S’mores by the campfire. Cocktail hour and sunsets. Your favorite meal cooked by mom. People, processes, and technology.
What do these all have in common?
Sometimes the classics are timeless because they just work. Resilient. Always a go-to. Beautiful in their simplicity.
As an ex-managing IT consultant, the classic IT framework of People, Processes, and Technology is simple yet profound. Faced with any IT “requirement,” use that framework and ask the question “Why?” five times. 95% of the time you realize the “requirement” is some bogus legacy need.
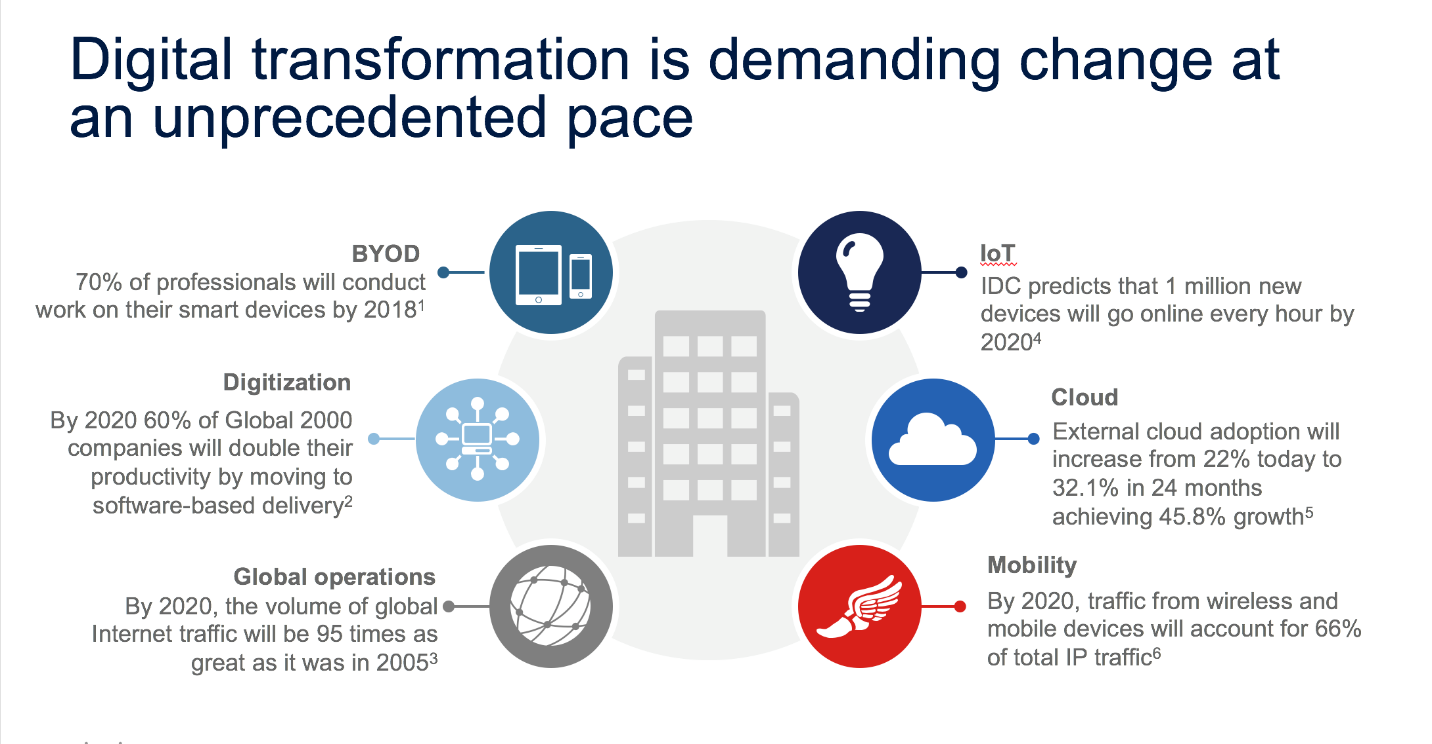
This axiom is more important than ever in today’s accelerating multicloud world. Yes, the cloud is a driving force behind most of the digital transformations organizations are undertaking. However, that’s just the technology. Scarily enough, that’s the easy part!
To optimize for success, IT can’t just transform the business with new technology. Instead, it needs to transform IT itself. IT must undertake a Hybrid IT transformation. And to succeed, yes you knew it was coming, IT need to manage change across people, processes, and technology holistically.
Hybrid Cloud vs. Hybrid IT

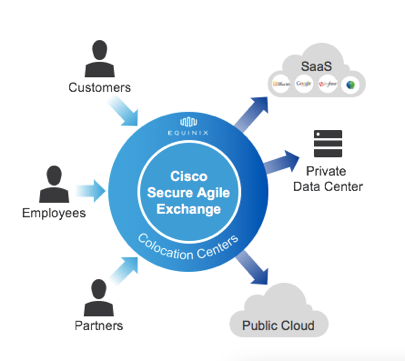
In today’s multicloud landscape, no one cloud fits all. Yes, you may be using AWS and/or an OpenStack Private Cloud. Leveraging SaaS heavily. Exploring containers and DevOps delivery. With a plethora of cloud solutions in every customer environment, we are in a Hybrid Cloud era.
According to Gartner, by 2018 96% of organizations using cloud services will also be using cloud services. However, ask 10 people and you will get 10 definitions for Hybrid cloud. To level set according to Gartner:
Hybrid Cloud: The coordinated use of two or more cloud services.
Hybrid IT: A trusted broker and provider for all IT services — cloud and non-cloud — from many different providers and styles.
And if this Hybrid Cloud definition is too simplified, it really includes these 5 Hybrid Infrastructure approaches:
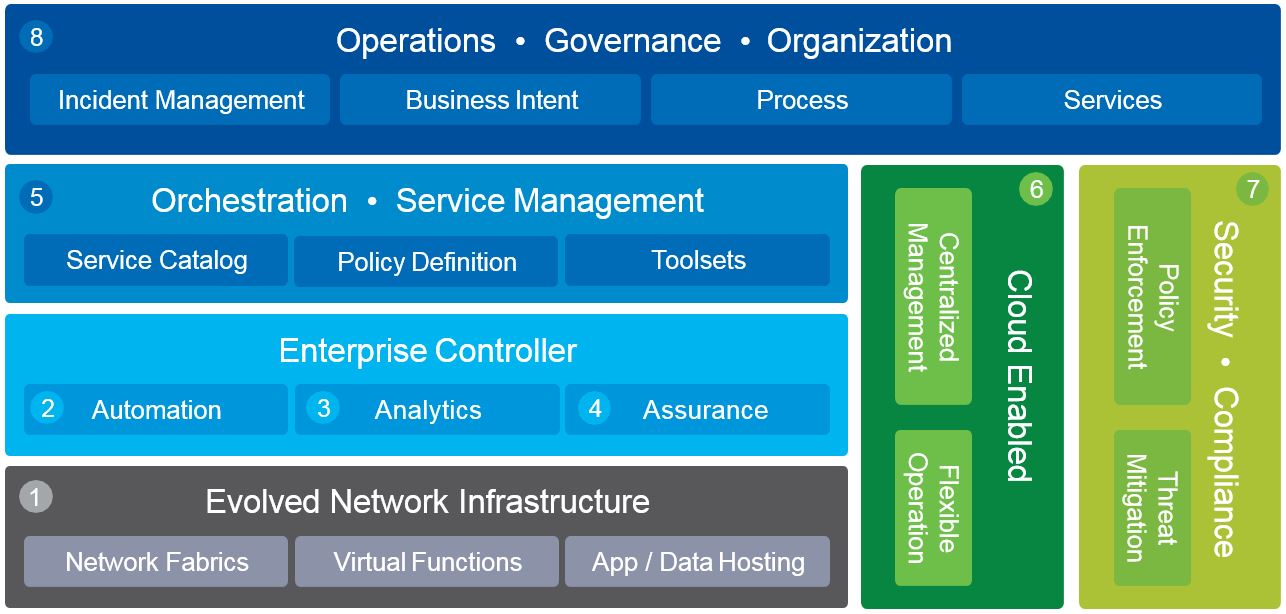
Hybrid Management: Governance, operation and brokering across silos
Hybrid Infrastrucure: Integration of infrastructure hardware and utility components (only) between silos
Hybrid Orchestration: Composing a service across silos supporting coordinated workload provisioning and motion
Data Integration: Integrated data across applications and operating silos
Hybrid Applications: Integration of applications and application middleware across silos through APIs and service interfaces
So based on this, ‘what’s your Hybrid Cloud strategy’? That’s a good question. However, a great question is ‘what’s your Hybrid IT strategy?’ How are you integrating and governing all of this multicloud usage to simplify, secure, and transform your business?
The Cloud Gap
So even if you know where you want to go (aka your cloud strategy) that is only the beginning. According to research conducted by IDC with over 11,000 IT professionals, only 3% of organizations have optimized cloud strategies! Yes, 3%. And even more surprising (or shocking) 69% of organizations do not have mature cloud strategies in place.

This data reflects many of the challenges with today’s IT landscape. Managing both traditional and cloud applications. Automating the Data Center. Multicloud security. IT-as-a-Service. DevOps Environments. Application lifecycle management. The IT to do list is never ending.
And to tackle all these areas, IT must overcome skillsets gaps and a shortage of cloud talent. . . And ohh yea, you have less budget!
Where does one begin?
Meet your neutral Change Agent: Cisco Cloud Advisory Services
Change is hard. Good luck trying to tackle org redesign and changing culture alone.
At Cisco, we have helped our customers adopt new technology with Professional Services for 30 years. However, we are seeing a huge growth in demand from our clients for Cloud Advisory Services. Our clients need a trusted partner in helping them manage the “Cloud Gap” across clouds.
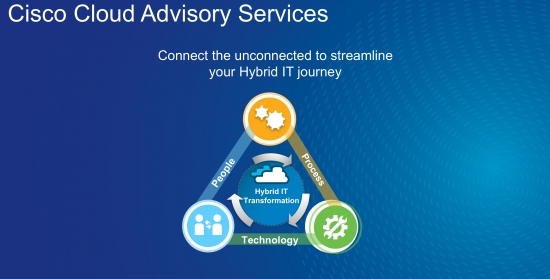
Cisco Cloud Advisory Services is a primely positiond to be your trusted multicloud advisor since we are cloud neutral. We have no public cloud of our own to lock you into. Being cloud neutral we can leverage our integration, networking, and security roots to optimize your multicloud strategy and accelerate your Hybrid IT transformation. Our experts have designed and built some of the world’s largest clouds.
So if you are like our customers you may need help with a:
- Hybrid Cloud Business Case
- Cloud Transformation Strategy for DevOps or ITaaS
- Application Migration Strategy
- Cloud Skillset Blueprint
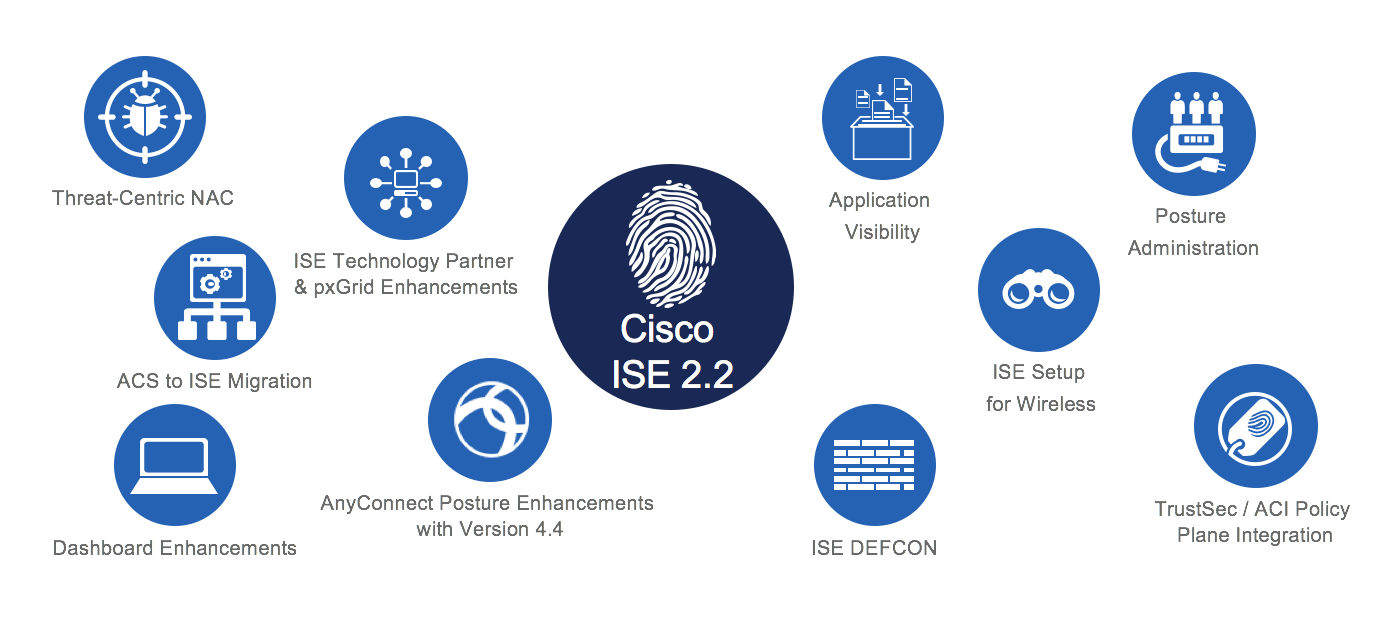
- Multicloud Security Blueprint
- Technology assessment
Yes we are technology nerds, but when analyzing your Hybrid IT strategy think about how people, processes, and technology will either make you or break you. And keep in mind Cisco Cloud Advisory Services is here simplify, secure, and transform your Hybrid IT!
To learn more:
If you are at Cisco Live Berlin stop by the Cloud or Services booth to meet with our Cloud Experts.
Curious about a Cloud Strategy Workshop? Stop by the Cisco Business Cloud Advisor (BCA) booth to receive a personalized summary regarding your cloud environment and enter to win daily prizes!
- Cloud Sessions at Cisco Live Berlin
- Cisco Cloud Portfolio Overview Website
- Cloud Professional Services Website
- Cisco Business Cloud Advisor Website
- Get your personalized Cloud Adoption summary (enabled by IDC)