In the event of a cyberattack, are industrial organizations prepared to defend their operational technology (OT) and industrial control system (ICS) environments? Cisco set out to answer this question in a survey conducted together with Gartner Peer Insights and Takepoint Research in Q3CY22. The audience for the survey involved IT, OT, engineering, and InfoSec professionals across the globe.
Results showed that 77 percent of industrial organizations are still in the beginning stages of their OT security journeys. And none of the participants have fully secured their OT/ICS environments yet. This fact is worrying, considering the post-pandemic world in which we find ourselves.
Much has changed over the last three years. The pandemic has significantly accelerated the digital transformation of OT, which has led to most—if not all—of organizations’ critical operations to be integrated with digital technologies. In turn, cyberattacks such as those suffered by Colonial Pipeline, Oldsmar Water, and JBS in 2021 have become more prevalent as bad actors focus on the vulnerabilities of OT/ICS networks.
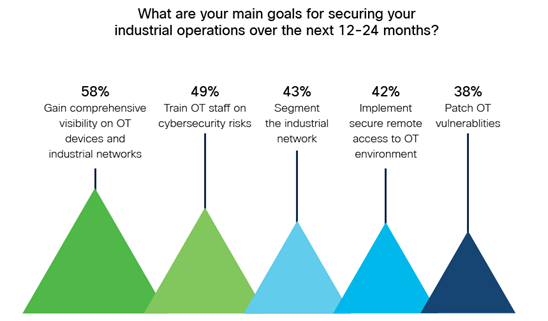
Our conversations with C-suite executives reveal that most organizations recognize that they aren’t prepared for a cyberattack and that many are just starting to prioritize OT security. Our survey reveals that the main goal for 58 percent of respondents is to gain comprehensive visibility on OT devices and industrial networks.
However, a stunning 74 percent say that the main obstacle to securing OT at scale is the cost and complexity of building an out-of-band Switched Port Analyzer (SPAN) network or deploying the network TAPs required to gain such visibility. But there is an alternative way to collect this data and build comprehensive visibility into the industrial network.
Cisco Cyber Vision embeds visibility features into network equipment, eliminating the need for sourcing, deploying, and managing dedicated security appliances or investing in costly out-of-band collection networks. This architecture provides unmatched visibility as passive discovery is achieved at every layer of the industrial network and active discovery requests are not blocked by NAT or firewall boundaries.
Our survey highlights other interesting facts, such as the critical need to implement secure remote access solutions into the industrial network and the need to control shadow IT practices in industrial networks now that operations teams are using more cloud and industrial IoT solutions. For more insights, see the survey results in this infographic.
For a deeper analysis of these survey findings, download our survey report that covers all the questions we asked our panel of professionals. The report also explains how to avoid some of the obstacles that OT security specialists face during deployment.
To learn more about how you can secure your IoT/OT infrastructure, visit our IoT Security page or contact us.
To get the latest industry news on IoT Security delivered straight to your inbox, subscribe to the Cisco IoT Security Newsletter.





