This post was authored by Andrea Allievi, Ben Baker, Nick Biasini, JJ Cummings, Douglas Goddard, William Largent, Angel Villegas, and Alain Zidouemba
Cisco’s Security Solutions (CSS) consists of information security experts with a unique blend of law enforcement, enterprise security and technology security backgrounds. The team works directly with Cisco’s Talos Security Intelligence & Research Group to identify known and unknown threats, quantify and prioritize risk, and minimize future risk.
When consumers make purchases from a retailer, the transaction is processed through Point-of-Sale (PoS) systems. When a credit or debit card is used, a PoS system is used to read the information stored on the magnetic stripe on the back of the credit card. Once this information gets stolen from a merchant, it can be encoded into a magnetic stripe and used with a new card. Criminal markets exist for this valuable information because the attackers are able to easily monetize stolen credit card data. Incidents involving PoS malware have been on the rise, affecting many large organizations as well as small mom-and-pop establishments and garnering a lot of media attention. The presence of large amounts of financial and personal information ensures that these companies and their retail PoS systems will remain attractive targets.
Overview
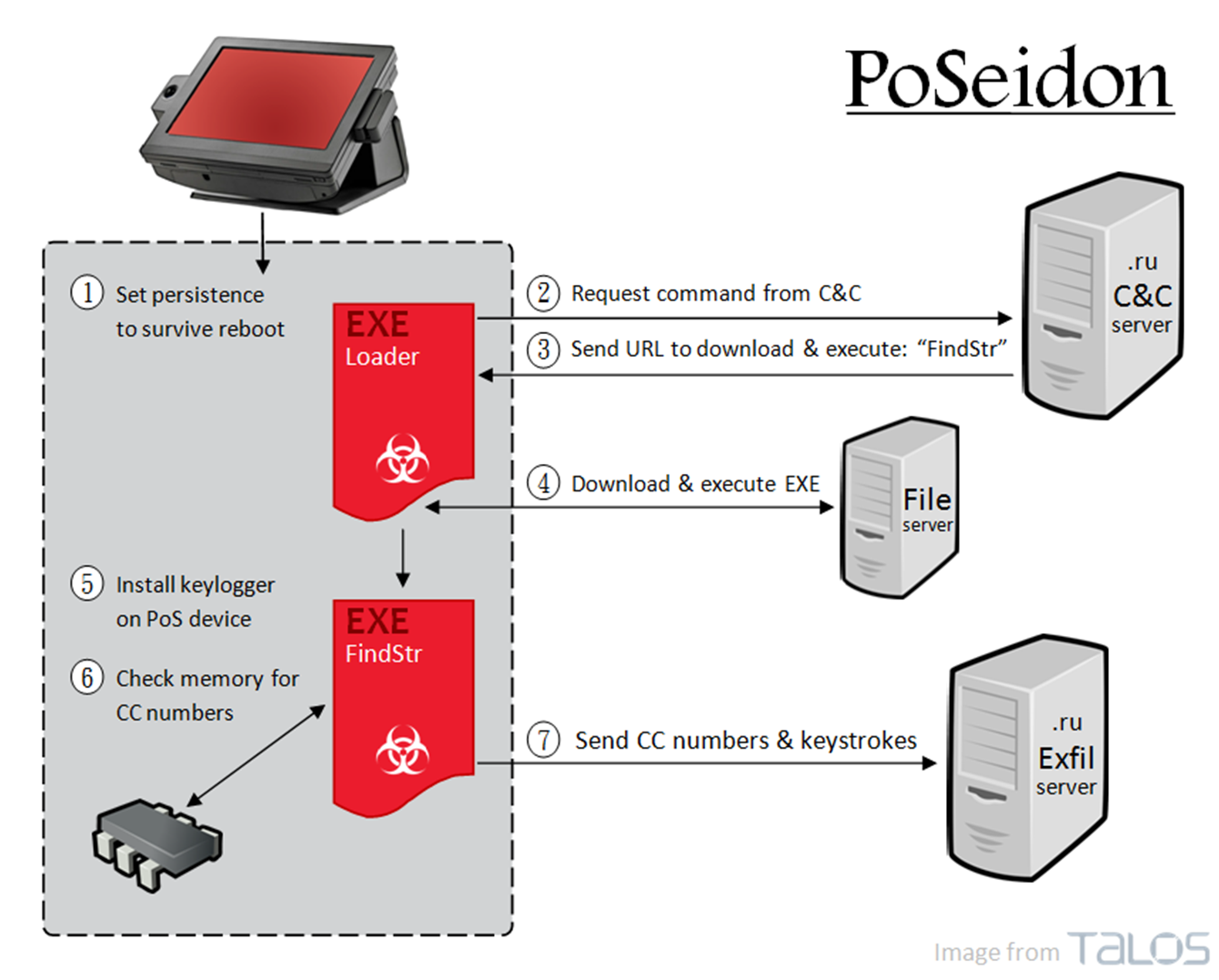
There is a new malware family targeting PoS systems, infecting machines to scrape memory for credit card information and exfiltrate that data to servers, also primarily .ru TLD, for harvesting and likely resale. This new malware family, that we’ve nicknamed PoSeidon, has a few components to it, as illustrated by the diagram below:
At a high level, it starts with a Loader binary that upon being executed will first try to maintain persistence on the target machine in order to survive a possible system reboot. The Loader then contacts a command and control server, retrieving a URL which contains another binary to download and execute. The downloaded binary, FindStr, installs a keylogger and scans the memory of the PoS device for number sequences that could be credit card numbers. Upon verifying that the numbers are in fact credit card numbers, keystrokes and credit card numbers are encoded and sent to an exfiltration server.
Continue reading “Threat Spotlight: PoSeidon, A Deep Dive Into Point of Sale Malware”
 Guest blog by Greg Nehib, SP Product and Solutions Marketing
Guest blog by Greg Nehib, SP Product and Solutions Marketing of students from around the world, with 1,400 students from over 35 countries. One value that sets the school apart is its commitment to using technology in the classroom. For instance, every student has a laptop that they use to access e-books, watch educational videos, and complete homework assignments. Some exams are even taken digitally.
of students from around the world, with 1,400 students from over 35 countries. One value that sets the school apart is its commitment to using technology in the classroom. For instance, every student has a laptop that they use to access e-books, watch educational videos, and complete homework assignments. Some exams are even taken digitally.
 Guest Blog and Interview by Christine Morgner
Guest Blog and Interview by Christine Morgner