The intriguing realm of the metaverse should not make us overlook its cybersecurity hazards.
Metaverse adoption has been steadily increasing globally, with various adoption use cases such as virtual weddings, auctions, and the establishment of government offices and law enforcement agencies. Prominent organizations such as INTERPOL and others are investing considerable time and resources researching space, underscoring the importance of the metaverse. While the growth of the metaverse has been accelerating, its full potential has not yet been realized due to the slow development of computing systems and accessories necessary for users to fully immerse themselves in virtual environments, which is gradually improving with the production of augmented reality and visual reality solutions such as HoloLens, Valve Index and Haptx Gloves.
As virtual reality tools and hardware evolve, enabling deeper immersion in virtual environments, we anticipate a broader embrace and utilization of the metaverse.
Significant concerns have risen regarding criminal activity within this virtual realm. The World Economic Forum, INTERPOL and EUROPOL have highlighted the fact that criminals have already begun exploiting the metaverse. However, due to the early stage of the metaverse’s development, forensic science has not yet caught up, lacking practical methodologies and tools for analyzing adversarial activity within this realm.

Unlike conventional forensic investigations that primarily rely on physical evidence, investigations within the metaverse revolve entirely around digital and virtual evidence. This includes aspects such as user interactions, transactions and behaviors occurring within the virtual world. Complicating matters further, metaverse environments are characterized by decentralization and interoperability across diverse virtual landscapes. There are unique challenges related to the ownership and origin of digital assets as users can join metaverse platforms with their anonymous wallets and interact with them pseudonymously without revealing their real identity. Such analysis requires advanced blockchain analytics capabilities and large attribution databases linking wallets and addresses to actual users and treat actors. As a result, this new digital realm necessitates the development of innovative methodologies and tools designed for tracking and analyzing digital footprints, which play a crucial role in addressing virtual crime and ensuring security and virtual safety in the metaverse.
The security community needs a practical, real-world forensic framework model and a close examination of the intricacies involved in metaverse forensics.

Case studies
User activity in the metaverse is immersed in digital environments where interactions and transactions are exclusively digital, encompassing different moving parts such as chatting, user movements, item exchanges, blockchain backend operations, non-fungible tokens (NFT), and more. The diverse and multifaceted nature of these environments presents adversaries with numerous opportunities for malicious activities such as virtual theft, harassment, fraud, and virtual violence, which will only be exemplified with the development of more realistic metaverse environments (Figure 1). The distinct aspect of these crimes is that they often lack any physical real-world connection, presenting unique challenges in investigating and understanding the underlying tactics, techniques and procedures leveraged by adversaries.
Occurrences of threats in metaverse platforms already exist, with the most notable to date involving the British police launching its first ever investigation into a virtual sexual harassment in the metaverse, stating that although there are no physical injuries, there is an emotional and psychological impact on the victim. An extensive list of the potential harms in and through the metaverse can be found in INTERPOL’s metaverse report.

Here are two other theoretical scenarios that exemplify the importance of metaverse forensics, and the need to distinguish their differences from contemporary forensics.
Scenario 1 – Robbery from an avatar (a metaverse gift): In the metaverse, a character approaches another avatar to present virtual shoes as a gift. The avatar accepts the gift, but a few hours later discovers that all digital assets associated with their metaverse account and digital wallet have disappeared. This incident involving stealing digital assets occurred because the seemingly innocent gift of virtual shoes was, in fact, a malicious NFT embedded with adversarial code that facilitated the theft of the avatar’s digital assets.
Scenario 2 – A metaverse conference: A user attends a cybersecurity conference in the metaverse, not knowing it is organized by cybercriminals. Their aim is to lure high-value stakeholders from the industry to steal their data and digital assets. This event takes place in a well-known conference hall in the metaverse. The registration form for the event includes a smart contract designed to extract personal information from all attendees. Additionally, it embeds a time-triggered malicious code set to steal digital assets from each avatar at random intervals after the conference ends. Investigating such incidents requires a comprehensive multi-dimensional analysis that encompasses marketplaces, metaverse bridges, blockchain activities, individual user behavior in the metaverse, data logs of the conference hall and the platform hosting the event, as well as data from any supporting hardware.
Challenges for forensic investigators and law enforcement
Several challenges exist for metaverse investigators. And as the metaverse evolves, additional challenges are expected to surface. Here are some potential issues law enforcement and cybersecurity investigators may run into.
Decentralization and jurisdictions: The decentralized nature of many metaverse platforms can lead to jurisdictional complexities. Determining which laws apply and which legal authority has jurisdiction over a particular incident can be challenging, especially when the involved parties are spread across different countries. As such, it will be exponentially complex or even impossible in some cases for law enforcement to subpoena criminals or metaverse facilitators.
Anonymity and identity verification: Users in the metaverse often operate in an anonymous or pseudonymous manner with avatars with random nicknames, making it difficult to identify their real-world identities. This anonymity can be a significant hurdle in linking virtual actions to criminals. Only few options for unmasking adversarial activity exist, including tracing IP addresses and analyzing platform logs which can be a complex undertake when dealing with truly decentralized metaverse platforms, often leaving blockchain analytics as the only viable analysis methodology.
Complexity and interpolarity of virtual environments: The metaverse can contain a myriad virtual spaces, each with its own set of rules, protocols and types of interactions. Understanding the nuances of these environments is crucial for effective investigation. To compound on the complexity of virtual environments, many metaverse platforms are interconnected, and an investigation may need to span multiple platforms, each with its own set of data formats and access protocols.
Digital asset tracking: Tracking the movement of digital assets, such as cryptocurrencies or NFTs, across different platforms and wallets through blockchain transactions requires specialized knowledge and tools. Without such dedicated tools, tracing digital assets is impossible as such tools contain millions of walled address attributions, ensuring the effective tracing of funds and assets.
Lack of international standards: The absence of global standards for metaverse technology development allows for a wide variety of approaches by developers. This diversity significantly affects the investigation of metaverse platforms, as each requires unique methods, tools and approaches for forensic analysis. This situation makes forensic processes time-consuming and difficult to scale. Establishing international standards would aid forensic investigators in creating tools and methodologies that are applicable across various metaverse platforms, streamlining forensic examinations.
Blockchain immutability: The immutable nature of blockchain ensures that all recorded data remain unaltered, preserving evidence integrity. However, this same feature can also limit certain corrective actions, such as removing online leaks or inappropriate data and reversing transactions involving stolen funds or NFTs.
Correlation of diverse data sources: Data correlation plays a crucial role in investigations, aiming to merge various data types from disparate sources to provide a more comprehensive insight into an incident. Examples of that can be correlating the events of different systems or combining end-host data with associated network data or the correlation between different user accounts. In the context of the metaverse, the challenge lies in the sheer volume of data sources associated with metaverse technologies. This abundance makes data correlation a complex task, necessitating an in-depth understanding of diverse technologies supporting metaverse platforms and the ability to link disparate data sets meaningfully.
Lack of forensic automation: Investigators commonly use various automated tools in the initial stages of their forensic analysis to automate various pedantic operations. These tools are crucial to identify signs of compromise efficiently and accurately. Without these tools, the scope, efficiency, and depth of the analysis can be greatly impacted. Manual analysis requires more time and heightens the risk of overlooking critical signs of compromise or other malicious activities. The emerging and complex nature of metaverse environments currently lacks these tools, and there is no anticipation of their availability soon.
Metaverse investigation approach
The forensic approach for the metaverse is distinct from traditional approaches, which typically begin with investigations focusing on physical devices for telemetry extraction. Investigating the metaverse is a challenging task because it involves more than just examining various files across multiple systems. Instead, it requires the analysis of diverse systems within different environments and the correlation of such data to draw meaningful conclusions.
An example illustrating metaverse forensic complexities is, a rare digital painting, goes missing from a virtual museum. A forensic system should undertake a comprehensive investigation that includes reviewing security logs in the virtual museum, tracing blockchain transactions, and examining interactions within interconnected virtual worlds and marketplaces. The investigation should also analyze recent data from devices like haptic gloves and virtual reality goggles to confirm any malicious related user activities. The analysis of virtual logs or hardware is dependent on the logs recorded by providers or vendors and whether such logs are made available for analysis. If such information is not present, there is little that can be done in terms of forensic analysis.
In this example, if the metaverse platform and virtual museum did not maintain logs it would be impossible to verify the activities preceding the theft, including information about the adversary. If logs from haptic gloves or reality googles are also not present, the activities described by the user during the adversarial activity would have been impossible to verify. This leaves a forensic investigator unable to perform in-depth analysis apart from monitoring on-chain data and the transfer of the painting between the museum wallet and adversarial wallet addresses.
Metaverse platforms vary in their approach to logging and data capture, significantly influenced by the method through which users access these environments. There are primarily two access methods: through a web browser and via client-based software. Web browser-based access to metaverse platforms, like Roblox and Sandbox, requires users to navigate to the platform using a browser. In contrast, client-based platforms such as Decentraland necessitate downloading and installing a software application to enter the metaverse. This distinction has profound implications for forensic analysis. For browser-based platforms, analysis is generally limited to network-based approaches, such as capturing network traffic, which may only be feasible when the traffic is not encrypted. On the other hand, client-based platforms can provide a richer set of data for forensic scrutiny. The software client may generate additional log files that record user activities, which, alongside conventional forensic methods like analyzing the registry or Master File Table (MFT), can offer deeper insights into the application’s use and user interactions within the metaverse. Regardless of the access method, the potential for forensic analysis can be further expanded based on the types of logs and data recorded by the metaverse environment itself and made available by the provider. This means that within each metaverse platform, the scope and depth of forensic analysis can vary based on the specific logs kept by the environment, offering a range of analytical possibilities.
Forensic systems suited for metaverse environments should start their investigation in the digital realm and use physical devices for their supporting data. These forensic systems must connect to user avatars, their accounts, and related data to facilitate initial triage and investigation. Forensic solutions for the metaverse should be capable of conducting triage, data collection, analysis and data enrichment, paralleling the requirements for examining current software and systems. The following three features would greatly benefit forensic investigators when analyzing the metaverse:
- Triage collection: Collection of forensic artefacts start within the metaverse environment or platform, extending to other supporting software and hardware devices enabling users to interface with the metaverse.
- Analysis: Processing the captured data to link relevant data and activity based on the reported incident aiming to identify anomalies and indicators of compromise (IOCs). Machine learning can be leveraged to automate the investigation by analyzing relevant telemetry based on the reported indicators of compromise or incident outcomes according to similar past incidences and the analysis and resolution provided by forensic analysts.
- Data enrichment: Based on the IOCs identified, forensic systems must be capable of searching diverse sources such as blockchains, metaverse platforms and other associated information to identify relevant data for added context.
Forensic systems for the metaverse should be able to directly interact with a user’s avatar (Figure 2), which may adopt a non-player character (NPC) for assistance. When activated, the NPC avatar should be able to engage with the user’s avatar, requesting access to the avatar’s data, the metaverse platform, and all associated software and hardware implicated in an incident. This includes the metaverse console, IoT devices, networking devices and blockchain addresses. To ensure enhanced privacy and security, NPC forensic analysts should only be able to access user data if they are only activated or requested by a user and should only obtain read-only access.
The forensic NPC avatar should meticulously record relevant logs and document any detected indicators of compromise (e.g., suspicious metaverse interactions) along with the observed impact (e.g., NFT or crypto token theft) and the estimated timeframe of the incident from the user’s avatar. Given the inherent complexity of metaverse environments, these forensic systems should possess the ability to operate on multiple layers to gather data, among others:
- Blockchain to analyze transactions and exchanges performed on-chain.
- Metaverse Bridges to analyze activities across linked metaverse environments.
- Metaverse Platforms, including different apps and digital assets in the metaverse.
- Networking, including connections related to the metaverse platform as well as supporting sensors and devices. Supporting devices (haptic gloves, body sensors, computational unit, etc.).
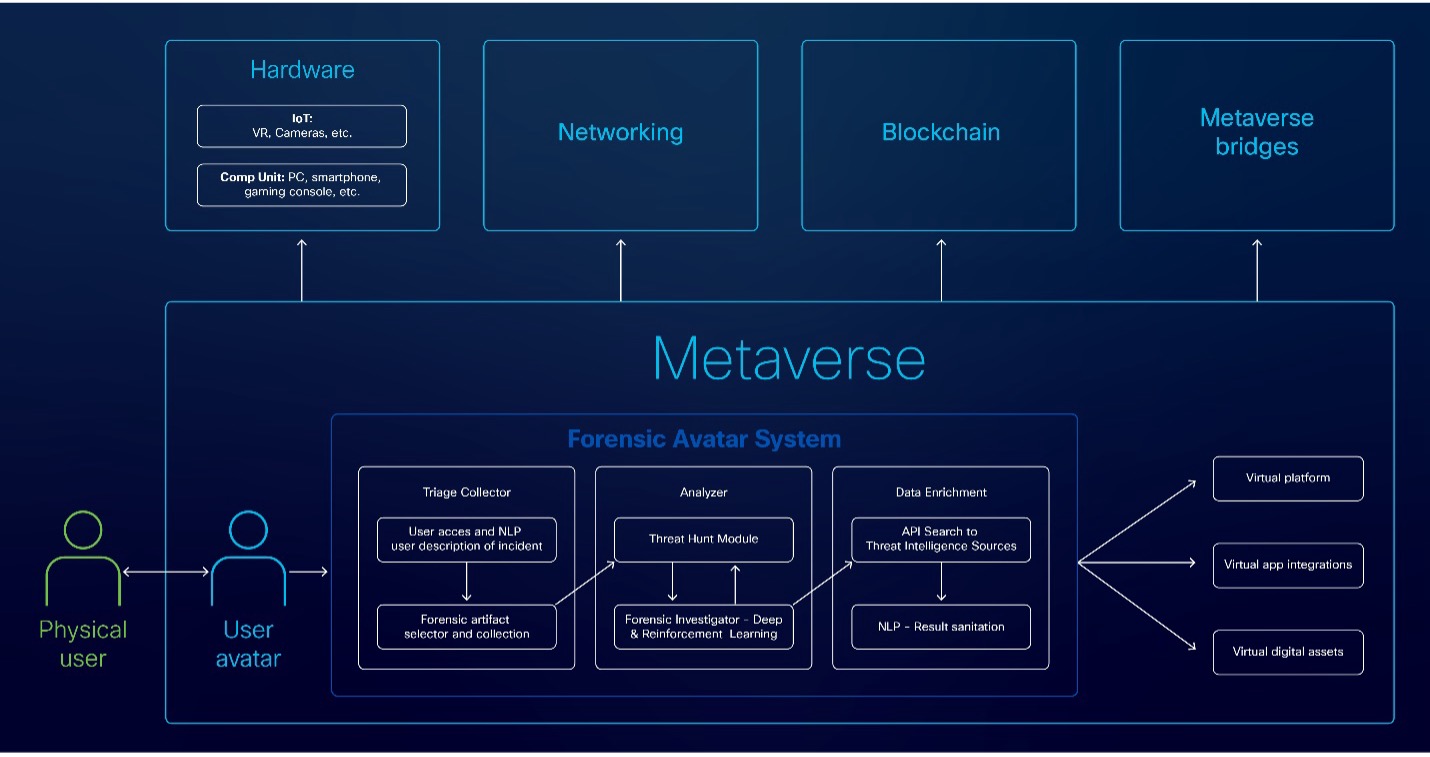
During analysis, malicious or anomalous activities should, optimally, be reported in an automated manner to guide the forensic analysts and speed up investigations. After analysis, any detected signs of compromise, such as cryptocurrency addresses, user activities, or files, should undergo data enrichment. This involves conducting searches across different data sources to find relevant information, which helps provide more detail and context for the analyst.
In the following sections of the blog, we provide a deeper view of how each of the three phases proposed operate, providing the data sources that can be leveraged for each, where applicable.
Triage and artefact collection
Forensic systems can analyze various threat types using multiple data sources. As the fields of forensics and the metaverse develop, the demand for new data sources will grow. It’s important to acknowledge that the available telemetry data can vary based on the platform and hardware in use. The absence of international standards and protocols for the metaverse compounds this complexity. With this in mind, we identify the following data sources as potential telemetry that should be logged to allow the effective analysis of metaverse environments. In addition to the telemetry presented below, forensic triage collection should be performed by capturing the memory and disk image from systems involved in an incident.
Authentication and access data:
- User login history, IP addresses, timestamps and successful/failed login attempts.
- Session tokens and authentication tokens used for access.
Third-party integration data:
- Data from third-party integrations or APIs used in the metaverse platform.
- Permissions and authorizations granted to third-party apps.
Error and debug logs:
- Logs of software errors, crashes or debugging information.
- Error messages, stack traces and core dumps.
Script and code data:
- Source code or scripts used within the virtual environment.
- Execution logs and debug information.
- Smart contracts in relevant blockchain wallets.
Marketplace, commerce data and blockchain:
- Records of virtual goods or services bought and sold on the platform’s marketplace.
- Payment information, such as credit card transactions or cryptocurrency payments.
User account and user behavior:
- Profile username, avatar image, account creation time, account status, blockchain address used to open the metaverse account.
- User interactions, friendships, groups, locations, and social networks, while preserving privacy.
- User activity logs, including participation in events and in-world gatherings.
User device forensics:
- User devices for the extraction of supporting data, such as device activity, configuration files, locally stored chat logs, images, etc.
- All ingoing and outgoing network activity reaching devices relevant to a metaverse incident.
Asset provenance data:
- Detailed asset provenance information with the complete history of ownership and modifications.
- Blockchain addresses and wallets, including a copy of their transaction history. Verification of the “from” address (creator or previous owner) and the “to” address (current owner) is required.
- If the asset is digital or represented as a token (e.g., an NFT), examine the smart contract that created it. Smart contracts contain rules and history about the asset.
- Ensure the asset is not a copy or fake by verifying that the smart contract and token ID are recognized by the creator or issuing authority.
System and platform configuration:
- Details of the platform’s architecture, configurations and version history.
Behavioral biometrics:
- Behavioral patterns of user interactions and in-game actions to help identify users based on unique behavior. Although such activity can be useful to identify adversaries in the case where very little is known for their activities, such information is not expected to be widely available.
Telemetry analysis
The goal of the telemetry analysis process is to detect unusual or potentially malicious behavior through a semi- or fully automated processing of data and logs, thereby aiding forensic experts and expediting the investigation process.
This can be accelerated by leveraging deep learning techniques to identify harmful patterns using a database of historically analyzed events. Additionally, incorporating reinforcement learning, refined by forensic experts, could enhance the system’s ability to offer better incident response suggestions. For effective training, these machine-learning algorithms would need access to a large repository of forensic strategies and actions taken by professionals in various investigative scenarios, including those spanning across different metaverse environments and artefacts. Utilizing this data allows the algorithms to match current incidents with similar past cases based on the user input provided.
Given the diverse range of threats and types of incidents, along with the emerging state of the metaverse and its insufficient logging features, devising a comprehensive forensic methodology that is universally applicable to all metaverse platforms or systems presents significant challenges. Should metaverse operators provide telemetry data, the analytical process can be simplified by focusing on artifacts that are most pertinent to a specific incident. Nonetheless, the presence of such artifacts in existing metaverse platforms cannot be assured. To overcome this issue and offer practical guidance, we suggest a hybrid forensic strategy that integrates traditional operating system forensics emphasizing Windows-based platforms due to their prevalent use for client-side metaverse platforms, along with specialized analyses that address the unique aspects of the metaverse and blockchain technologies. For better understanding, we categorize each analytical technique as per the divisions used in the triage and artifact collection section of this blog.
Authentication and access data
Metaverse platforms often store records of successful authentication attempts, including the dates, in local log files. If these logs are unavailable, analyzing DNS records and process executions associated with the metaverse platform can provide insights into when a user accessed it.
One approach to uncover such information involves examining browser records (e.g. Chrome) and the history of visited URLs to identify when a user visited and connected to a specific metaverse platform via a web browser. Additionally, routers may maintain by default traffic logs offering further insight into DNS activity.
For process-related investigation, resources like Amcache and Prefetch are valuable for determining the timing of executions for the metaverse platform client. These tools can help trace the usage patterns and activities associated with user interactions with the metaverse.
Third-party integration data
Acquiring such data can be challenging because these operations occur usually on the backend of servers, and logs related to this activity are typically not accessible to users. To obtain this information, which depends on the architecture and API usage of a metaverse platform, one could use network capture tools like Wireshark. This method allows users to monitor any API requests made while using a metaverse platform, and inspect the contents of these communications, provided they are not encrypted. This approach helps in understanding the interaction between the client and the server during the operation of metaverse platforms.
Error and debug logs
Metaverse platforms commonly record client and connectivity issues in local log files. When these logs are not accessible, one can analyze the Windows Application log to identify any errors issued by the application and any software problems that prevent it from either logging in or functioning properly. However, it is important to note that errors occurring specifically within the metaverse environment are not captured by Windows’ native logs, thus remaining invisible to analysts using these tools.
Script and code data
In certain environments, snippets of scripts and other code that serve various functionalities can be accessed through reverse engineering, allowing analysts to determine if a metaverse feature is functioning properly and safely. However, it’s important to note that reverse engineering software may be illegal and is generally advised against.
Despite these limitations in directly analyzing metaverse code, it is still feasible to examine publicly available smart contract code. This code governs on-chain transactions and facilitates exchanges of value between players in metaverse environments. To analyze the smart contract associated with a specific metaverse, one must first identify the blockchain it utilizes. Then, by finding the smart contract’s address, one can inspect its code using a blockchain explorer. For instance, to review the smart contract of UNI (a decentralized exchange) which operates on the Ethereum blockchain, one would use an Ethereum blockchain explorer to locate and examine the contract’s code at the Ethereum address (0x1f9840a85d5aF5bf1D1762F925BDADdC4201F984) used by UNI.
Marketplace, commerce data and blockchain
Transaction records of virtual goods or services exchanged on a metaverse platform can be tracked by examining a user’s account to review the NFTs and other items they possess. Additionally, by conducting on-chain transaction analysis, one can retrieve a complete history of item ownership, including details of items or NFTs bought and sold by users. Thanks to the transparency of public blockchains, this process is straightforward. It only requires the wallet address used by the user to access the metaverse platform. This address can be searched in the relevant blockchain explorer to analyze the user’s historical transactions and items purchased or sold.
User accounts and behavior
Currently, the logging and analytics of user behavior within metaverse environments are largely undeveloped. Basic information like profile usernames and avatar images are stored locally in the metaverse client’s directory. More detailed information about user interactions, friendships, groups, and visited locations can be retrieved from a user’s account, provided the data has not been deleted by the user. Analyzing a user’s social networks may offer deeper insights into their participation in metaverse events and related in-world gatherings.
User device forensics
Various devices enable interaction with the metaverse, including VR headsets, smartphones, gaming consoles and haptic gloves. The extent of data logging varies by device. For example, VR headsets may record details such as connected social networks, usernames, profile pictures and chat logs. It is essential to analyze the specific vendor and device to determine the availability of such logs. As the technology landscape evolves, it is anticipated that more vendors and devices will emerge, further complicating the environment. This dynamic nature will necessitate more sophisticated tools and greater expertise for effective forensic analysis in the future.
Asset provenance data
Detailed information about the provenance of assets in the metaverse, including the complete history of ownership and modifications, can be obtained through on-chain analysis. This process involves examining transactions between blockchain addresses of interest, the non-fungible tokens (NFTs) and other tokens they possess, and their interactions with smart contracts. Because public blockchains are immutable — meaning that once data is recorded, it cannot be deleted or changed — it is relatively straightforward to track asset provenance. By searching for a known wallet address in the appropriate blockchain explorer, one can easily trace the history associated with that address.
When analyzing blockchain data for provenance, it is critical to verify that the addresses interacting with the target address are legitimate. This includes ensuring that entities like metaverse providers or NFT issuers are not misrepresented by posing as the official addresses. Verification can be achieved by visiting the official website of the token or metaverse provider to find and confirm their official blockchain addresses. This step is crucial to ensure that the address in question belongs to the entity it claims to represent. An illustrative case would be investigating the purchase of an expensive plot in the metaverse. Suppose an analysis of a user’s blockchain address reveals an NFT transaction from another address, which purportedly represents a plot identical to the one purchased. However, the source address sending the NFT is not the official one used by the metaverse provider for NFTs. If this discrepancy goes unchecked, it could obscure potential fraud or suspicious activities.
Another key factor in asset provenance is linking blockchain addresses to actual user identities. While blockchain technology typically provides pseudonymity, there are services that offer extensive databases capable of associating specific addresses with various entities and exchanges. This capability enhances an investigator’s ability to trace asset flows more effectively. For instance, WalletExplorer is a website that provides free services for attributing addresses on the Bitcoin network.
System and platform configuration
To effectively investigate a metaverse platform, it’s essential to gather detailed information about its system, architecture, and configuration. However, obtaining this information can be challenging as it is often limited. When available, key sources include official websites, developer documentation, user forums, and community pages. Additionally, valuable insights into the platform’s configuration can often be gleaned from debug and error logs, where these are accessible.
Behavioral biometrics
Behavioral patterns, such as user interactions and in-game actions, are key in identifying users based on their unique behaviors and detecting potential account hijacks. These behaviors can include movement and gesture recognition, voice recognition and the patterns of typing and communication. Additional metrics may involve how users interact with in-game items and other participants.
Currently, most systems used to interact with the metaverse do not extensively log such information, which limits the capacity for in-depth behavioral analysis. What is typically available for analysis includes communication patterns derived from chat logs and basic interaction patterns. These interactions are often analyzed through chats, the groups users join, events they attend, and on-chain analytics for transactions and engagements within the virtual space. This level of analysis, while helpful, only scratches the surface of what could potentially be achieved with more comprehensive behavioral data collection and analysis.
Data enrichment
Following analysis, it is crucial to correlate and analyze diverse data types from multiple sources, including blockchain transactions, IPFS storage, internet-of-things (IoT) devices and activities within the metaverse. Drawing from research, a forensic framework could use APIs from diverse data repositories to aggregate pertinent information. Such information can be retrieved from blockchain analytics vendors for the identification of malicious wallet addresses or traditional databases containing threat intelligence for malicious IP addresses and file hashes. The gathered data can then be processed through Named Entity Recognition (NER) to cleanse the data to extract relevant information and diminish data clutter in larger datasets, ensuring analysts receive concise and clear insights. Enriching threat intelligence demands considerably more effort beyond conventional practices, extending beyond mere checks of IPs, URLs, file hashes and online adversarial behavior. It also encompasses the analysis of blockchain transactions, provenance of digital assets, and the scrutiny of entities within the metaverse, such as casinos and conference venues, given that logs are available for analysis.
The insights gained from each case should be meticulously documented in public databases, outlining the tactics, techniques and procedure employed by adversaries within the metaverse. This documentation aids in refining the forensic capabilities of metaverse systems and provides forensic examinators intelligence for more effective and precise attributions. The selection of data sources for threat intelligence augmentation can be tailored based on investigative needs and emerging developments in the field. While it’s crucial to continue employing conventional threat intelligence strategies to address more traditional and legacy aspects of investigations, for metaverse-specific inquiries, relevant data sources might include:
- The source code of blockchains or smart contracts (e.g., from GitHub).
- IPFS (Interplanetary File System) frameworks.
- Blockchain analytics tools.
- Social media and community monitoring for discussions and trends on social media.
Conclusion
Metaverse environments are built on different platforms, each with its own set of protocols, standards, and data formats. This heterogeneity complicates the process of collecting and analyzing digital evidence. Additionally, the dynamic and immersive nature of the metaverse, where interactions and transactions occur in real-time within three-dimensional spaces, adds another layer of complexity. Forensic investigators must navigate these virtual spaces, by first understanding the context of interactions, and then identify relevant data points for analysis, which can be a daunting task.
Looking forward, the development of metaverse forensics is likely to focus on the creation of standardized tools and protocols to make metaverse compatibility, interpolarity, and thus forensics, an easier task. Forensic tools should be able to efficiently navigate and extract data from various metaverse platforms. These tools must be capable of not only handling the current diversity of data formats and interaction types but also adaptable to future technologies. Additionally, there is an emphasis on developing collaborative frameworks that allow for cross-jurisdictional cooperation, as the metaverse transcends geographical boundaries.
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Security on social!
Cisco Security Social Channels





