It seems like these days, you can’t read the news without seeing something about a cyberattack or data breach. While the digital economy and the Internet of Everything (IoE) are creating huge opportunities for value creation in both the public and private sectors, they also create huge opportunities for security breaches. With an expanded attack surface created by the IoE, cybercriminals look to take advantage of the influx of new devices and increasing network complexity. While a large cyberattack on a private company might be painful financially, a hack on some of our nation’s defense agencies could hurt much more.
The Department of Defense (DoD) is a high-priority target for hackers of all types, but especially for advanced malware creators who are seeking to steal intellectual property, capabilities and strategies from the U.S. government. These threats aren’t only isolated incidents from hacktivist groups; they often come from other advanced nation-states. The protection of military information and network assets is a part of national security and the DoD needs the tools to protect itself from cyberattacks.
One way the DoD and other agencies are looking to better protect their networks is by using advanced malware protection (AMP) tools. AMP helps detect “bad” files as they move across a sensor and flags the files for removal so that they don’t corrupt the rest of the network. Cisco’s AMP services are industry-leading; it was named a leader in Gartner Magic Quadrants for Intrusion Prevention Systems in 2014 and improved its position in 2015. It was also tested during NSS Labs’ rigorous next-generation firewall testing and received the highest effectiveness rating possible.

Cisco AMP is unique from its competitors in that it can place sensors throughout the network. Unlike most companies’ sensors, which must be attached to the firewall, Cisco’s sensors are compatible with a large variety of devices and platforms, such as switches, virtual machines and the cloud. By allowing for sensors in other places in the network, Cisco AMP casts a wider and finer net to catch malware.
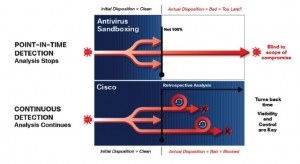
Additionally, Cisco AMP tracks files throughout the whole network. For most advanced malware systems, a file is only flagged as good or bad when it crosses a sensor. But with Cisco AMP, the file is tracked throughout and continually evaluated. That means if a file was initially tagged as good but more information appears, Cisco AMP can detect that anywhere in the network, flag it, and have the file removed. Continuously monitoring files enables security managers to get rid of corrupted files rapidly – which means the network can recover more quickly as well.
Another way that Cisco AMP sets itself apart from other security options is through its ability to trace a file’s path and remove other files it has potentially corrupted. The corrupted file is patient zero, but CiscoAMP can find every other patient it touched to ensure the threat is completed eradicated.
As DoD networks become increasingly complex, with more devices requiring access from remote areas, the capabilities Cisco AMP solutions provide will be even more important to ensure these critical networks are secure. No matter how it is utilized, Cisco AMP can help the Department of Defense and other public sector agencies defend their sensitive information from cyberattacks. Click here to learn more about Cisco AMP solutions.





