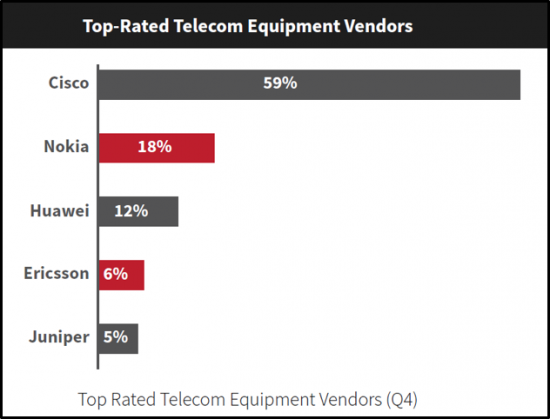
ACG Research, a well-known and respected analyst and consulting firm in the networking and telecom space, recently published a study of decision makers and influencers in companies across the globe who purchase various types of telecom equipment from vendors Cisco, Nokia, Huawei, Ericsson and Juniper.
I’m pleased to say that Cisco was the top-rated telecom vendor by a huge margin and number one in vendor performance. We also ranked highest or second-highest in reputation, innovation, quality, product features and performance, end-to-end solution, thought leadership, financing and sales team quality.
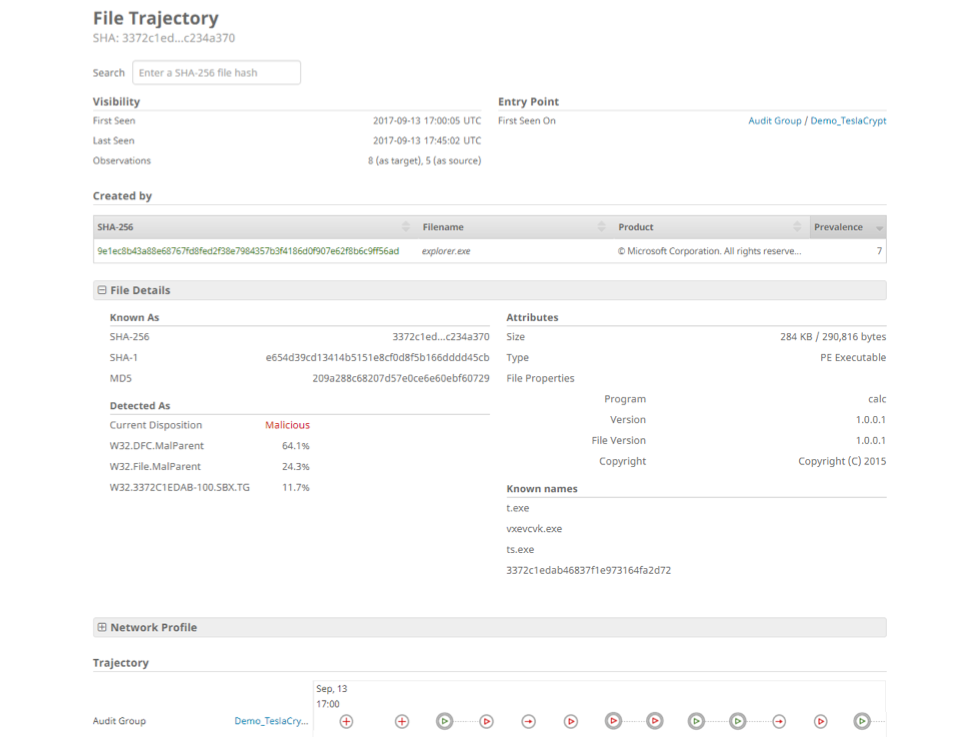
Figure 1: ACG Research, Telecom Vendor Equipment Selection 2017
We take great pride in being applauded for the following attributes:
- High-end expertise in security solutions
- Robust and high-quality networking equipment
- Innovation
- Product features and after-sales services are up to the mark
We also appreciate being described in the report findings like this:
“Cisco is the global service provider for cloud solutions and considered extraordinary in providing security & networking solutions. Robust and high-quality equipment with great service quality are the main reasons. Confident about its approach toward the satisfaction of its customers.”
It’s nice to be recognized for the work we’ve been doing to transform Cisco’s Service Provider Business over the past year. I’d like to share with you some of the ways we are taking back leadership in the Service Provider space:
Leading routing platform:
- Market-leading density in a 100GE routing platform (Cisco NCS 5500).
- Leading the charge toward network operations modernization with model-driven interfaces, OpenConfig, and streaming telemetry with Cisco IOS XR.
- The most flexible universal gateway (Cisco ASR 9000), bridging networks of today with those of tomorrow.
- Cisco Access Solutions deployed at more than 200 operators, across more than 75 countries, with over 1 billion mobile subscribers.
- Driving innovations in Segment Routing to help carriers, including Telefonica, COLT, and Softbank, offer new and differentiated network services. See blog on SR here.
Leading automation platform:
- Broadest portfolio (Network Service Orchestrator, Virtual Topology System, WAN Automation Engine, EPN Manager) delivering automation across the network.
- Foundation built upon high fidelity of network telemetry and collection, with open source contribution.
- Deploying closed-loop automation in some of the world’s largest service delivery networks.
- Industry’s most advanced and flexible service orchestration platform. More than 100 customers have adopted Cisco Network Services Orchestrator (NSO) technology including AT&T, Deutsche Telekom, Equinix, Level 3, NTT DOCOMO, SoftBank, Telecom Italia, Telefonica, Telstra, and Vodafone Hutchison.
- Work in multi-vendor environments with the industry’s broadest set of proven orchestration interoperability capabilities, spanning over 50 network equipment vendors and up to 100 device models today.
- Proven to automate more than 60 to 70 percent of customer operations workflows:
-
- 70 percent operational efficiency increase
- 60 percent reduced time to revenue with new services implemented in days /minutes
- The market has voted Cisco NSO as the clear market leader in the LSO (Life Cycle Services Orchestration) & Next Gen OSS space according to a recent survey by SDxCentral.
Leading next generation cable access with fiber deep and Remote PHY:
- First to market with end-to-end Remote PHY solution, Cisco Infinite Broadband.
- First to market with automation for Remote PHY, Cisco SmartPHY Automation.
- Leading the industry with Cable innovation such as Full Duplex DOCSIS 3.1 and Cloud Native virtualization for the CMTS
Leading data center interconnect:
- #1 market share leader in small form factor DCI (ACG Research). In fact, Cisco is growing faster than the market itself!
- “Solid financials, a growing client base in DCI, a focus on packet optical, and a good reputation for service and support, nudge Cisco over the line into the Leader category this year” – IHS Markit.
- #2 in modular market segment ranked by Cignal AI.
Leading optical and optics:
- Top rankings by ACG Research for ease of integration and thought leadership in optical for Cisco.
- Ranked highest for innovation in vendor scores by purchase criteria – ACG Research
- #2 market share in Metro Optical – another very fast growing segment of the market – ACG Research.
- Founding member of the QSFP-DD industry consortium seeking to drive down the cost, space, and power of 100G+ optics with QSFPP-DD form factor.
Leading mobile packet core and 5G:
- Market share leader for Evolved Packet Core (25 percent per Synergy Research).
- More than 1 billion subscribers currently served on a Cisco packet core platform, including 300 million virtual subs.
- Active participant in multi-vendor trials leading to 5G with Intel, Samsung, Verizon.
Leading video in the cloud:
- Market leading Cloud DVR Platform.
- Leading end-to-end cloud IP video platform.
- 15 percent of video software market share (per Synergy Research).
- #1 market share in client software (per Synergy Research).
- #2 market share in content security (per Synergy Research).
- Awarded 250+ US patents, 340+ Non-US issued counterpart patents.
Leading in open source:
- Active participants in multiple working bodies including OpenStack, Open Daylight, OPNFV, others.
- More than 40+ Cisco Application Contributions to the Open Source Community.
- More than 28 open source products.
- Cisco VNF and Virtualization Ecosystem includes 21 active alliances and partners.
- Created an open-source project called Community ICN in 2017.
- Founding member of the Cablelabs-led OpenRPD open-source initiative for Remote PHY.
We have been executing a plan to be ranked number one in all areas that are important to our customers. Stay tuned as we continue to lead the disruption in the industry with our cutting edge technology innovations so service providers can reduce cost and complexity, grow revenue, and secure their networks.
Click here to see me “On the Hot Seat” with Ray Mota of ACG Research talking about the industry transformation taking place today.