Barcelona is a city of wonder, defined by the architectural genius of Antoni Gaudí. For the 100,000+ attendees of the Mobile World Congress 2026, these landmarks were must-see destinations. But where there is high interest, there is high opportunity for cybercriminals.
This was part of the backdrop for our mission in early March. As the most influential mobility and networking event on the planet, MWC 2026 was a whirlwind of innovation. At the center of this high-stakes environment, our team was on the ground, operating the Security and Network Operations Center (S/NOC) to ensure that the massive infrastructure powering the event remained bulletproof, and the attendees using its network were secure.

Our SOC was based on cutting-edge technologies provided by Cisco, consisting of the recently released AI ready ultra-high-end Secure Firewall 6160, our leading Security Service Edge solution Cisco Secure Access , our AI security solution Cisco AI Defense, our premium SIEM solution Splunk Enterprise Security, and our cloud-native detection and response solution Cisco XDR.
Secure Access
Due to the nature of the event, we were only using the DNS capabilities of Secure Access, also available in the Secure Access DNS Defense solution, with security applied at the DNS level. The DNS queries of the connected devices were forwarded to the Secure Access public resolvers where we block threats before a connection is established. All the security event logs were pushed directly to XDR, while Splunk ES was pulling all the anonymised logs, and AI Defense was collecting App Discovery logs for Generative AI applications to provide additional insights of the AI models used on the network of the event.
Splunk Platform

In the image above, you can see a custom dashboard we created on Splunk ES consuming all the logs it was receiving from the Firepower Threat Defense 6160 firewall, and the DNS requests sent to the Secure Access public resolvers. In this specific screenshot, we are showing the data for the last seven days from the afternoon of the last day of the event, the 5th of March (instead of the last 24 hours appearing at the titles of the graphs, which was what we were normally observing).
Please note that the network of the venue remains protected at the DNS level by Cisco Secure Access outside the event. As a result, there are DNS logs outside the dates of the MWC, as the network was actively used during the setup.
XDR
In the customised XDR dashboard below, you can see some high-level information extracted from the DNS traffic of the network. This includes the total number of DNS requests for the last 30 days, and the blocks for Malware, Command and Control, and Phishing for the same period.
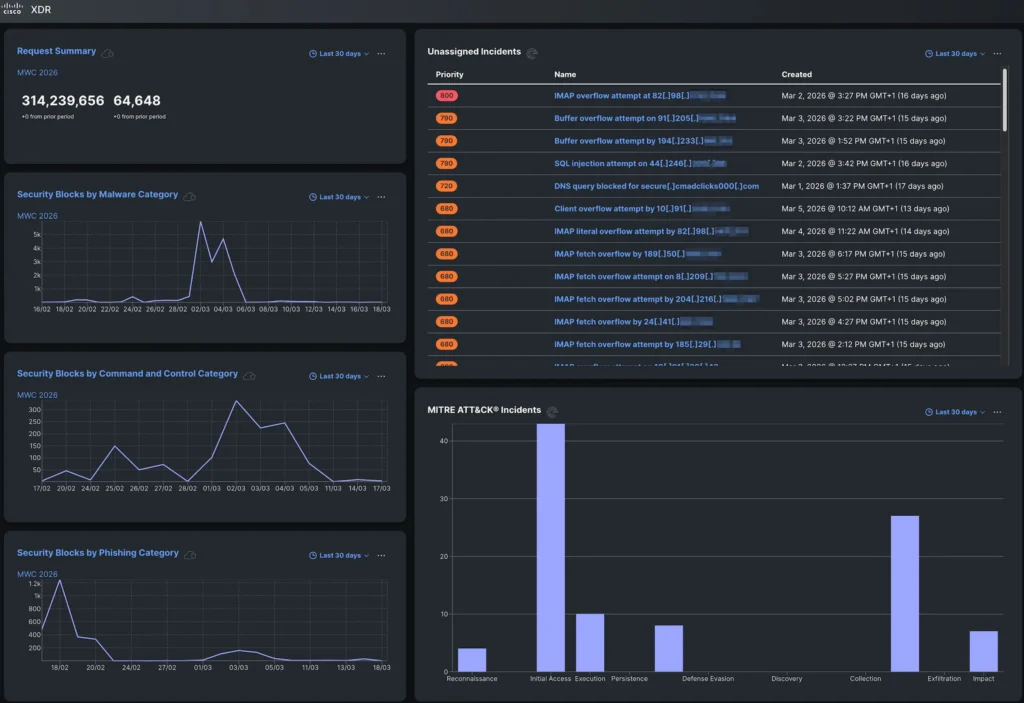
There are again events outside the dates of the MWC. It is worth noting that a phishing campaign appears to have taken place at the venue during a previous event in mid-February.
On the right-hand side, you can see incidents that were automatically created on XDR after correlating the DNS logs from Secure Access and the firewall logs from the FTD 6160, and MITRE ATT&CK Incidents.
AI Defense
While Generative AI is a powerful tool, it imposes significant risks that organisations need to be aware of and manage accordingly. In the image below, you can see an App Discovery report from AI Defense showing the AI applications discovered on the network of the venue. The Composite Risk Score occurs by combining Business Risk, Usage Risk, and Vendor Compliance to calculate a standardised measure of the risk they may imply.
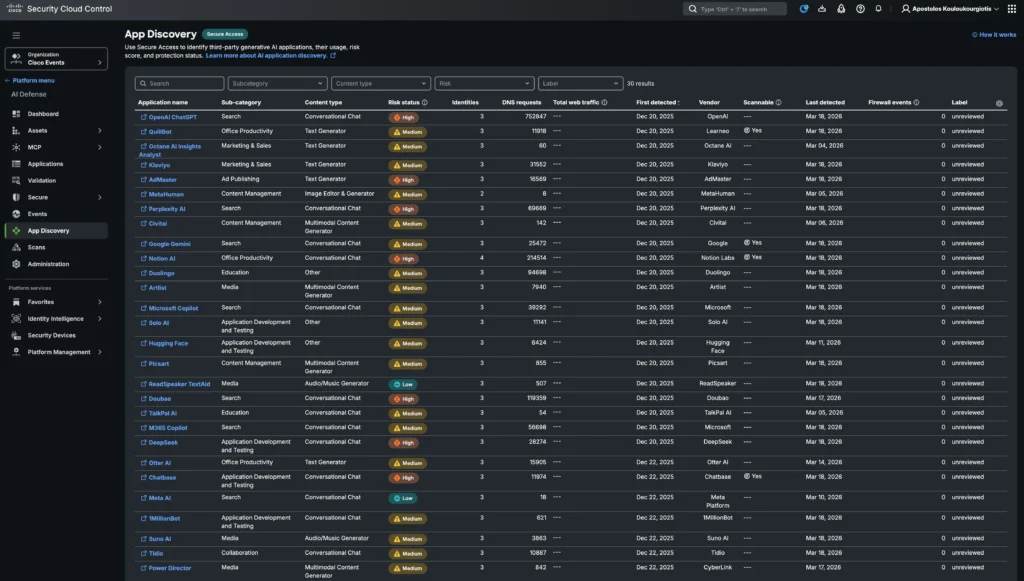
Access to these AI models can be managed with Secure Access to secure AI apart from just leveraging AI for security. In a non-anonymised environment where the traffic is routed through the Security Service Edge (SSE)’s cloud-hosted Secure Web Gateway, the applications can be scanned to enforce AI guardrails through the Secure Access DLP (data loss prevention) policy and control what data is sent to the AI applications, while tenant controls can also be applied.
When the guard is down
While attendees were busy planning their sightseeing outside the event, attackers were busy crafting traps. We observed a surge in sophisticated phishing campaigns targeting the very people attending the conference. Fraudsters stood up convincing, fake websites perfectly mimicking official ticket portals for the city’s top attractions, designed to harvest credit card details and drain accounts before the victims even reached the front doors of the breath-taking Basílica de la Sagrada Família in this example.
It was a stark reminder: even the most seasoned tech experts who spend their careers building defenses and hunting threats may leave a digital door unlatched when they step away from work. The same AI-powered vigilance we apply to global enterprise networks is just as critical in our personal digital lives. At MWC 2026, we were not just monitoring the network; we were witnessing a masterclass in how quickly a moment of leisure can turn into fraud.
During the event, Secure Access blocked access to one of those phishing domains.
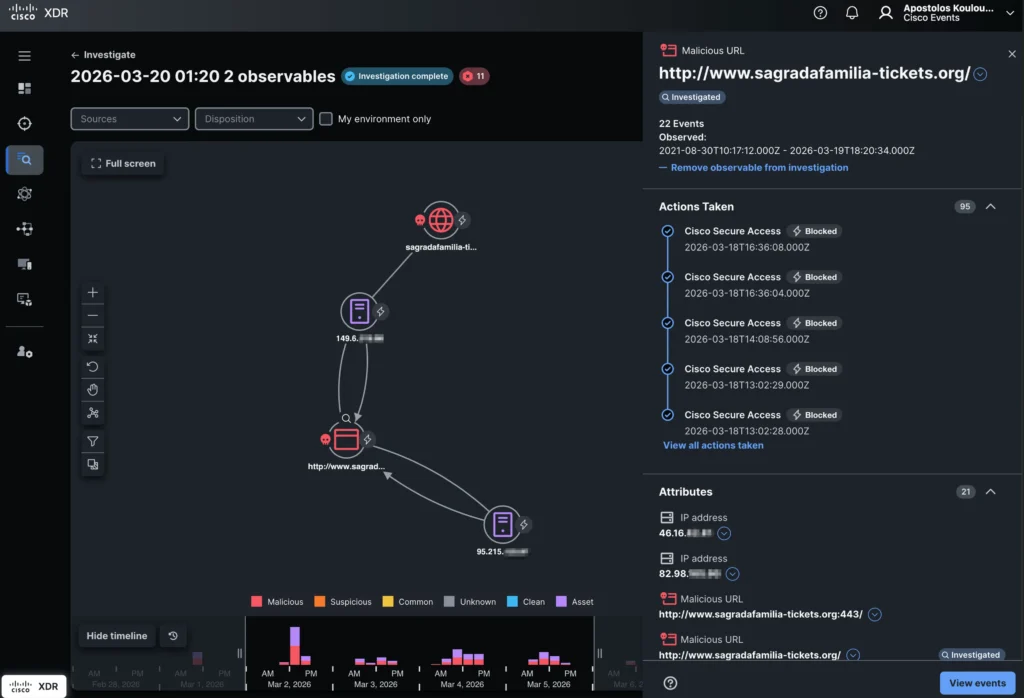
While Secure Access was enforcing only at the domain level, with XDR Investigate we could correlate logs from both Secure Access and the FTD 6160 firewall to provide further information, like the exact URLs users attempted to access, appearing as Attributes on the right-hand bottom of the image above.
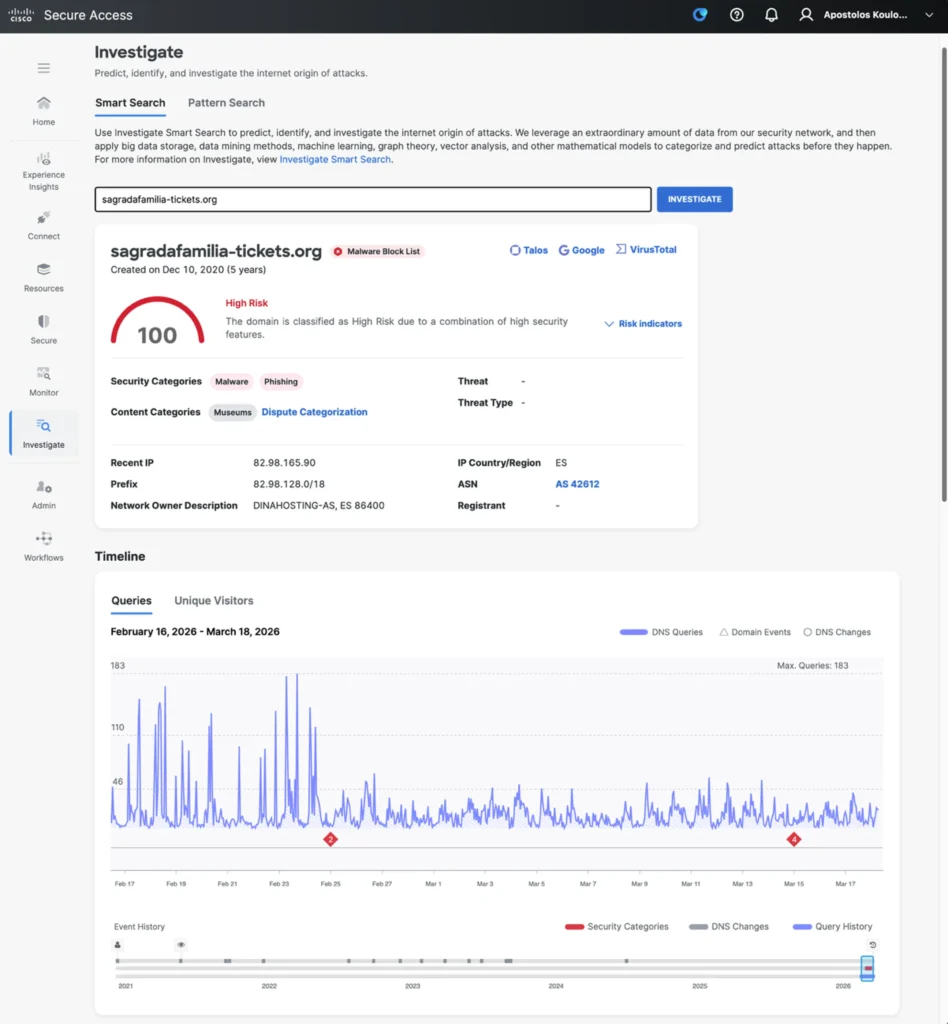
Secure Access Investigate, as appearing above, provides real-time actionable threat intelligence by analysing global data from the Secure Access network using AI to detect, score, and predict emerging threats. It allows security teams to proactively uncover malicious infrastructure (domains, IPs, ASNs) and accelerate incident investigation through API-driven, high-context data enrichment.
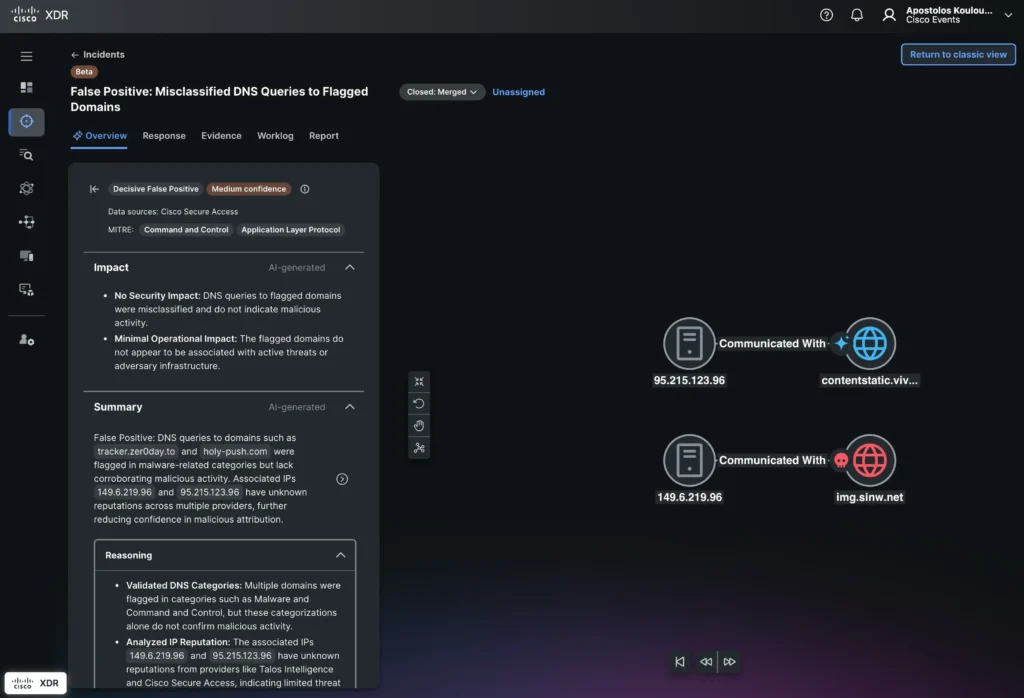
XDR can then correlate events further to provide more Incidents which are not as obvious as the above phishing event. Its AI-powered incident analysis (appearing above) provides AI-generated Classification, Impact, and a Summary including the Reasoning, Evidence and Detections for every incident. The additional AI-generated Analysis and Recommendations are invaluable for the integrations with Secure Access and Splunk ES to automate responses for every incident, while they facilitate escalations to senior security analysts when further manual action is required. In this specific case, XDR classified this incident as a potential false positive with medium confidence. Based on that, the SOC team can prioritise other incidents of higher priority.
Concluding
The AI-powered Security and Network Operations Center (S/NOC) at Mobile World Congress 2026 demonstrated Cisco’s commitment to leveraging cutting-edge technologies to secure and optimise large-scale, high-profile events. By integrating advanced solutions such as the AI-ready Secure Firewall 6160, Cisco Secure Access, Cisco AI Defense, Splunk Enterprise Security, and Cisco XDR operating all together as a single platform, the S/NOC provided comprehensive, multi-layered security that proactively blocked threats, including phishing campaigns, and delivered actionable insights through AI-driven analytics and correlation.
This deployment highlighted the power of combining AI, automation, and unified security telemetry to enhance threat detection, investigation, and response in real time, while also enabling granular control over AI application usage. The event underscored the importance of a holistic, AI-enabled security architecture that not only protects critical infrastructure but also educates and innovates to stay ahead of evolving threats in complex environments with diverse user populations.
Check out the lessons learned from the Event SOCs we deploy around the world, with the white paper and latest blogs.
We’d love to hear what you think! Ask a question and stay connected with Cisco Security on social media.
Cisco Security Social Media





