Last update: 6.21.2018
Save this post! New videos will continue to be added [ranked: newest to oldest]
Cisco Tetration offers holistic workload protection for multicloud data centers by enabling a zero-trust model using segmentation. This approach allows you to identify security incidents faster, contain lateral movement and reduce your attack surface. Its infrastructure-agnostic approach supports both on-premises and public cloud workloads.
What’s more, it’s rich ecosystem of partners brings you flexibility and choice to help you leverage a full-fledged open APIs, publish-subscribe Kafka messaging system, and ability to run custom apps .
One of the partnering solutions is the perfect match for your data center network analytics needs. Check them out!
First of all…
High level conceptual videos: lightboard series
If you need to take a step back and understand how you can achieve better network security through analytics, watch these Cisco Tetration lightboard videos. But if not, hey buddy, just jump straight into the demos below!
Demos

Cisco Tetration Overview (5:28)
Cisco Tetration delivers consistent, automated policy enforcement enabling application segmentation across on-premise, private and public clouds. Using software and hardware sensors, Tetration provides a deep understanding of application dependencies and interactions, increasing reliability and simplifying zero-trust operations.

Demo: Cisco Tetration Automated Policy Recommendation and Simulation (2:16)
Learn how you can create a consistent whitelist policy model.
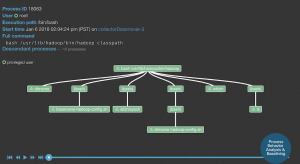
Demo: Cisco Tetration Dependency Mapping (2:10)
Learn how you can get a solid foundation for successful zero-trust operations, application migration and policy enforcement through deep understanding of application behavior.
Demo: Cisco Tetration Apps (1:08)
Cisco Tetration provides a variety of mechanisms to access information from the platform. You can write your own application on the platform using Python, Scala spark SQL.

Demo: Application Segmentation with Cisco Tetration (1:43)
See how you can automate policy enforcement enabling application segmentation across virtualized and bare-metal servers on-premise, private and public clouds.
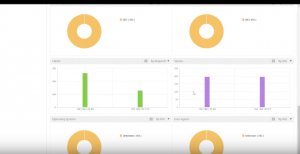
Demo: Cisco Tetration Self-Monitoring (1:39)
Cisco Tetration provides self-monitoring to cluster components that use big data technology and perform analytics including hardware and software sensors for easier cluster management.
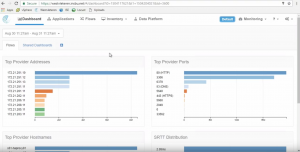
Demo: Cisco Tetration Dashboard Creation (1:20)
Cisco Tetration hardware and software sensors gather comprehensive analytics points of telemetry. This information is thoroughly analyzed and used to create rich information dashboards and critical data points in quick and easy to navigate charts and formats.
Demo: Cisco Tetration Policy Export (1:24)
Learn how you can easily deploy whitelist policy to any network controller using JSON, XML or YAML formats.

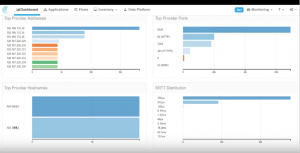
Demo: Cisco Tetration Visualization (2:14)
Search billions of records in less than a second. You can collect data center flow information in real time at line rate, and find details of known issues and aberrant behaviors that could go, otherwise, unnoticed.

Demo: Asset Tagging with Cisco Tetration (1:17)
Understand your business and data center with detailed business context about the service in the form of tags. You can search telemetry data and defined policies based on tags.

Demo: Cisco Tetration Compliance Capabilities (1:20)
See how you can get consistent network policy across different types of infrastructure – any workload, anywhere.
Cisco Tetration Overview: Hybrid Cloud Workload Protection (7:35)
Get holistic workload protection for multicloud data centers with zero-trust model using segmentation. This approach allows you to identify security incidents faster, contain lateral movement and reduce your attack surface. Its infrastructure-agnostic approach supports both on-premises and public cloud workloads.
Demo: Cisco Tetration Application Dependency Mapping (Deep Dive) 42:50
This video will go through a full mapping exercise: discovering the end points, understanding how they are communicating, building out the map, and lastly, enforce.

Demo: Cisco Tetration Data Sink, and Correlating SSH Logs and Flows (Deep Dive) 29:53
Bring your own data! Get information from other systems through Kafka and store them on Tetration, then leverage capabilities like data platform, user apps, and build you own application on top of them.
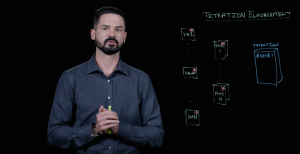 Cisco Tetration: Security Policy Enforcement (2:05) Cisco Tetration: Security Policy Enforcement (2:05)
Joe Onisick explains a recent feature of the Tetration Analytics appliance which is its ability to enforce. |
||
 Demo: Cisco Tetration Analytics and Tufin (6:52) Demo: Cisco Tetration Analytics and Tufin (6:52)
Learn how you can achieve Compliance and Policy Consistency with Cisco Tetration Analytics and Tufin |
||
Demo: Cisco Tetration and Infoblox (6:16)
This demo is about compliance and security with Cisco Tetration and Infoblox joint solution. |
||
 Demo: Cisco Tetration and Citrix (3:29) Demo: Cisco Tetration and Citrix (3:29)
Learn how you can achieve full data center visibility, analytics and security with this joint solution.
|
||
 Demo: Cisco Tetration and Turbonomic (6:44) Demo: Cisco Tetration and Turbonomic (6:44)
Learn how to achieve network-aware workload placement and IT optimization with Cisco Tetration Analytics and Turbonomic. |
 Demo: Cisco Tetration and Algosec (6:04) Demo: Cisco Tetration and Algosec (6:04)
Business driven security policy management with Cisco Tetration and Algosec. |
For more information, visit: www.cisco.com/go/tetration