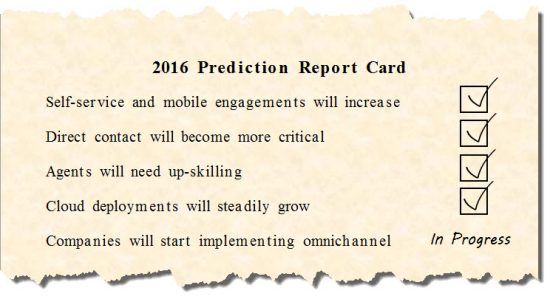
Organizations aren’t just talking about digital transformation – they’re doing it: More than 75 percent of global business leaders cite digitization as a top strategic priority and nearly seven in ten say their company will meet its digital transformation objectives this year, according to a recent survey from The Economist Intelligence Unit.
To advance these initiatives, organizations are primarily focused on boosting capabilities in Big Data/analytics (as cited by 58 percent of survey respondents), mobile computing (36 percent), Software as a Service (29 percent), Infrastructure as a Service (26 percent) and electronic payments (21 percent). Additionally, according to a recent report from PwC, more than half of organizations have also increased their security spending to support their digitization efforts.
These capabilities are frequently coupled with an intensified interest in social media and the Internet of Things (IoT) and are clearly revolutionizing business practices. But they’re also increasing risk, giving cyber criminals more opportunity to compromise networks and systems and steal valuable data. Such attacks are draining bottom lines, with the average cost of a data breach now totaling $4 million, up 29 percent since 2013, according to research from the Ponemon Institute.
That’s why cyber resilience is so critical for organizations today. At Cisco, we define cyber resilience as the ability to prepare for and adapt to changing threat conditions while withstanding and rapidly recovering from attacks to infrastructure availability. It is largely about managing risk – identifying events that might happen; assessing how likely they are to happen and the impact they could make; and deciding what actions to take.
We recently published a white paper on this topic, titled “Cyber Resilience: Safeguarding the Digital Organization.” In the paper, we outline a multidisciplinary capabilities framework that should serve as the foundation of your cyber resilience program. Key capabilities include:
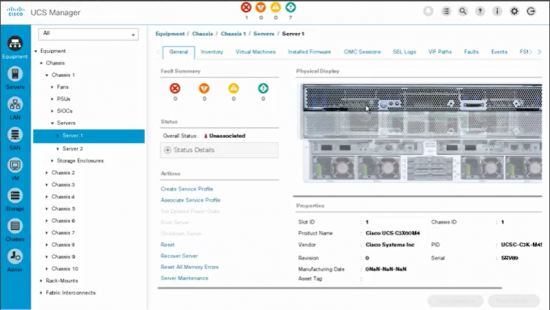
Identification. First, you need to identify your most valuable assets, so you can make informed decisions about risk and investment. It’s also necessary to perform an asset management and risk assessment. To achieve this, it’s essential to be able to know and authenticate all systems in your network architecture, so one party can confidently identify another party. You must know which devices – with specific cyber resilient capabilities – form the foundation of your cyber resilience and business competencies. You must also know where your business-critical data is and understand its resiliencies. Only then can you develop and maintain a security strategy.
Protection. The next step is to limit or contain the impact of attacks. Policies, processes and mechanisms ensure that systems are built and operate in a state of integrity during an attack, and that they are defended from modification from unauthorized or unauthenticated processes.
Detection. Security teams must constantly measure, collect, verify and analyze system integrity to enable timely discovery of a threat. Detection solutions provide behavior notifications, logging and forwarding events related to unexpected and possibly harmful user behavior or network activity.
Recovery. Recovery restores the normal operation of platforms, apps and services if they are corrupted by a compromise. New platform capabilities, for example, will allow an agent to run and correct or replace compromised components, including firmware, applications, user data, configuration data and software. This greatly reduces costs and downtime when an attack occurs.
Visibility. With visibility mechanisms supporting protection, detection, recovery, analytics and forensics, you assure continuous awareness of system integrity. Visibility tools are typically integrated with other cyber resiliency functions to establish a coordinated security and compliance posture that can reveal the state of system integrity to administrators, users, tools, applications or third parties. With this, IT continuously monitors and tracks the state of integrity of all organizational informational assets.
Analytics. Through analytics, you examine incident data to augment situational awareness, helping security teams distinguish events that pose the greatest risk. In addition, these tools reduce the time from detection to recovery, paving the way for the proactive defense of your network.
Forensics. Teams ingest relevant support data, while preserving, processing, analyzing and presenting system-related evidence in support of recovery.
A complete digital transformation requires a roadmap – not only of the technical investments that will advance business performance, but of the tools, policies and processes that will protect your investments. These capabilities will not entirely eliminate cyber risk; but they create awareness to the risks and will build a formidable defensive posture to significantly reduce the impact of threats.