Speaking to many CISOs, it’s clear that many security executives view zero trust as a journey that can be difficult to start, and one that even makes identifying successful outcomes a challenge. Simultaneously, the topic of security resilience has risen up the C-level agenda and is now another focus for security teams. So, are these complementary? Or will they present conflicting demands that will disrupt rather than assist the CISO in their role?
One of the most striking results coming from Cisco’s latest Security Outcomes Report is that organizations with a mature zero trust implementation – those with basic controls, constant validation and automated workflows – experience a 30% improvement in security resilience compared to those who have not started their zero trust journey. So, these two initiatives – implementing zero trust and working to achieve security resilience – appear to complement each other while supporting the CISO when a cyber black swan swims in.
Security resilience is the ability to withstand an incident and recover more strongly. In other words, ride out the storm and come back better. Meanwhile, zero trust is best known as a “never trust, always verify” principle. The idea is to check before you provide access, and authenticate identity based on a risk profile of assets and users. This starts to explain why the two are complementary.
The top security resilience outcomes
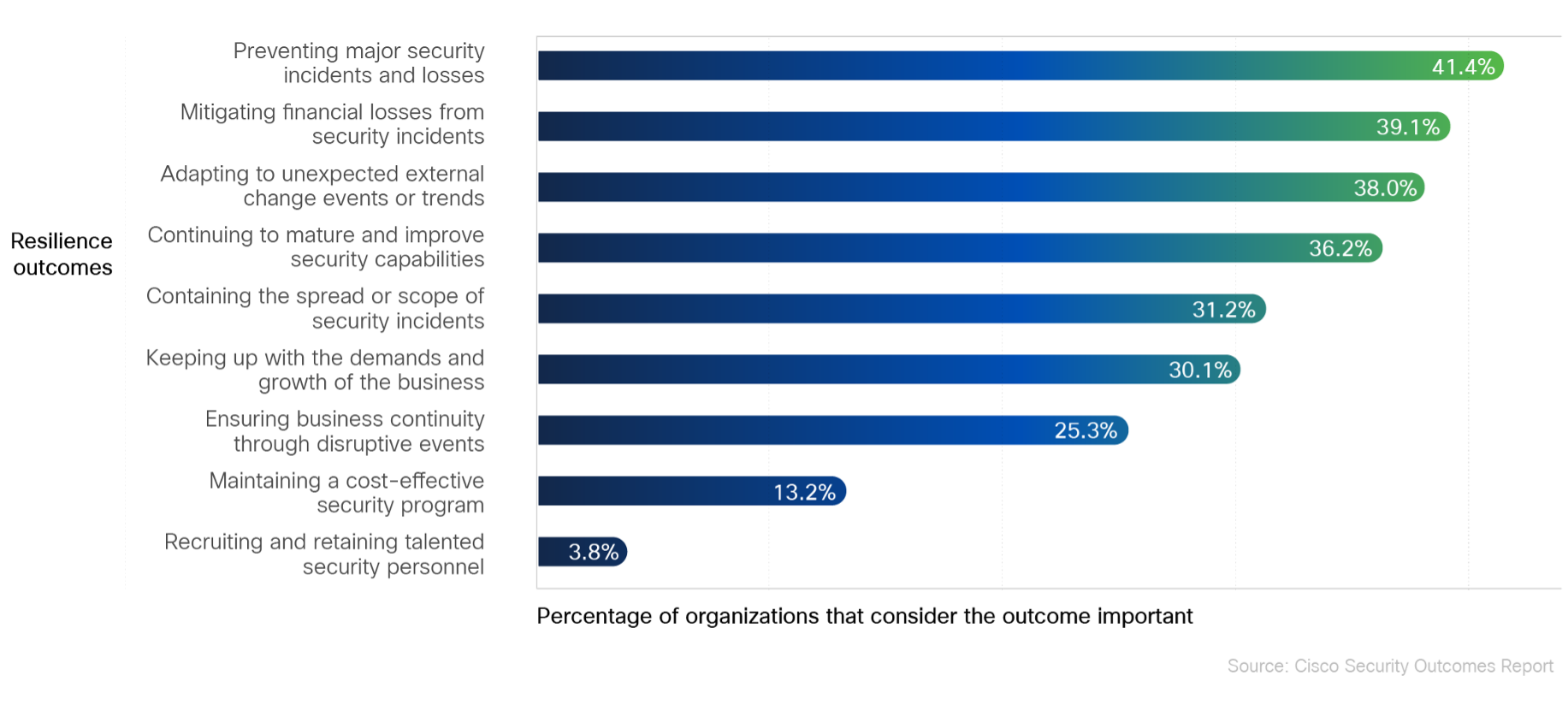
The Security Outcomes Report summarizes the results of a survey of more than 4,700 security professionals. Among the insights that emerge are nine security resilience outcomes they consider most important. The top three outcomes for resilience are prevention, mitigation and adaptation. In other words, they prioritize first the ability to avoid an incident by having the right controls in place, then the ability to reduce and reverse the overall impact when an incident occurs, and then the ability to pivot rapidly without being bound by too rigid a set of systems. Zero trust will support these outcomes.
Preventing, or reducing the likelihood of a cybersecurity incident, is an obvious first step and no surprise as the most important outcome. Pursuing programs that identify users and monitor the health of devices is a crucial a preventative step. In fact, simply ensuring that multifactor authentication (MFA) is ubiquitous across the organization can bring an 11% improvement in security resilience.
When incidents occur, security teams will need a clear picture of the incident they are having to manage. This will help in them respond quickly, with a proactive determination of recovery requirements. Previous studies show that once a team achieves 80% coverage of critical systems, the ability to maintain continuity increases measurably. This knowledge will also help teams develop more focused incident response processes. A mature zero trust environment has also been found to almost double a team’s ability to streamline these processes when compared to a limited zero trust implementation.
Communication is key
When talking to CISOs about successful implementation programs, communication within the business emerges as a recurring theme. Security teams must inform and guide users through the phases of zero trust implementation, while emphasizing the benefits to them. When users are aware of their responsibility to keep the organization secure, they take a participatory role in an important aspect of the business. So, when an incident occurs, they can support the company’s response. This increases resilience. Research has shown that a mature program will more than double the effect of efforts to improve the security culture. Additionally, the same communication channels established to spread the word of zero trust now can be called upon when an incident requires immediate action.
Mature implementations have also been seen to help increase cost effectiveness and reduce unplanned work. This releases more resource to cope with the unexpected – another important driver of resilience surfaced in Volume 3 of the Security Outcomes Report. Having more efficient resources enables the security function to reallocate teams when needed. Reviewing and updating resource processes and procedures, along with all other important processes, is a vital part of any of any change initiative. Mature zero trust environments reflect this commitment continuous assessment and improvement.
Adapt and innovate
Inherent in organizational resilience is the ability to adapt and innovate. The corporate landscape is littered with examples of those who failed to do those two things. A zero trust environment enables organizations to lower their risk of incidents while adapting their security posture to fit the ongoing changes of the business. Think of developing new partners, supporting new products remotely, securing a changing supply chain. The basic tenets of MFA – including continuous validation, segmentation and automation – sets a foundation that accommodates those changes without compromising security. The view that security makes change difficult is becoming obsolete. With zero trust and other keys to achieving security resilience, security now is a partner in business change. And for those CISOs who fear even starting this journey, understanding the benefits should help them take that first step.
Download the Security Outcomes Report, Vol. 3: Achieving Security Resilience today.
Learn more about cybersecurity research and security resilience:
- Join experts on January 18 as they dive deep into 7 success factors for achieving cybersecurity resilience
- Explore other blogs like this on security resilience
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels






This is solid fresh guidance for CISOs and security teams of every size. Nice work Cisco!