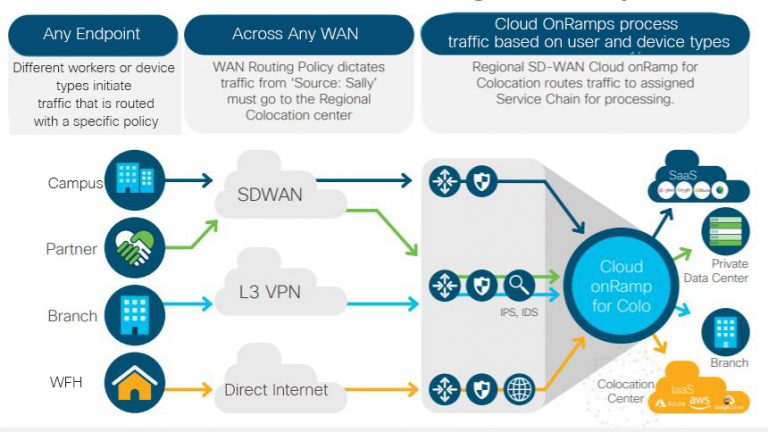
Just as every enterprise has differences based on geography, customer distribution, and type of business, within each enterprise are departments with separate operational needs and regulations. For example, direct internet connections to applications are very common now as branch and remote workers access SaaS providers directly without first tunneling through data center security services. In these cases, sending traffic to a cloud security broker makes perfect sense—especially when the next step is an on-ramp tuned for cloud application performance. In these cases, SASE cloud security is provided by Cisco Umbrella to protect both outbound and inbound traffic.
However, not all threats arrive from the internet. Many types of threats still propagate in enterprises in the east-west direction—using local traffic traveling from a device to an on-site application or among IoT devices. Protecting east-west / lateral flow traffic from spreading infections is better suited to segmentation with security groups which is beyond the scope of pure cloud security. Enterprise security segmentation policies are not available in the context of cloud security because it requires integration at the management layer, control plane, and data plane. However, segmentation can be managed via Secure SD-WAN with a centralized identity service engine (ISE) shared across the fabrics. At the same time, security policies can be implemented in a distributed manner close to the origin of the threats to prevent lateral movement as quickly as they are detected with AI End-Point Analytics.
In cases where predictable latency and optimized throughput is of critical importance, sending traffic over a WAN interface to a cloud security broker can increase end-to-end latency, which can lower the Quality of Experience for some use cases such as video conferencing. Requiring all traffic from a branch to flow through a cloud security broker makes optimizing the middle-mile much more complex to manage. Providing security in edge routers, at a branch or in a local PoP, enables NetOps to optimize middle-mile performance to keep applications performing as promised in SLAs. Whether in the branch or in a PoP, security policies are applied and traffic routed according to the application’s latency and throughput requirements.
Data privacy is a global variable that can affect how different geographic divisions of an organization can or cannot leverage cloud capabilities. Data privacy regulations like GDPR can prevent some organizations from adopting cloud-hosted security because personal data must be kept within specific geographic boundaries (countries, regions). California has more restrictive privacy laws than many other states, for example, so operations there need to treat personal data traffic judiciously when using cloud services for security. Organizations in the U.S. federal government also have privacy requirements that make it complicated to send data to cloud security brokers for processing. These types of regulatory requirements warrant the application of security policies on-premise before traffic exits the source and hits the WAN, therefore cloud-hosted security may be difficult to implement correctly. In these cases, the edge-based application-aware next generation firewall in Secure SD-WAN provides the necessary security protection for sensitive data.
Focus on Establishing the Necessary Security and Performance Policies Instead of Where Security is Applied
These examples demonstrate that there are optimal use cases for both SASE and Secure SD-WAN. A Software-Defined Architecture that supports both enables IT to implement security and network performance policies that are most appropriate for the changing workplace and workforce. Effective enterprise-wide security policy management should focus less on where the security functions are implemented and more on the types of policies that need to be enabled to protect data, applications, and devices while providing optimal performance for the workforce.
- Cisco provides unified security policy management across the network of branches, edges, secure internet gateways, colocation, and cloud with granular visibility through vManage and application-aware, enterprise grade firewalls, URL filtering, Snort IPS, Advanced Malware Protection (AMP), and Umbrella DNS-layer security.
- Cisco SD-WAN with edge security stack or SD-WAN with Umbrella Cloud Security (SASE) both leverage the Cisco Identity Service Engine’s Security Group Access Control Lists for segmentation policy management and enforcement across the WAN.
- When applications require very low and predictable latency, enforcing security policies on a Secure SD-WAN edge device like the Cisco Catalyst 8000 optimizes the middle-mile for secure application Quality of Experience.
- Security can also be applied in regional PoP/colocation providers to gain control over middle-mile performance and achieve more predictable latency results for applications.
- To provide unified security insights to stop threats before they spread, Cisco SecureX is a single dashboard for monitoring security events and incidents across the network fabric.
- Duo Zero Trust Network Access adds control over permissions to connect to applications and data resources with single sign-on policies.
You Can Have It All: SASE and Secure SD-WAN
As organizations adapt to changes in workplace, workforce, and application distribution, Secure SD-WAN enables enterprises to transition to a Secure Access Service Edge where and when it is needed. IT benefits by being able to provide both network agility and security in ways that best fit an organization’s structure and operations. Cisco’s continuous evolution of Secure SD-WAN with data center, edge, PoP, and cloud security offerings enable a smooth transition to whatever the next “new normal” may be.
Using the Cisco SD-WAN integration with Cisco Umbrella gives us effective cloud security throughout our SD-WAN fabric. We can now see which devices employees are using to connect to Tamimi Markets’ SD-WAN, restrict them to the most secure protocols, and even limit the applications they can use while connected to the network. We’ve never had application visibility like this before. This added security protects our staff from the ever-present threats on the internet.
— Joel Marquez, IT Director at Tamimi Markets
Vistara airlines is able to perform consistent, future-ready security checks across DNS and firewalls, while defining communication frameworks across its offices and IT offices. “Vistara’s growing business required a strong and cost-effective solution to run a spectrum of applications with minimal downtime and maximum performance. Cisco’s SD-WAN was the right solution to help us do this. (With) Cisco SD-WAN, our network topology is now optimized and centralized across all of our operations and IT offices, making it easier to manage data and incrementally save costs.”
Subhash Kumar Mishra Head of IT Enterprise, Vistara
For more information read a white paper on the Roadmap to SASE or visit the SASE webpage.






Great overview and use cases, Ravi. Thank you
Ravi,
Solid overview of how It all comes together. Infographics are well done, easy to visualize the complete solution.