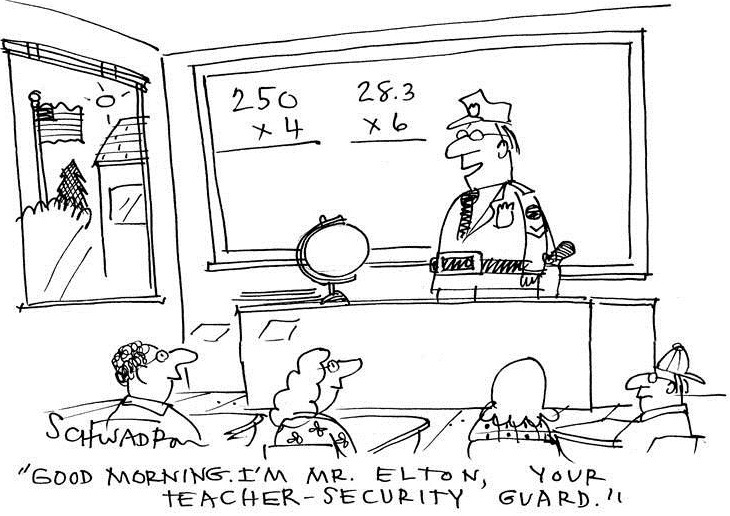
So many students, so many devices, yet zero increase in number of IT staffers. The increasingly unbalanced ratio is enough to cause a few nightmares for any IT professional. Luckily, supporting student IT requirements, while remaining secure, has become a bit simpler with Identity Service Engine (ISE) Policy Deployment, part of Cisco BYOD Solutions for K12 Education. With ISE, IT staffers can quickly add and support student’s devices like laptops, smart phones and tablets and at the same time ensure the protection of student information access, dynamically control who gets access to what and provide optimal network user experience. You can be rest assured that we have your back while you balance it all.

Protection of Minors – Let’s face it – K-12 means we’re talking about minors, so we need to tread quite carefully. Extending network access across wired and wireless opens education to a world of innovation; yet it also opens the network up to security threats. 64% of parents feel it is a schools responsibility to effectively teach students how to use their mobile devices safely [Info graphic]. Protection of access to and access by students is a high-priority. It is critical to restrict access to confidential student records while making sure students get the right access to resources they need for learning. The ISE component of the K12 BYOD Solution protects student information through secure, role-based, application access – simply – over the wired and wireless infrastructure.
Ensure Performance – Too many mobile devices slowing down the network? Not a problem! IT administrators can leverage ISE of the K12 BYOD Solution to easily distinguish between groups (students, teachers, staff), devices (wired or wireless), and location. ISE allows you to prioritize between student and teacher application usage and access to ensure optimal network performance for education purposes. IT needs to provide selective access to ensure that teachers can leverage sites such as YouTube for educational purposes, while limiting student access to potential bandwidth drains and possible mal-content exposure. Alternatively, unilaterally ban BitTorrent access since it does nothing but act as a network drain and could expose the network malware.

ISE helps easily optimize network performance with simple, role-based application access across wired and wireless.
IT Simplification – In K-12, there’s guest access, student access, teacher access and staff access, all of which could either be over desktops, laptops, tablets, or smartphones. Each user’s devices require device authorization, device profiling, device registration, certificate enrollment -the list goes on- in order to provide BYOD for school districts. With the number of devices on a schools network, it would be staggering to go through this process with each device. Worry not…

The ISE component of the K12 BYOD Solution simplifies this for the IT department. One way that ISE simplifies device onboarding is by enables each device the access to combining both authentication and authorization into one appliance. In this way provides a simple solutionfor school districts supporting a BYOD strategy.
Cisco BYOD Solutions for K12 Education offers a flexible solution for small, medium, and large school districts. ISE Policy Deployment empowers IT staffers’ to easily provide secure access and efficient network performance while enabling schools to innovate education for their students.
To learn more about Cisco K12 BYOD Solutions, you can watch our 3-part webcast series, now available on demand on the Cisco Enterprise Networks Community. Also, be sure to visit the Cisco BYOD Solutions for K12 Education page to see how different school districts are innovating education and transforming their classrooms.
This is the third installment of the Cartoon Catalyst Blog Series. Be sure to catch up on the series by reading the first two installments:
1) [Cartoon Catalyst Blog Series] The New Age Textbook – Implications of BYOD on K12 Education
2) [Cartoon Catalyst Blog Series] Why deploy Pervasive Wireless for K-12. Who’s doing it and how.
Also be sure to visit –
Image Sources (By order of appearance)


CONNECT WITH US