As each day passes, wireless security becomes even more critical to the day-to-day operations of organizations. Several factors contribute to the growing need for reliable security. With the introduction of Wi-Fi 6, many organizations are shifting from a primarily wired infrastructure to one that focuses on worker mobility through wireless connectivity. While the CAPEX and OPEX savings are compelling, increasing wireless traffic provides a larger attack surface – and greater opportunity – for hackers.
The Challenges of Wireless Security
As might be expected, there has been a significant increase in the number and complexity of cyberattacks. Distributed Denial of Service (DDoS) attacks alone are up 33% from last year, with a 37% increase in attack bandwidth.
One of the challenging aspects of wireless security is that communications can be captured passively. For example, when a client connects to an access point utilizing WPA-PSK, there is a 4-way handshake that takes place. Because the handshake occurs wirelessly, an attacker can passively listen in and capture this handshake. Due to the nature of wireless communications, there is no way to detect or prevent passive capture.
The next stage for the attacker is to use offline resources to attempt to brute force or wordlist attack the handshake to determine the passphrase. The attacker can then use this passphrase to de-authenticate the original client and connect with the access point in its place.
With advanced authentication mechanisms like WPA2 or WPA3 using 802.1x, commonly used in enterprise networks, passive listening will not allow an attacker to impact the network. But attackers are also advancing their methods and tools. For example, a new collection of recently discovered vulnerabilities called FragAttacks impacts all the Wi-Fi protocols from WEP to WPA3, in turn putting every wireless-enabled device at risk.
Advanced Security for Advanced Threats
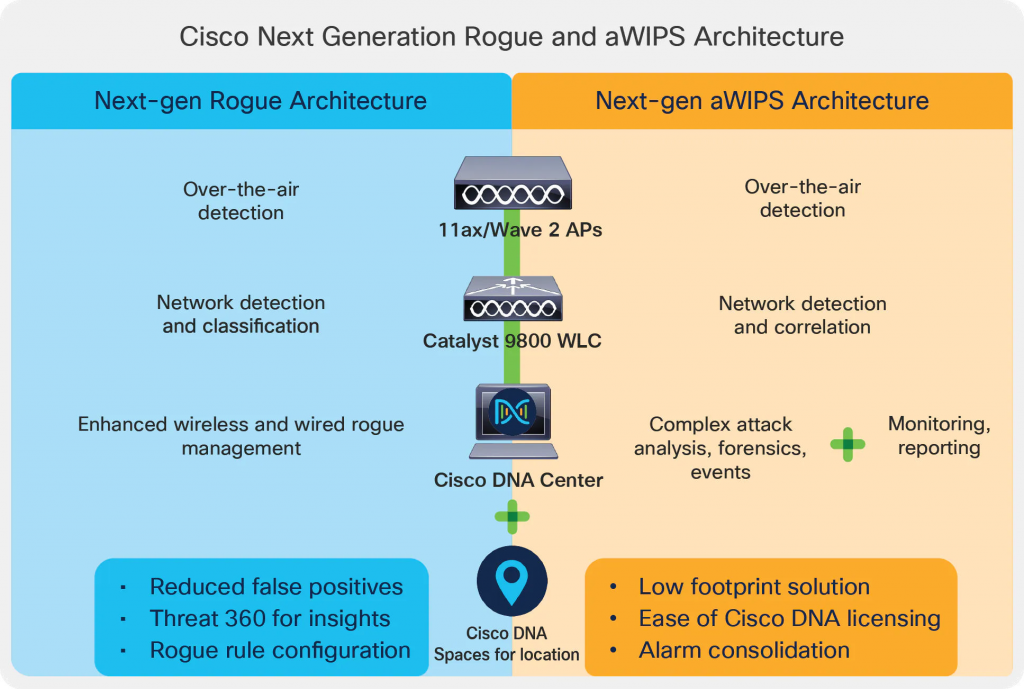
Cisco’s Advanced Wireless Intrusion Prevention System (aWIPS) and Rogue Management is a fully infrastructure-integrated solution that constantly monitors radio spectrum to detect, analyze, and thwart attacks. By incorporating signature-based techniques, traffic analysis, and anomaly detection, the aWIPS and Rogue Management solution is able to provide an intuitive Wi-Fi threat detection and prevention system designed to solve the critical security needs of modern networks. Together, Cisco’s aWIPS and Rogue Management provides security against a plethora of attacks like DoS attacks, management frame attacks, tool-based attacks, and more (see Figure 1).
While it is not possible to detect or prevent the passive capture of a handshake, the system is able to detect when an attacker tries to use a passphrase to de-authenticate an already connected client. At this point, aWIPS identifies the de-authentication attack and creates an alert so IT and the network can take action. For example, the Cisco Identity Services Engine (ISE) could apply policies for downgrading the trust score of the device launching the de-authentication attack to prevent access to the network and minimize its impact on operations. Similarly, Cisco’s Rogue management solution can detect rogues and AP impersonations, including the latest attacks like FragAttacks, right out of the box, without requiring any extra components.
Independent PEN Testing and Certification by Synopsys
The wireless team at Cisco has extensive experience understanding, identifying, and preventing wireless attacks. Our security solutions are tested to the latest threat standards. However, we have not relied solely on our own internal testing to verify that aWIPS and Rogue Management provide best-in-class wireless security.
Recently we engaged Synopsys to perform a wireless network penetration test to assess the functionality of aWIPS and Rogue Management. The test system consisted of Cisco C9130 and Cisco C9120 access points connected to a Cisco Catalyst 9800 Wireless LAN controller.
Synopsys assessed how the aWIPS and Rogue Management system identified common attack vectors over a three-week period. The test used a timeboxed approach of passive reconnaissance, active exploitation, and targeted manual penetration. The test assessed how the Rogue and aWIPS systems identified a wide range of attacks, including:
- WPA2/WPA3 attacks
- De-authentication attacks
- AP spoofing attacks
- Authentication attacks
Among its findings, Synopsys verified that Cisco’s Rogue Management was successful at preventing other access points from operating in the vicinity of the access points under test. This was achieved reliably by sending de-auth packets to the other access points’ clients and effectively preventing multiple access points and multiple clients from communicating simultaneously.
Synopsys also showed that Cisco’s aWIPS technology triggered an alert whenever a de-auth packet was sent against an aWIPS-enabled access point by another station (i.e., an unauthenticated client). Again, the passive nature of these attacks makes it impossible to prevent them. However, aWIPS successfully identified attacks so that risks to the network would not pass unnoticed.
Securing the Future
The shift to an increasingly mobile workforce continues to increase the complexity – and the necessity – of keeping the network secure. To keep peace of mind now and into the future, organizations need a security solution they have confidence in.
Learn more about how Cisco’s aWIPS and Rogue Management solution can protect Wi-Fi and wireless security for your organization. For a comprehensive demo, reach out to your Cisco sales representative.
Check out our Intent-Based Networking video channel.





