It is with great admiration and fondness that I write this blog about my colleague John Chapman’s induction into the 2017 class of Cable Pioneers, during the SCTE Cable-Tec Expo, in Denver this week.
The Cable Pioneers is an organization that honors long-serving and accomplished executives in the industry. It began in 1966, with a group of 21 entrepreneurs, and has grown since then to over 700 men and women. (Click here to see a Multichannel News compilation of 50 Facts about the Cable Pioneers.)
I’d venture a guess that anybody who works on the IP-side of cable, and particularly those familiar with DOCSIS (Data Over Cable Service Interface Specification), knows John Chapman, or at least knows of his foundational and ongoing work to advance the depth and breadth of broadband communications.
We took the liberty of checking in with some industry luminaries about John’s role in the cable and broadband universe. Here’s what Tony Werner, cable pioneer and President of Comcast Technology and Product, has to say: “John has a unique knack for innovating in the precise directions the industry needs — years before those needs arise. He’s done it over and over again, even before the beginnings of DOCSIS. Plus, he’s not only a ‘dream it up’ guy — he’s also a ‘get it operationalized’ guy, which is always harder than it looks.”
Mark Bell, Vice President of Industry affairs for NCTA – The Internet & Television Association, notes that “John’s longstanding commitment and numerous contributions to the NCTA Technical Papers is immeasurable. Serving countless terms on the selection committee as our DOCSIS ‘spirit guide,’ John’s unique vision into the trajectory of cable’s broadband platform — as one of its creators — often led to vigorous debate, selection and publication of several technical papers on the topic.”
“As one of the most distinguished and frequently published authors from the series,” Bell continues, “John himself, along with distinguished co-authors, has contributed more than a few peer-acclaimed written works to the industry’s archival body of technical literature — including one that ‘weighed in’ at 182 pages. Bonus: He’s also one of the nicest brilliant minds in the business.”
John was nominated by Rouzbeh Yassini, CEO of YAS Capital Partners an acknowledged “father of the cable modem,” and Nick Hamilton-Piercy, former CTO of Rogers, in Canada. They note several major accomplishments, attributable to John:
- He founded the CMTS business at Cisco in 1996
- He’s a prolific author, with more than 100 patents issued and pending, related to DOCSIS
- He’s contributed meaningfully to the DOCSIS spec since its first iteration (DOCSIS 1.0) through to DOCSIS 3.1, Full Duplex DOCSIS, and now, at this year’s Expo, mobile backhaul for DOCSIS
Beyond that, he’s a 7th Dan in Tae Kwon Do, a 5th Dan Black Belt in Hapkido, and a blue belt in Brazilian Ju-Jitsu. He’s taught martial arts to adults and children for over 30 years. Which speaks volumes about his intensity, fortitude, and respectfulness.
John will be inducted into the Cable Pioneers at a dinner event on Tuesday, October 18, at the Brown Palace Hotel. Our deepest congratulations, John! You are an industrial treasure, and we are lucky to have you on our team at Cisco.


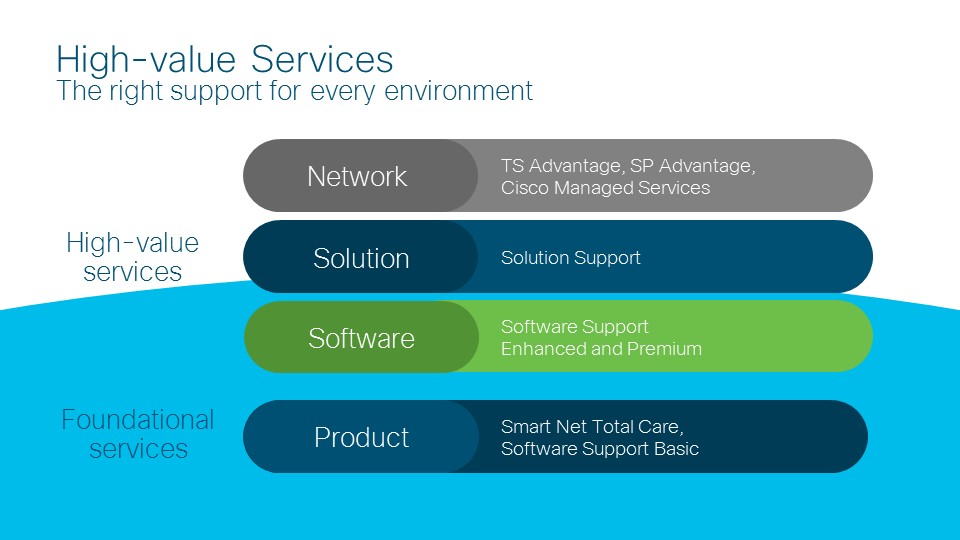
 the right skills). Rather, they allow IT to spend more time on strategy, innovation, and working with lines-of-business to support business priorities. And by combining our trusted experts with predictive insights from AI, we can help customers take their operations to the next level. These new services help our customers achieve the business outcomes they desire, and provide even more value through our partners for their customers. Both of these offerings are available today.
the right skills). Rather, they allow IT to spend more time on strategy, innovation, and working with lines-of-business to support business priorities. And by combining our trusted experts with predictive insights from AI, we can help customers take their operations to the next level. These new services help our customers achieve the business outcomes they desire, and provide even more value through our partners for their customers. Both of these offerings are available today.