Today, Microsoft has released their monthly set of security bulletins designed to address security vulnerabilities within their products. This month’s release contains twelve bulletins addressing 37 vulnerabilities. Five bulletins are rated critical and address vulnerabilities in Internet Explorer, Edge, Windows Journal, Office and Windows PDF. The remaining seven bulletins are rated important and address vulnerabilities in the Network Policy Server (NPS), Active Directory, Windows, Remote Desktop Protocol, WebDAV, Kernel Mode Driver and the .NET Framework.
Bulletins Rated Critical
Microsoft bulletins MS16-009, MS16-011 through MS16-013, and MS16-015 are rated as critical in this month’s release.
MS16-009 and MS16-011 are this month’s Internet Explorer and Edge security bulletin respectively. In total, sixteen vulnerabilities were addressed with four vulnerabilities impacting both browsers. The vulnerabilities impacting both browsers include three critical memory corruption issues (CVE-2016-0060, CVE-2016-0061 and CVE-2016-0062) along with CVE-2016-0077 that addresses a critical spoofing vulnerability.
- MS16-009 is the IE bulletin for IE versions 9 through 11. Three critical memory corruption issues specific to Internet Explorer are addressed (CVE-2016-0063, CVE-2016-0067 and CVE-2016-0072).
- MS16-011 is the Edge bulletin. A critical memory corruption issues specific to Edge is addressed (CVE-2016-0084).
 Get the Podcast
Get the Podcast
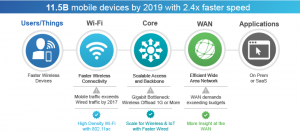 When I talk to network professionals, I routinely ask them about the one part of their job that keeps them up at night. The thing that consistently comes up is their network speed required for delivering a consistent reliable user experience: or specifically, the lack of it. They usually follow up this admission by saying that their network is not always slow, but the rate at which the business introduces new applications and new ways of leveraging technologies is definitely trending towards the network not being able to keep pace.
When I talk to network professionals, I routinely ask them about the one part of their job that keeps them up at night. The thing that consistently comes up is their network speed required for delivering a consistent reliable user experience: or specifically, the lack of it. They usually follow up this admission by saying that their network is not always slow, but the rate at which the business introduces new applications and new ways of leveraging technologies is definitely trending towards the network not being able to keep pace.