Safe. The very sound of it resonates with security. It is with some irony that Cisco has decided to reuse the term. Why ironic? For one, there is the idea among security folk that in reality, nothing is entirely safe. Why would Cisco sell intrusion detection if no intruders can, well…intrude? For those of you who remember SAFE from the early days of Cisco, it might seem like a familiar friend that has grown up a bit. Cisco historians ask, “What does SAFE stand for?” In our underground tunnels that forge firewalls and FirePOWER, you might get responses such as “Security Architecture for Enterprise” or “Secure Architecture for Everything.” In truth, the meaning has been lost to the annals of time.
One thing that everyone can agree on is that security is growing more complex by the day. While attackers are developing more lucrative schemes and advanced threats, security professionals have been running faster and faster in a race to keep up. Most organizations have deployed security technologies across some combination of networks, endpoints, web and email gateways, virtual systems, mobile devices, and the cloud. But how do we know that we have all of the right capabilities at the right places across the extended network? This is where SAFE comes in.
Cisco aims to simplify security because it realizes that the increasing fragmentation of the technology multiplies the attack surfaces, which in turn complicates the defenses. The industry desperately needs a resource that looks at the problem from an end-to-end perspective, but also makes it easier to understand. The solution has to be comprehensive, credible, and more than just about products. It needs to focus on the threats of the industry.
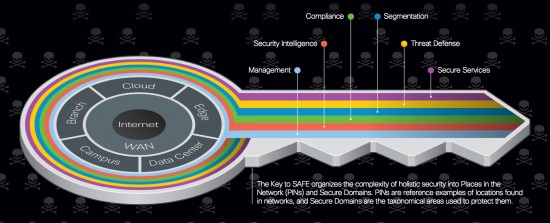
With that intention, Cisco is relaunching SAFE. SAFE simplifies security by employing game theory with building blocks focused on threats and the best practices for defending against them. It is not a perfect model; no model is. But with SAFE, you can use simple concepts to focus on the complex ones. You can break down the network into building blocks that simplify its design, build, and maintenance—with security baselined in its DNA.
SAFE is designed with a common language to facilitate frank discussions about security architectures. When used correctly, it can help protect the whole company, from end to end.
Read the SAFE Overview Guide or go to cisco.com/go/SAFE to learn more about SAFE and see if you can identify gaps in your security architecture. And most off all, stay SAFE out there!






Security @ Layer 8 also needs to be consider. As nothing can work if end user don’t get it correct. My view Awareness is much more critical and has very limited control.
Agreed! If you follow the link to the SAFE overview guide you will see that we start with the humans; both malicious and benign. To your point, if the human is compromised, the rest of the controls are a lot easier to get around. Thank you for the comment!
Christian
Nice! Just downloaded the pdf and am already liking it. Thanks Christian 🙂
Awesome to hear, Melinda! We put a lot of work into it to make things as simple as can be for such a complex topic. Thank you so much for the feedback! Best, Christian