No, ransomware attacks are not random. From extortion to data breaches, ransomware is always evolving, and is becoming very lucrative with ransomware-as-a-service kit making it easier to target organizations. The days of just a single bad actor searching for vulnerabilities in your security stack are over. Security Operations Centers (SOCs) and the security analyst community are dealing with a sophisticated global network of adversaries who can do irreversible damage. The conversation must shift from how we can prevent a breach to how do we prepare for the inevitable breach.
What happened
Recently I found out that the small private college I attended right out of high school closed their doors permanently, falling victim to a targeted ransomware attack. This institution not only provided an education but also contributed to the local economy in this rural town for over 150 years.
The cyberattack occurred during the pandemic when most educational institutions had suddenly shifted to remote learning. Adversaries knew that the shift to remote learning would expose the college’s lack of acceptable tools for monitoring and managing applications, frequently from unsecure locations.
Unfortunately, the hackers were able to halt all admission activities, locked the administrators out from accessing critical data pertaining to the upcoming school year and ultimately, forced the school to close their doors – even after they paid the hackers the ransom.
And this is not an isolated case – Comparitech published a story ‘Ransomware attacks on US schools and colleges cost $3.56bn in 2021’ and outlined how threat actors have evolved with their ransomware attacks on schools and colleges. This is particularly concerning as many of these institutions do not have the skillsets or resources to protect their students or organization from these attacks. Below you can review their findings from a study done between 2018 – 2022:
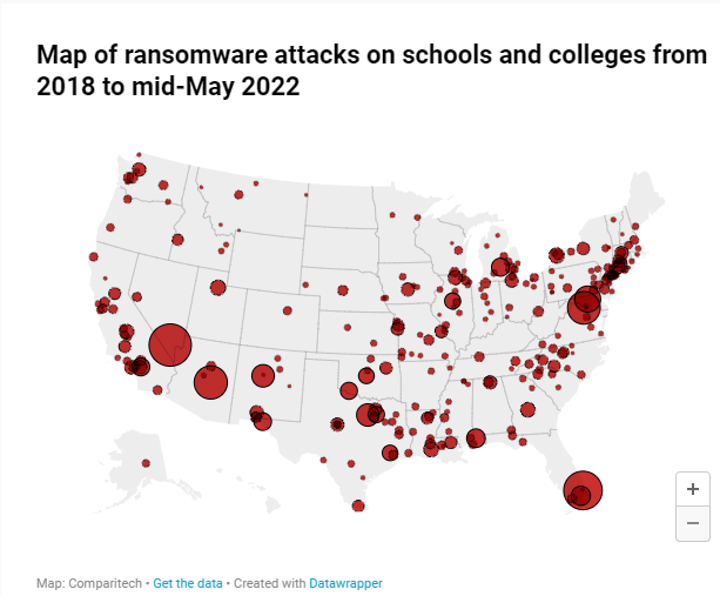
Key findings
In 2021:
- 67 individual ransomware attacks on schools and colleges–a 19 percent decrease from 2020 (83)
- 954 separate schools and colleges were potentially affected–a 46 percent decrease from 2020 (1,753)
- 950,129 individual students could have been impacted–a 31 percent decrease from 2020
- Ransomware amounts varied from $100,000 to a whopping $40 million
- Downtime varied from minimal disruption (thanks to frequent data backups) to months upon months of recovery time
- On average, schools lose over four days to downtime and spend almost a month (30 days) recovering from the attack
- Hackers demanded up to $52.3 million across just six attacks and received payment in two out of 18 cases where the school/college disclosed whether or not it paid the ransom (however, they are more likely to disclose that they haven’t paid the ransom than if they have). In one case, hackers received $547,000
- The overall cost of these attacks is estimated at around $3.56 billion
Protect yourself from Cyber criminals
Just having a firewall alone will not stop all of the attacks, it’s just a matter of time before you experience a breach. Once the breach happens, you need a security system that will quickly detect and remediate the threat .
Resiliency must be a critical outcome for any security solution and Cisco Secure Endpoint is built to stop hackers at the point of entry. Our cloud native solution allows your security operations team to quickly detect and respond to threats minutes after a breach occurs.
Securing vectors threat actors have to your network has to be the goal
Small to medium size businesses, hospitals, and educational institutions internal network will rely on cyber insurance in-lieu of a fully staffed, skilled cyber-security team. In today’s climate of ever-increasing sophisticated cyber threats this won’t cut it. You will need an agent that quickly detects, responds, and has visibility across your different security solutions.
With Cisco Secure Endpoint Pro we are equipped to assist with the responsibility of monitoring your endpoints for cyberattacks. With 24/7/365 monitoring capabilities, our SOC will quickly detect and remediate any threats that targets your organization. Secure endpoint pro provides flexibility and the option of letting our SOC team do the heavy lifting while you focus on your core business.
Tangible outcomes provided by Secure Endpoint and Secure Endpoint Pro:
- Stop threats before you’re compromised
- Remediate faster and more completely
- Maximize your security operations – Focus on the most important threats and gain always on security with managed EDR
Limit the amount of time threat actors have to your network
An effective managed endpoint detection and response solution frees up time for your SOC team along with accelerating detection and response time. Cisco Secure Endpoint can reduce incident response time by as much as 97%, which limits the damage threat actors can cause after you have been breached.
Cisco Security has launched a solution geared towards protecting your school’s network by blocking malicious threats before they enter the endpoint and compromising your data. The secure endpoint agent is deployed, sits on the school endpoint freeing up time from a stretched thin IT department.
Don’t know where to get started? Check out how our EDR solution got you covered below and how to contact us to learn more.
Sign up for a Secure Endpoint 30-day free trial
and test drive a demo account
Did You Know: Cisco has a grant and funding option available for schools?
Interested? Reach out to grantsquestions@cisco.com to learn about public funding options available in your state.
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels






“The NIST frameworks were designed as flexible, voluntary frameworks. The fact that they are flexible makes it relatively easy to implement them in conjunction with ISO 27001.
This is largely due to both standards having a number of common principles, including; requiring senior management support, a continual improvement process, and a risk-based approach.”
https://www.6clicks.com/blog/how-do-iso-27001-and-nist-csf-complement-each-other