Healthcare costs are rising globally and making it increasingly difficult for patients to get the care they need. In the Netherlands, one very specific non-profit organization, VECOZO, was founded to maintain cost control in the Dutch Healthcare sector. VECOZO operates the national portal for data exchange (entitlement check and billing and other services) between healthcare providers and insurers.

Challenge: Network Insight Needed to Meet New Demands
In 2016, VECOZO processed over two billion digital messages across 30 services with 42,000 connected health providers (118,000 users) and processed digital invoices totaling €69 billion. As customers across the care chain demanded more access, VECOZO ran into a steep rise in new application needs and increased network traffic. A new IT model was needed. Key requirements included faster time to market and 24/7 uptime.
“Building out infrastructure could take many weeks depending on our specialists’ availability,” explains team leader, André Beerendonk. “Our services must run with zero interruption, but we had no real network insight. That made it harder to ensure uptime and control the user experience due to mission critical applications running on top of its IT infrastructure.”
VECOZO needed a new infrastructure solution with minimal cost increase to maintain business continuity.
The Solution
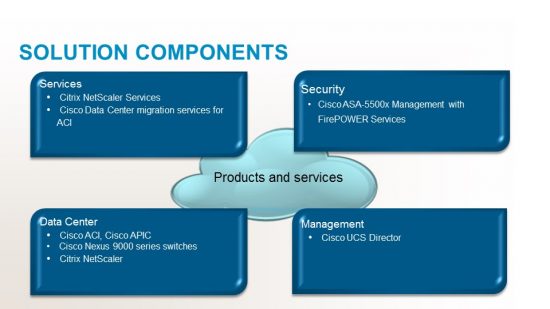
To meet the growing demand for applications and the network loads in its data center, VECOZO chose to deploy a joint solution based on Cisco Application Centric Infrastructure (Cisco ACI™) and Citrix® NetScaler as a next generation foundation. Spanning two data centers this joint solution combines Cisco and Citrix capabilities to enable rapid application deployment and services integration onto multi-tenant networks. Cisco ACI with Citrix NetScaler helped VECOZO boost application availability and performance through seamless integration of Citrix NetScaler’s programmable fabric with Cisco Application Policy Infrastructure Controller.

Deploy Apps faster with greater security and availability
For the highest levels of protection, VECOZO added Cisco next-generation firewalls, collapsing multiple security layers into one. In addition, through Cisco UCS Director integration with ACI, end users get a seamless experience for application deployment and orchestration.
Outcomes: Achieving 50% More Without Increasing Headcount
VECOZO is reaping the rewards of a fully programmable stack, achieved integrating Cisco ACI’s Layer 2-to-3 and NetScaler Layer 4-to-7 fabrics. This has made a profound difference. Applications are deployed with greater security and reliability—and up to five-times faster. Now they guide the network, rather than the other way around. Unlike before, VECOZO has a robust process to support compliance and can pull up reports and network charts on the fly. Total cost of ownership is lower, thanks to a smaller and greener data center footprint. The business is easier to manage with the elimination of operational silos and predictable IT costs.
“Service creation no longer depends on specialists. Pretty much anyone here can do it with minimal effort,” says Beerendonk. “As a result, we’ve been able to grow our infrastructure and services by 50 percent with the same headcount thanks to Cisco ACI and its partner ecosystem.”
VECOZO has been able to deliver new services with the efficiency gained. For example, by enabling healthcare providers to combine several medical treatments into one declaration, while also extending contract negotiations between healthcare providers and insurers.

Meet user needs and improve their experience
Counting on Cisco ACI Ecosystem for Stress-Free Migration
“The commitment and vision shown by Cisco was unmatched. With pre-validated designs, jointly developed between Cisco and Citrix as strategic partners, we were confident the deployment would be fast and reliable,” says Beerendonk.
“Our strategy was to simplify and automate everything,” adds ICT architect, Igor van Haren. “Cisco Services really helped. They shared valuable expertise and tools, helping us accelerate and complete the migration in just four months. Key steps, like ensuring proper documentation, cut down testing requirements by 90 percent.”

Accelerate and de-risk migration project
Products and Services Deployed
Results
- Grew infrastructure and services by 50% without increasing staff or cost
- Increased IT performance with greater reliability and up to 5X more speed
- Improved security and compliance at lower total cost of ownership
Relevant links:
www.cisco.com/go/customerstories
www.cisco.com/c/en/us/solutions/data-center/aci-ecosystem/index.html