Today, cities are experiencing population growth and socioeconomic and political shifts that change the requirements necessary for protecting residents, physical infrastructure and city data. Public safety is a highly visible metric for which city officials are judged on quality of leadership and as a platform for reelection. But the ability to protect and serve the community also contributes to attracting trade, investment, commerce and talent, which are all vital to quality of life. Now, more so than ever, city and community leaders are looking for innovative ways to address ever-evolving challenges, while keeping people safe and maintaining sustainable, successful growth.
There are many factors and stakeholders to consider when transforming public safety and security. Different agencies, departments, critical infrastructure elements, businesses and people are greatly affected by changes in attempts to improve public safety. And from a technology perspective, the matter can be further complicated. A comprehensive approach to a public safety solution is necessary for proactive management and effective response.
We recently announced the Smart+Connected Digital Platform, a unifying, cloud-based tool that provides a centralized mechanism for addressing the need to manage streams of data in a reliable, secure and effective way. This allows cities to capture, analyze and share data across various organizations, across sectors and with residents, visitors and businesses—opening up new possibilities to enable each city’s unique digital transformation vision.
https://www.youtube.com/watch?v=BN-NfmC_BuQ&list=PLEE1CB50148EBA975&index=1
With the Smart+Connected Digital Platform, Cisco and its partners are changing the game. The collaboration with the certified public safety ecosystem partners brings new and improved capabilities to be integrated into the platform for both unique and cross-domain analysis. The platform ecosystem is robust and growing. Deployments from around the world are including global and local partners per the call of and catered to the particular goals of each city.
The platform integrates smart video surveillance, enables automated alerting and connects agencies for faster and more effective emergency response. This helps to reduce crime, optimize resources and allows public safety officials to proactively manage threats and better coordinate in wake of disaster. Predictive, cross-correlated analytics help to better plan, heighten situational awareness and enhance collaboration in a traditionally fragmented market. Safer streets and neighborhoods mean residents, local businesses and visitors all have an improved community experience that contributes to the overall attractiveness and well-being of the city. For example in India, Jaipur Development Authority (JDA) is transforming its public safety apparatus to move further toward its smart, digital city vision.
Already, the feedback from customers and partners is powerful. Not only do these innovations make it easier and more affordable for cities to approach innovative change, but the true and lasting positive impact to people and communities is what makes it all worthwhile.




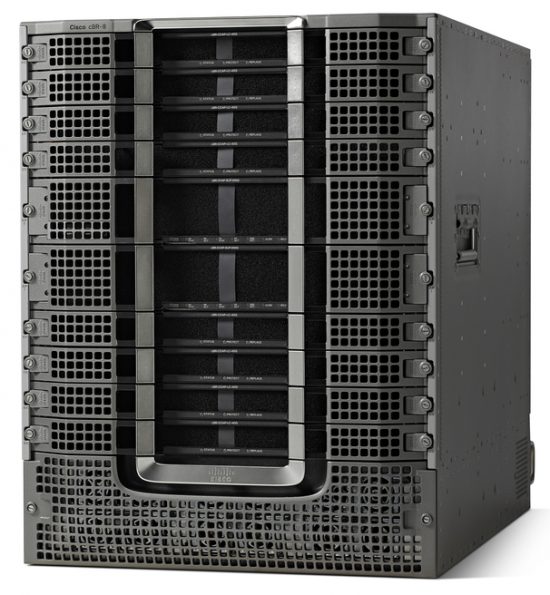 We often get asked what we mean by claiming that the Cisco cBR8 is designed from the ground up for DOCSIS 3.1 and beyond. In fact, there is a lot of confusion out there with regard to different hardware architectures in use by the various CCAP vendors. Cisco’s cBR8, introduced in 2015, was designed in-house, based on our decades of expertise in architecting carrier class platforms with 10 or more year lifespans.
We often get asked what we mean by claiming that the Cisco cBR8 is designed from the ground up for DOCSIS 3.1 and beyond. In fact, there is a lot of confusion out there with regard to different hardware architectures in use by the various CCAP vendors. Cisco’s cBR8, introduced in 2015, was designed in-house, based on our decades of expertise in architecting carrier class platforms with 10 or more year lifespans.