If you had a million airline miles, where would you travel?
Kyle Lovett, a security penetration tester with the Advanced Services Security Team is asking himself that very question right now. That’s because his United Airlines mile bank is overflowing, thanks to a security bug he found through a bug bounty United Airlines was offering.
Bug bounties are nothing new, they’ve been around for a while, usually offered by big tech companies. It’s an opportunity for white-hat “hackers” (those using their powers only for good) to find security vulnerabilities for rewards. United is the first airline to offer a bug bounty.
Kyle lives and breathes security. He says he’s been “breaking things” since he was a kid. It’s a part of his day-job, but also something he enjoys in his free time. Normally, he doesn’t participate in bug-bounties, but in the case of United, he was intrigued.
“Sometimes, a company will recognize the work with a good reward,” Kyle says. “What caught my eye [with the United bug bounty] is that they were giving away miles. But they were significant miles. So I sat down one Saturday morning and got to work.”

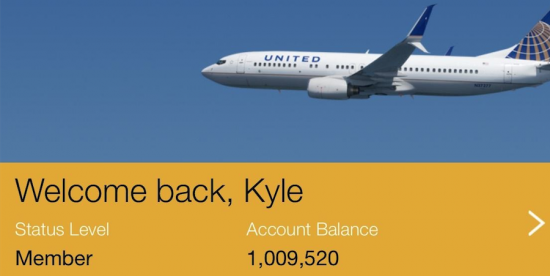
Kyle got to work for sure. In a few hours, he’d made several different submissions. One of those submissions was significant enough to get United’s almost immediate attention. He’s under agreement not to say what the bug was, but it was big enough to earn the largest prize in the bug bounty – he’s now in the million mile club.
“United reached out to me with questions and clarifications,” he explains. “We went back and forth over the course of a week, and they had it fixed in a few days. Then they said ‘Congratulations! Here are a million miles.’ They were genuinely concerned about the bug and very professional.”
He opened his United app, and saw the seven-figure number. A million miles means approximately 40 domestic round-trip flights, 20 round-trip flights to Europe, or eight first-class trips. Here’s the kicker. He still has additional submissions that might earn him MORE miles.
How will Kyle put them to use? He’s already bringing his mom and brother out from Virginia to visit him in California. His job gives him a lot travel opportunities as well, so he’s a little stumped right now.
“I’ve always wanted to go to East Asia or the Southern Pacific. Not for the scenery (although that’s nice). I’m more intrigued to see the culture,” he says. “But I would like to give at least one ticket away for someone who might really need it, maybe for medical treatment or they can’t afford to get home.”
How’d Cisco get so lucky to have such a great security tester on the team?
“The Internet of Everything is near and dear to my heart, especially the security around it,” Kyle says. “There is such a large wealth of people to reach out to in all different areas. And the culture and atmosphere here is genuine. I’ve not met one person who works here that doesn’t enjoy what they do!”
Want to join Kyle and the Cisco Security team? See open security jobs here.




 Networking Field Day 10 this year. Cisco brings together independent thought leaders and our engineers to share information and opinions in a two-hour interactive discussion format. If you cannot attend NFD10 all presentations will be live streamed from the
Networking Field Day 10 this year. Cisco brings together independent thought leaders and our engineers to share information and opinions in a two-hour interactive discussion format. If you cannot attend NFD10 all presentations will be live streamed from the 